Android phones under attack as new malware can root devices
 Devices running Android are being targeted by a new version of the Tordow malware, which was originally discovered earlier this year and attempts to obtain root privileges to perform a series of actions, such as stealing passwords.
Devices running Android are being targeted by a new version of the Tordow malware, which was originally discovered earlier this year and attempts to obtain root privileges to perform a series of actions, such as stealing passwords.
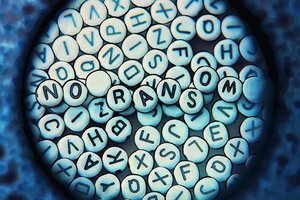
Tordow 2.0 is primarily a mobile banking Android Trojan that attempts to root the device in order to get full control and then perform a series of tasks that include the following: make phone calls, control SMS messages, steal login credentials, access contacts, encrypt files, visit webpages, manipulate banking data, remove security software, reboot a device, rename files, and act as ransomware.
Read moreIt's now commonplace for Android banking trojans to include ransomware features
 The current generation of Android banking trojans are all equipped with ransomware-like features in order to lock the user's device. Despite possessing such dangerous functions, very few Android banking trojans deploy them, focusing on their primary job of collecting login credentials for banking portals and instant messaging applications.
The current generation of Android banking trojans are all equipped with ransomware-like features in order to lock the user's device. Despite possessing such dangerous functions, very few Android banking trojans deploy them, focusing on their primary job of collecting login credentials for banking portals and instant messaging applications.
Nevertheless, when the ransomware feature is activated, the crooks behind the banking trojan do it for a very good reason. In most cases, the trojan's ransomware feature is used as a secondary monetization feature, activated on devices where the original banking trojan has failed to collect login credentials or credit card details.
Read moreMore firmware backdoor found in cheap Android phones
 Here's some bad news for Android users again. Certain low-cost Android smartphones and tablets are shipped with malicious firmware, which covertly gathers data about the infected devices, displays advertisements on top of running applications and downloads unwanted APK files on the victim's devices.
Here's some bad news for Android users again. Certain low-cost Android smartphones and tablets are shipped with malicious firmware, which covertly gathers data about the infected devices, displays advertisements on top of running applications and downloads unwanted APK files on the victim's devices.
Security researchers have discovered two types of downloader Trojans that have been incorporated in the firmware of a large number of popular Android devices operating on the MediaTek platform, which are mostly marketed in Russia. The Trojans are capable of collecting data about the infected devices, contacting their command-and-control servers.
Read moreNew trojan infects Android devices from Google AdSense
 If you don’t go to suspicious sites, malware can’t get you — right? Well, no. Even those who do not open unreliable e-mail attachments, avoid porn sites, and do not install apps from unofficial stores are not well-enough protected.
If you don’t go to suspicious sites, malware can’t get you — right? Well, no. Even those who do not open unreliable e-mail attachments, avoid porn sites, and do not install apps from unofficial stores are not well-enough protected.
New developments suggest that malware can be found even on an absolutely legitimate site, as 318,000 thousand Android users found out when their Android devices were attacked by the Svpeng.q banking Trojan from Google AdSense advertisements. Google AdSense is the biggest ad network in the world, so a lot of criminals dream about finding a way to use the network to spread their malicious programs worldwide.
Read moreAndroid banking Trojan tricks victims into submitting selfie holding their ID card
 While some payment card companies like Mastercard have switched to selfies as an alternative to passwords when verifying IDs for online payments, hackers have already started taking advantage of this new security verification methods.
While some payment card companies like Mastercard have switched to selfies as an alternative to passwords when verifying IDs for online payments, hackers have already started taking advantage of this new security verification methods.
Researchers have discovered a new Android banking Trojan that masquerades primarily as a video plugin, like Adobe Flash Player, pornographic app, or video codec, and asks victims to send a selfie holding their ID card, according to a blog post published by McAfee. The Trojan is the most recent version of Acecard that has been labeled as one of the most dangerous Android banking Trojans known today.
