CTB-Locker is the newest crypto malware
From late 2013 through the first half of 2014, CryptoLocker malware was a major concern for many businesses and individuals.
 In June of 2014, the FBI was able to successfully disrupt CryptoLocker, along with Game Over Zeus, but according to the figures in their legal complaint against Evgeniy Bogachev, not before his malware had encrypted more than 230,000 computers, with 120,000 of them in the United States.
In June of 2014, the FBI was able to successfully disrupt CryptoLocker, along with Game Over Zeus, but according to the figures in their legal complaint against Evgeniy Bogachev, not before his malware had encrypted more than 230,000 computers, with 120,000 of them in the United States.
The second major Crypto Malware was CryptoWall. In Malcovery's 3rd Quarter malware report, there were documented 24 separate spam campaigns that resulted in CryptoWall infections. But that number declined sharply in our 4th Quarter Malware Report, with only 10 CryptoWall spam campaigns in October, only 4 in November, and none at all in December.
Today we may have seen the beginning of the Next Wave of Crypto Malware being delivered by spam. Malcovery Threat analysts Neera Desai and Brendan Griffin called attention to the new threat, which was delivered in a series of spam messages claiming to be some form of faxed document. There were many variants of the spam subject, including:
- Fax from RAMP Industries Ltd
- [Fax server]= +07955-168045
- [Fax server] : LPY.5705BBC7.1118
- Incoming fax, NB-112420319-8448
- New incoming fax message from +07829 062999
- [Operational Support Ltd] Fax transmission=U2W9MABD921532EC5
The messages themselves contained a very simple text explaining that your inbound fax was attached.
No.: +07434 20 65 74
Date: 2015/01/18 14:56:54 CST
Pages: 5
ID: TVZ.79483B95A.8086
Filename: headband.zip
--
Peter Brett Associates
Eun Gransberry
The attached file used a seemingly random dictionary word. Some of the .zip files that Malcovery observed including:
- banjoes.zip
- denudement.zip
- disgruntled.zip
- facto.zip
- headband.zip
- ...
- tutty.zip
- woodworking.zip
Many anti-spam tools now unzip .zip attachments to check for the presence of an .exe within the .zip. This spam attempts to avoid that trip by containing a .zip file, which also contains a .zip file, which includes a .scr file.
No two files that we reviewed had the same malware hash. One of the many ways the anti-virus industry inflates their numbers is to count each unique hash as a separate file. Malcovery prefers to refer to the malware by the campaign. Since every .scr file was unique, we could claim as many new "malware variants" as we chose to review spam email messages, however that adds no meaningful value since each of these samples performs the same action and is structurally identical, if not actually identical.
The ".scr" file, which will be named with the same dictionary word as the .zip file from which it was extracted, is a downloader known as Dalexis. (For Malcovery customers, see ThreatHQ reports 2460 and 2486 for previous reports about the Dalexis loader.)
Dalexis performs a similar role to the more common UPATRE malware. Its job is to covertly download additional malware, unpack it, and execute it. In this case it does so by retrieving a file named "pack.tar.gz" from a variety of websites, such as:
- breteau-photographe.com / tmp / pack.tar.gz
- maisondessources.com / assets / pack.tar.gz
- pleiade.asso.fr / piwigotest / pack.tar.gz
- scolapedia.org / histoiredesarts / pack.tar.gz
- voigt-its.de / fit / pack.tar.gz
These files are not actually .tar.gz archive files, they are actually copies of the CTB-Locker malware that have been XOR'ed in a special way that Dalexis knows how to reverse. By passing through the network perimeter in an encoded format, the download is not scanned, since the file is not an executable or commonly known file type.
