Android ransomware spreads itself via SMS
The security firm AdaptiveMobile has discovered a new variant of Koler ransomware is capable of self-replication via SMS messages.
 A new strain of the Koler Android ransomware is threatening the mobile industry, the new variant spreads itself via SMSs and holds the victim’s device phone hostage until a ransom is paid.
A new strain of the Koler Android ransomware is threatening the mobile industry, the new variant spreads itself via SMSs and holds the victim’s device phone hostage until a ransom is paid.
The Koler ransomware were detected by experts at Kaspersky Lab in July, the researchers issued a report on the malware explaining that it was targeting targeting both Android devices and desktop browsers. The first variant of the Koler Android ransomware was observed in May when the Trojan was spread through certain pornographic websites under the guise of legitimate apps.
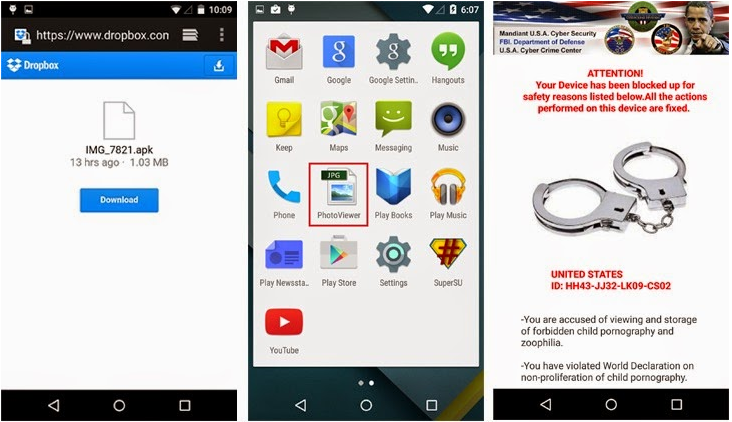
Implementing a classic extortion scheme locks the victim’s device display and then requests money from victims. The malware displays fake notifications from law enforcement agencies that accuse victims of viewing and storing child pornography. Security experts from mobile security firm AdaptiveMobile have discovered a new variant of the mobile malware Worm.Koler that allows the malicious code to spread via SMS, sending shortened bit.ly URL.
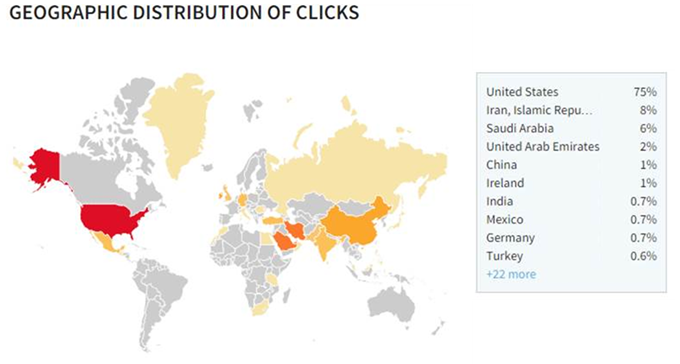
The security firm has already observed thousands of messages from hundreds of infected phones, mainly located in the US.
The attack scenario is very interesting, the Koler worm sends an SMS message with a bitly link stating that an account with the user’s photos has been created. To spread itself, the koler worm first sends an SMS message to all contacts in the mobile’s address book with a text stating:
The victim is re-directed to a DropBox folder containing a “PhotoViewer” app trojanized with the malware. Once installed, the maclious app locks the victim’s devices requesting the payment of a fee to unlock it.
The experts noticed that the code of Worm.Koler is internationalized, it is able to display localized messages to victims. As usual I strongly suggest to infected users to not pay any ransom because there is no guarantee to free the mobile from the threat. Another risky behaviour for mobile users is the enable the “Unknown Sources” option in Android device security settings menu. Enabling the option users can install applications from unknown sources, a behaviour that could allow malicous code download from unofficial stores to infect the device.
In September many owners of smartphones, Ukrainian mobile operators subscribers became victims of similar SMS-virus. Koler does not encrypt users’s files, for this reason it is easy for users to eliminate it from infected devices. Below the instructions to remove the malware:
- Reboot the mobile device in the “Safe Mode“
- Remove the malicious ‘PhotoViewer‘ app using standard Android app uninstallation tool
Axarhöfði 14,
110 Reykjavik, Iceland














