Hackers exploit zero-day flaw in Telegram to mine cryptocurrency
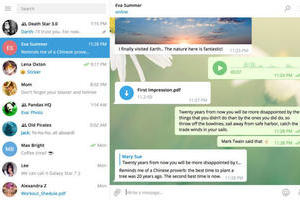 Cyber thugs have been exploiting a zero-day flaw in the Telegram Messenger desktop app in order to mine for cryptocurrencies or to install a backdoor to remotely control victims’ computers. Kaspersky Lab discovered “in the wild” attacks on Telegram Messenger’s Windows desktop client back in October 2017.
Cyber thugs have been exploiting a zero-day flaw in the Telegram Messenger desktop app in order to mine for cryptocurrencies or to install a backdoor to remotely control victims’ computers. Kaspersky Lab discovered “in the wild” attacks on Telegram Messenger’s Windows desktop client back in October 2017.
The vulnerability in the popular Telegram app had been actively exploited since March 2017 to mine a variety of cryptocurrencies, such as Monero, Zcash, Fantomcoin and others. Yet the multi-purpose malware being delivered was capable of doing more than secretly use the computing power of victims’ machines to mine cryptocurrencies.
Read moreIt's 2018 and you can still p0wn your Linux box by plugging in a USB stick
 Linux users running KDE Plasma desktop environments need to apply patches to fix a bug that can lead to malicious code execution every time a user mounts a USB thumb drive on his computer.
Linux users running KDE Plasma desktop environments need to apply patches to fix a bug that can lead to malicious code execution every time a user mounts a USB thumb drive on his computer.
The KDE Plasma team has released versions 5.8.9 and 5.12.0 to address the issue, tracked as CVE-2018-6791 and categorized as an "arbitrary command execution" vulnerability. According to a description of the bug, USB thumb drives that contain the characters `` or $() in the volume label will execute the text contained within these characters as shell commands. This means that an attacker can place malicious code in a USB thumb drive's name.
Read moreGovernment websites hit by cryptocurrency mining malware
 Thousands of websites, including those belonging to NHS services, the Student Loans Company and several English councils, have been infected by malware that forces visitors’ computers to mine cryptocurrency while using the site.
Thousands of websites, including those belonging to NHS services, the Student Loans Company and several English councils, have been infected by malware that forces visitors’ computers to mine cryptocurrency while using the site.
Late on Sunday, the website of the UK’s data protection watchdog, the Information Commissioner’s Office, was taken down to deal with the issue after it was reportedly infected by the malware. The cryptojacking script was inserted into website codes through BrowseAloud, a popular plugin that helps blind and partially-sighted people access the web. More than 5,000 websites have been flooded by the malware.
Read moreResearcher uses macOS app screenshot feature to steal passwords, tokens, keys
 Malicious app developers can secretly abuse a macOS API function to take screenshots of the user's screen and then use OCR to programmatically read the text found in the image.
Malicious app developers can secretly abuse a macOS API function to take screenshots of the user's screen and then use OCR to programmatically read the text found in the image.
The function is CGWindowListCreateImage, often utilized by Mac apps that take screenshots or live stream a user's desktop. According to Fastlane Tools founder Felix Krause, any Mac app, sandboxed or not, can access this function and secretly take screenshots of the user's screen. Krause argues that miscreants can abuse this privacy loophole and utilize CGWindowListCreateImage to take screenshots of the screen without the user's permission.
Read moreNew Monero crypto mining botnet leverages Android debugging tool
 A new botnet that distributes malware for mining Monero cryptocurrency has emerged, infecting Android devices through a port linked with a debugging tool for the OS, according to researchers at Qihoo 360 Netlab.
A new botnet that distributes malware for mining Monero cryptocurrency has emerged, infecting Android devices through a port linked with a debugging tool for the OS, according to researchers at Qihoo 360 Netlab.
Dubbed ADB.Miner by 360 Netlab, the botnet is gaining entry to Android devices–mostly smartphones and TV boxes–through port 5555, which is associated with Android Debug Bridge, a command-line tool that is used for debugging, installing apps and other purposes. ADB typically communicates with devices via USB, but it’s also possible for it to use wifi with some setup, according to Android documentation.