Read moreEmboldened by $1B Bangladesh hackers, new group targets SWIFT users
 A few months after hackers broke into Bangladesh's central bank and came close to getting away with $1 billion, researchers have uncovered evidence that a separate hacking group is targeting the same payment network.
A few months after hackers broke into Bangladesh's central bank and came close to getting away with $1 billion, researchers have uncovered evidence that a separate hacking group is targeting the same payment network.
The researchers, from security firm Symantec, said that they recently found new tools that target users of SWIFT, a payment network banks use to transfer payments that are sometimes in the range of hundreds of millions of dollars. The malicious tools monitor SWIFT messages sent to infected computers for International Bank Account Numbers or other keywords relating to specific transactions.
Read moreFastPOS malware abuses Windows Mailslots to steal POS data
 The group behind the FastPOS malware has updated their trojan with a new data exfiltration mechanism that abuses the Windows Mailslots mechanism to store data before exfiltration from infected systems.
The group behind the FastPOS malware has updated their trojan with a new data exfiltration mechanism that abuses the Windows Mailslots mechanism to store data before exfiltration from infected systems.
This new version of POS malware came to light this past summer when researchers discovered ads for it on underground carding forums. Analysis of the malware showed a new POS malware family that focused on speed and sacrificed stealth, an opposite approach to how most POS malware operate today. Trend Micro continued its analysis of this malware after the initial detection and discovered traces of FastPOS activity dating back to March 2015.
Read moreMarsJoke: the cryptor and the cure
 Every day, new versions and variations of ransomware pop up. Malware creators are still sure that ransomware is their ticket to easy street, despite the fact that law enforcement agencies are paying more and more attention to the problem.
Every day, new versions and variations of ransomware pop up. Malware creators are still sure that ransomware is their ticket to easy street, despite the fact that law enforcement agencies are paying more and more attention to the problem.
In fact, so many different versions are out there, ransomware creators have started to repeat themselves or copy the work of others. For example, the recently discovered Trojan-cryptor Polyglot, aka MarsJoke, is a knockoff of the infamous (and rather nasty) CTB-Locker ransomware. You can see traces of CTB-Locker all over Polyglot. Its interface is absurdly reminiscent of the older Trojan.
Read moreGuide for Pokémon Go Trojan catches Pokémon trainers
 Less than three months after Pokémon Go launched, criminals sneaked malware into Google Play to target Pokémon trainers. Experts discovered the Trojan several days ago and immediately reported it to Google.
Less than three months after Pokémon Go launched, criminals sneaked malware into Google Play to target Pokémon trainers. Experts discovered the Trojan several days ago and immediately reported it to Google.
Unfortunately, by that time, the malicious app called Guide for Pokémon Go had already been downloaded more than 500,000 times. In the past few months almost 6 million people gave Pokémon Go a try. It’s no wonder that the massively popular game quickly caught the attention of cybercriminals: The first malware for Pokémon Go was traced in July, soon after the launch of the game. At that time, the situation was not so dangerous.
Read moreMirai Trojan is the next big threat to IoT devices and Linux servers
 A new trojan named Mirai has surfaced, and it's targeting Linux servers and IoT devices, mainly DVRs, running Linux-based firmware, for the purpose of enslaving these systems as part of a large botnet used to launch DDoS attacks. Mirai is an evolution of an older trojan, also used for DDoS attacks.
A new trojan named Mirai has surfaced, and it's targeting Linux servers and IoT devices, mainly DVRs, running Linux-based firmware, for the purpose of enslaving these systems as part of a large botnet used to launch DDoS attacks. Mirai is an evolution of an older trojan, also used for DDoS attacks.
Mirai's mode of operation is largely the same as Gafgyt, targeting IoT devices running Busybox, a slimmed-down version of select GNU tools and libraries, usually deployed on small embedded hardware. The trojan also targets only a specific set of platforms, on which IoT devices are usually built.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















