Hacking group expands espionage operation with new attacks
 A hacking operation has expanded its operations taking advantage of new tools - including the EternalBlue SMB exploit - to attack organisations across the Middle East for the purposes of surveillance and intelligence gathering.
A hacking operation has expanded its operations taking advantage of new tools - including the EternalBlue SMB exploit - to attack organisations across the Middle East for the purposes of surveillance and intelligence gathering.
Targets are mostly working in telecoms and transport and their surrounding supply chains - with IT software, payroll, aircraft services and engineering firms all targets during the last year. The operations of Chafer, an Iran-based targeted attack group have been detailed by researchers at security company Symantec, who note that since first being exposed in 2015, the group has expanded its surveillance and cyber attack operations.
Read more"Zealot" campaign uses NSA exploits to mine Monero on Windows and Linux servers
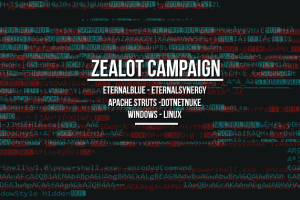 An aggressive and sophisticated malware campaign is currently underway, targeting Linux and Windows servers with an assortment of exploits with the goal of installing malware that mines the Monero cryptocurrency.
An aggressive and sophisticated malware campaign is currently underway, targeting Linux and Windows servers with an assortment of exploits with the goal of installing malware that mines the Monero cryptocurrency.
The campaign was detected by security researchers from F5 Networks, who named it Zealot, after zealot.zip, one of the files dropped on targeted servers. According to Maxim Zavodchik and Liron Segal, two security researchers for F5 Networks, the attackers are scanning the Internet for particular servers and using two exploits, one for Apache Struts and one for the DotNetNuke ASP.NET CMS, to get a foothold on unpatched machines.
Read moreInternal Kaspersky investigation says NSA worker’s computer was infested with malware
 The personal computer of an NSA worker who took government hacking tools and classified documents home with him was infected with a backdoor trojan, unrelated to these tools, that could have been used by criminal hackers to steal the US government files.
The personal computer of an NSA worker who took government hacking tools and classified documents home with him was infected with a backdoor trojan, unrelated to these tools, that could have been used by criminal hackers to steal the US government files.
The Moscow-based antivirus firm, which has been accused of using its security software to improperly grab NSA hacking tools and classified documents from the NSA worker's home computer and provide them to the Russian government, says the worker had at least 120 other malicious files on his home computer.
Read moreKaspersky says it obtained suspected NSA hacking code from U.S. computer
 Moscow-based antivirus software maker Kaspersky Lab said on Wednesday that its security software had taken source code for a secret American hacking tool from a personal computer in the United States.
Moscow-based antivirus software maker Kaspersky Lab said on Wednesday that its security software had taken source code for a secret American hacking tool from a personal computer in the United States.
In September, U.S. officials ordered Kaspersky’s products removed from government computers, saying the firm was vulnerable to Kremlin influence and that using the software could jeopardize national security. After that announcement, the Wall Street Journal reported on Oct. 5 that hackers working for the Russian government appeared to have targeted a National Security Agency (NSA) worker by using Kaspersky software to identify classified files in 2015.
Read moreRussian hackers reportedly stole NSA cyber defense material
 Russian hackers stole documents detailing how US agencies defend their networks against cyberattacks, how they breach foreign networks and the computer code they use to do so.
Russian hackers stole documents detailing how US agencies defend their networks against cyberattacks, how they breach foreign networks and the computer code they use to do so.
The stolen files were identified through Kaspersky security software used by an NSA contractor that had taken classified material from the NSA and saved it on his computer. The theft, discovered last spring, occurred in 2015 and those familiar with the incident told that having this information could help inform Russian officials how to protect their networks against the NSA and possibly how to break into US networks.
Read moreDistrustful U.S. allies force spy agency to back down in encryption fight
 An international group of cryptography experts has forced the US NSA to back down over two data encryption techniques it wanted set as global industry standards, reflecting deep mistrust among close US allies.
An international group of cryptography experts has forced the US NSA to back down over two data encryption techniques it wanted set as global industry standards, reflecting deep mistrust among close US allies.
In interviews and emails, academic and industry experts from countries including Germany, Japan and Israel worried that the U.S. electronic spy agency was pushing the new techniques not because they were good encryption tools, but because it knew how to break them. The NSA has now agreed to drop all but the most powerful versions of the techniques - those least likely to be vulnerable to hacks - to address the concerns.
Read moreThe Shadow Brokers return with the release of UNITEDRAKE exploit
 The ShadowBrokers have promised the release of NSA exploit UNITEDRAKE which remotely targets Windows machines to subscribers. This week, the threat group posted an update to the Monthly Dump service, which will now include two cache dumps every four weeks for subscribers.
The ShadowBrokers have promised the release of NSA exploit UNITEDRAKE which remotely targets Windows machines to subscribers. This week, the threat group posted an update to the Monthly Dump service, which will now include two cache dumps every four weeks for subscribers.
The changes have been made potentially as a means to drum up extra interest for cyberattackers, government groups, or vendors which have chosen to subscribe to the service to gain access to the stolen exploits and malware samples. The September dump includes a manual for UNITEDRAKE, modular malware which remotely targets Microsoft Windows machines.
Read moreHackers are using NSA hacking tool to attack hotels in Europe
 Russian-speaking cyberespionage group APT28, also known as Sofacy, is believed to be behind a series of attacks last month against travelers staying in hotels in Europe and the Middle East. APT28 notably used the NSA hacking tool EternalBlue as part of its scheme to steal credentials from business travelers, according to a report released Friday by security firm FireEye.
Russian-speaking cyberespionage group APT28, also known as Sofacy, is believed to be behind a series of attacks last month against travelers staying in hotels in Europe and the Middle East. APT28 notably used the NSA hacking tool EternalBlue as part of its scheme to steal credentials from business travelers, according to a report released Friday by security firm FireEye.
One of the goals of the attack is to trick guests to download a malicious document masquerading as a hotel reservation form that, if opened and macros are enabled, installs a dropper file that ultimately downloads malware called Gamefish.
Read moreNSA opens Github account — lists 32 projects developed by the agency
 The NSA — the United States intelligence agency which is known for its secrecy and working in the dark — has finally joined GitHub and launched an official GitHub page.
The NSA — the United States intelligence agency which is known for its secrecy and working in the dark — has finally joined GitHub and launched an official GitHub page.
The NSA employs genius-level coders and brightest mathematicians, who continually work to break codes, gather intelligence on everyone, and develop hacking tools like EternalBlue that was leaked by the Shadow Brokers in April and abused by the WannaCry ransomware last month to wreak havoc worldwide. The intelligence agency mostly works in secret, but after Edward Snowden leaks in 2013, the NSA has started opening itself to the world.
Read moreShadow Brokers threaten to unleash more hacking tools
 The hacking group that says data they released facilitated the WannaCry ransomware attack has threatened to leak a new wave of hacking tools they claim to have stolen from the US National Security Agency.
The hacking group that says data they released facilitated the WannaCry ransomware attack has threatened to leak a new wave of hacking tools they claim to have stolen from the US National Security Agency.
The so-called Shadow Brokers, who claimed responsibility for releasing NSA tools that were used to spread the WannaCry ransomware through the NHS and across the world, said they have a new suite of tools and vulnerabilities in newer software. The possible targets include Microsoft’s Windows 10, which was unaffected by the initial attack and is on at least 500m devices around the world.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