Read moreMixpanel analytics accidentally slurped up passwords
 The passwords of some people using sites monitored by popular analytics provider Mixpanel were mistakenly pulled into its software. Until experts’ inquiry, Mixpanel had made no public announcement about the embarrassing error beyond quietly emailing clients about the problem. Yet some need to update to a fixed Mixpanel SDK to prevent an ongoing privacy breach.
The passwords of some people using sites monitored by popular analytics provider Mixpanel were mistakenly pulled into its software. Until experts’ inquiry, Mixpanel had made no public announcement about the embarrassing error beyond quietly emailing clients about the problem. Yet some need to update to a fixed Mixpanel SDK to prevent an ongoing privacy breach.
It’s unclear which clients were impacted due to confidentiality agreements, but Mixpanel lists Samsung, BMW, Intuit, US Bank and Fitbit as some of the companies it works with. “We can tell you that less than 25 percent of our customers were impacted,” the company’s spokesperson told.
Read moreUber says hackers behind 2016 data breach were in Canada, Florida
 The two people who hacked ride-hailing firm Uber’s data in 2016 were in Canada and Florida at the time, a company security executive told a U.S. congressional committee on Tuesday.
The two people who hacked ride-hailing firm Uber’s data in 2016 were in Canada and Florida at the time, a company security executive told a U.S. congressional committee on Tuesday.
About 25 million people whose data was compromised in the breach live in the United States, Uber Technologies Inc chief information security officer John Flynn said in written testimony to a Senate Commerce Committee panel. Of those, 4.1 million were drivers, said Flynn, whose testimony described new details about the hack, the handling of which prompted newly appointed Uber Chief Executive Officer Dara Khosrowshahi to fire two top security officials.
Read moreHackers could seize control of your fridge and force it to mine Bitcoin
 Hackers could seize control of home appliances fitted with new smart technology and force them to mine Bitcoin without the owner's knowledge, security experts have warned.
Hackers could seize control of home appliances fitted with new smart technology and force them to mine Bitcoin without the owner's knowledge, security experts have warned.
High-tech fridges, ovens and washing machines powered by computer processors and linked to home assistant devices and smart phones are all vulnerable to attack from cyber criminals, specialists from geopolitics consultancy Stratfor said. And, if hackers manage to hijack the software controlling them, they could use the appliance’s computing power to mine cryptocurrency such as Bitcoin, then funnel off the proceeds into their own digital wallets.
Read moreCryptocurrency mining malware that uses an NSA exploit is on the rise
 A computer security exploit developed by the US National Security Agency and leaked by hackers last year is now being used to mine cryptocurrency, and according to cybersecurity experts the number of infections is rising.
A computer security exploit developed by the US National Security Agency and leaked by hackers last year is now being used to mine cryptocurrency, and according to cybersecurity experts the number of infections is rising.
Last April, a hacking group called the Shadow Brokers leaked EternalBlue, a Windows exploit that was developed by the NSA. Less than a month later, EternalBlue was used to unleash a devastating global ransomware attack called WannaCry that infected more than 230,000 computers in 150 countries. A month later, in June, the EternalBlue exploit was again used to cripple networks across the world in an even more sophisticated attack.
Read moreHackers stole $400 million from cryptocurrency exchange Coincheck
 Hackers have stolen roughly $532.6 million from Tokyo-based cryptocurrency exchange Coincheck, raising questions about security and regulatory protection in the emerging market of digital assets.
Hackers have stolen roughly $532.6 million from Tokyo-based cryptocurrency exchange Coincheck, raising questions about security and regulatory protection in the emerging market of digital assets.
The following are some questions and answers about one of the largest heists of cryptocurrencies in the history: NEM is a cryptocurrency launched in March 2015 by a team of five developers identifying themselves as Pat, Makoto, Gimre, BloodyRookie and Jaguar. Its acronym stands for New Economy Movement and, like other cryptocurrencies, markets itself as a digital coin outside the control of governments and central banks, which can be used for fast, global transactions.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