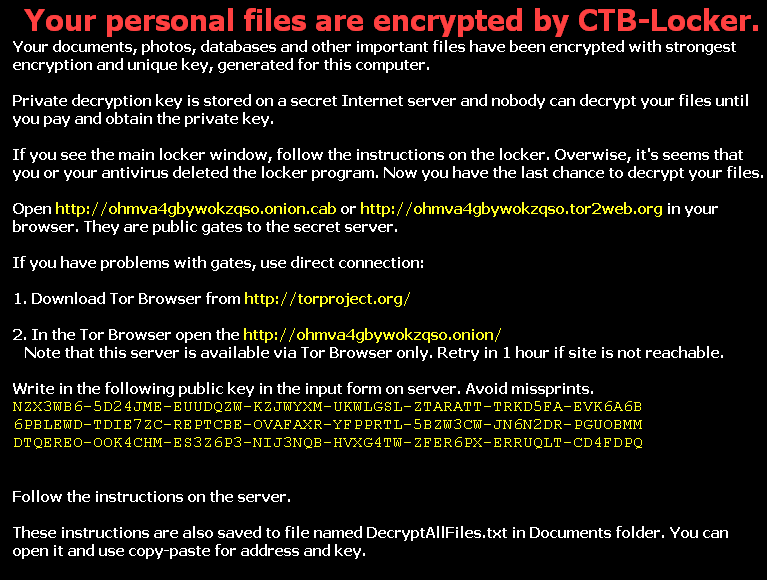
At that point, CTB-Locker takes over. CTB is an acronym for Curve Tor Bitcoin. Curve refers to the fact that the malware uses Eliptical Curve Encryption, which the author claims is the equivalent of RSA-encryption with a 3072 bit key. The first we saw CTB being described was by the malware blogger Kaffeine on his excellent blog "malware.dontneedcoffee.com" back in July 2014. At that time, CTB was primarily associated with the Angler Exploit Kit.
The author of the malware announced CTB to the criminal underworld in June, with a couple interesting points.
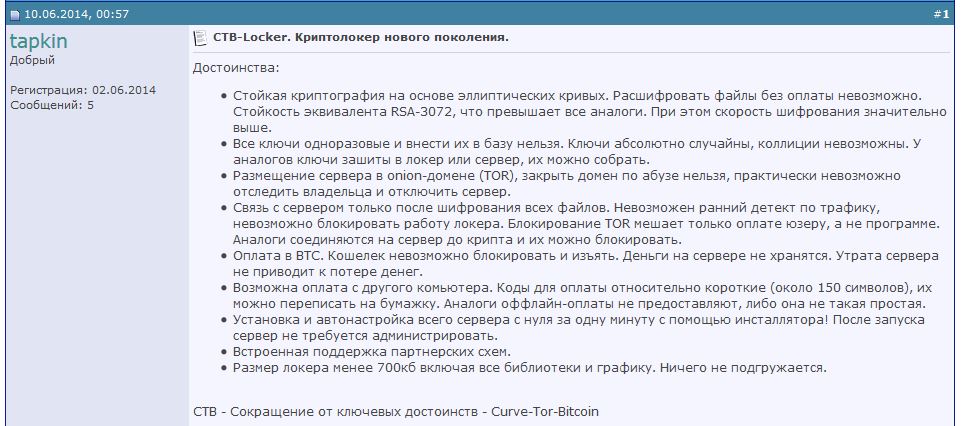
The criminal, who uses the handle tapkin, was offering his malware for $3,000, with a discount of 50% to the first purchaser. He also advertised that he had a plan for making it an Affiliate Program, meaning that a criminal could host CTB and other criminals could earn a commission by infecting people and having them pay the ransom.
We are not sure yet whether today's spam will be revealed to be part of such an affiliate program, or if this is just one of Tapkin's customers. We believe that the Angler Exploit Kit will continue to be used to deliver some forms of CTB-Locker, but expect that this will be the beginning of a long series of similar spam messages. The challenge however may be that the criminals find the TOR network requirement to be a barrier to their efforts.
Here is the sequence of events:
1. After CTB has been downloaded, it encrypts the files on the local machine. Many filetypes that have not been encrypted by previously Crypto Malware have been added, most interestingly, several extensions related to computer source code such as would be found on a programmer's computer.
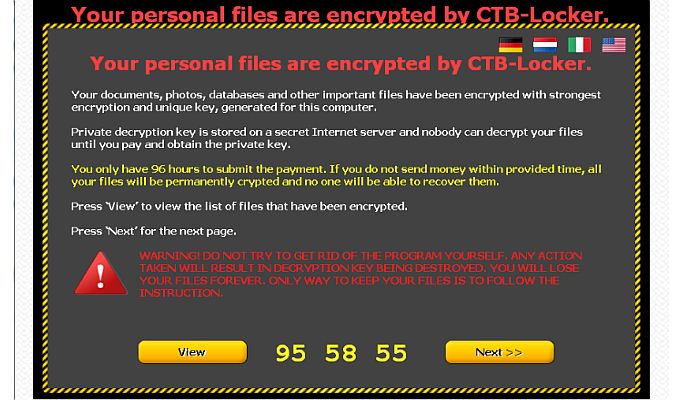
2. Once the encryption process is completed, the Count Down Begins!
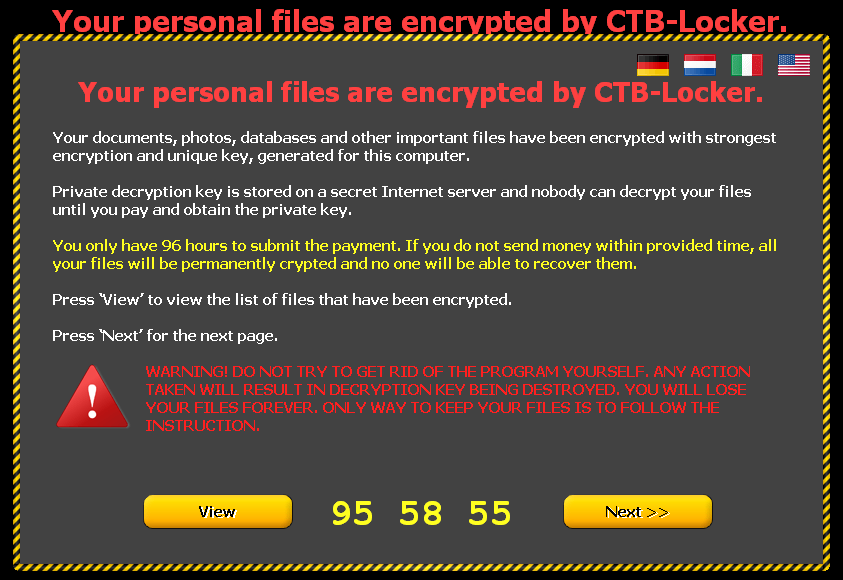
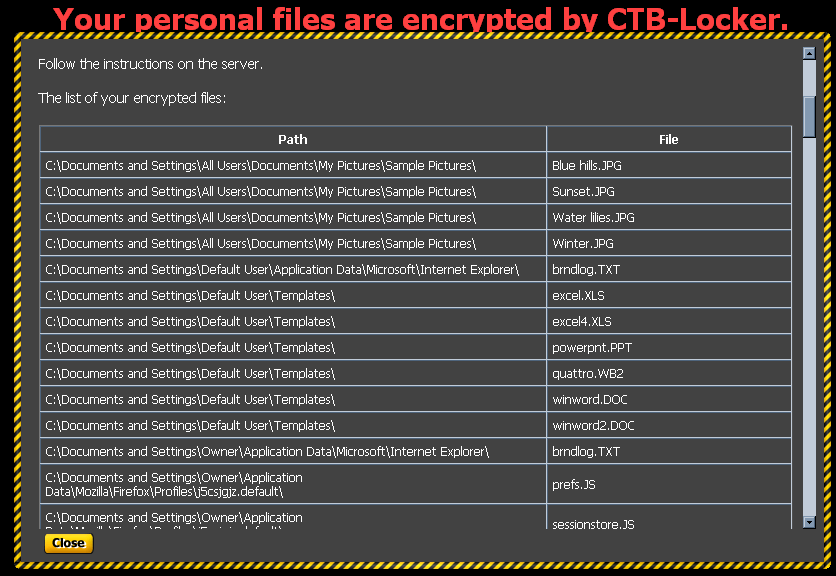
(2A). Choosing the "View" screen displays a list of the victim's encrypted files.
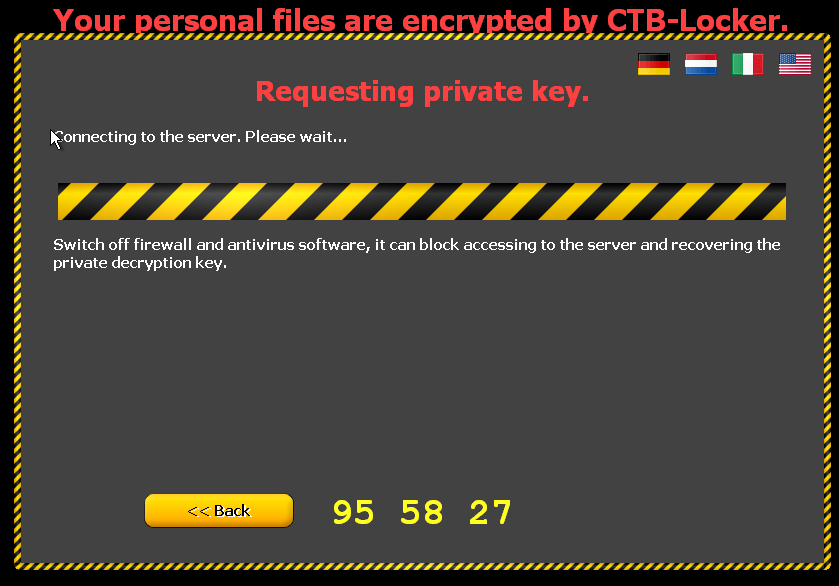
3. When the victim is ready to decrypt their files, clicking NEXT results in a request for the Private Decryption Key:
4. But of course they aren't going to give that to you for FREE!
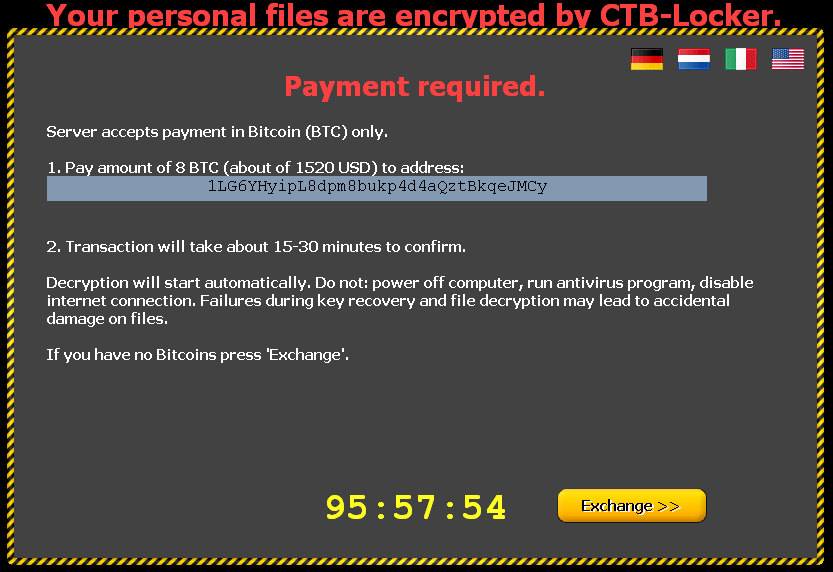
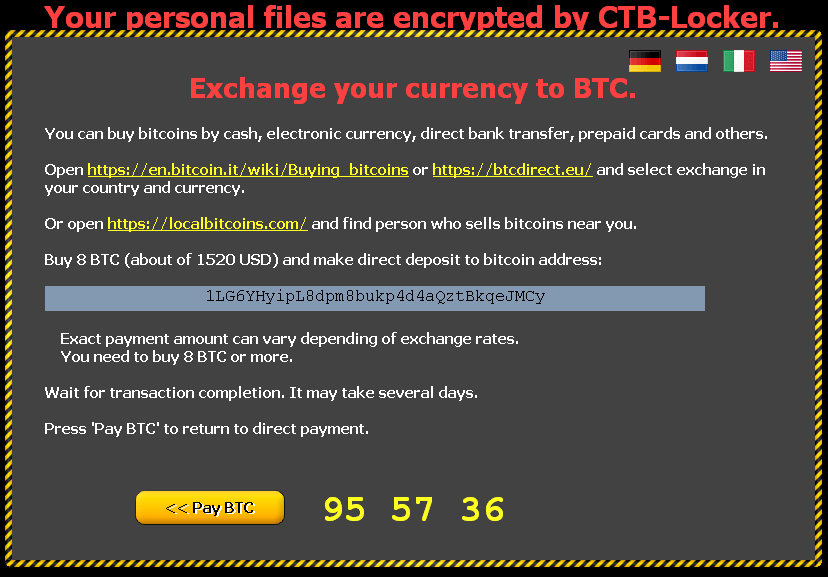
5. The only payment type they accept is BitCoin, but they offer several helpful links to educate the victim on how they can buy Bitcoins. The ransom is the highest price we've seen in Crypto Malware so far. This version asks for EIGHT BITCOINS, which they estimate at $1520 USD:
6. The addresses offered for contacting the criminal's website require the use of the TOR network. If you have TOR installed, you can use the ".onion.cab" address, or if you don't have TOR, you can use a "tor2web.org" gateway.
Axarhöfði 14,
110 Reykjavik, Iceland














