Wikileaks reveals CIA malware that hacks & spy on Linux computers
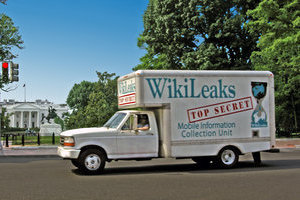
 WikiLeaks has just published a new batch of the ongoing Vault 7 leak, this time detailing an alleged CIA project that allowed the agency to hack and remotely spy on computers running the Linux operating systems.
WikiLeaks has just published a new batch of the ongoing Vault 7 leak, this time detailing an alleged CIA project that allowed the agency to hack and remotely spy on computers running the Linux operating systems.
Dubbed OutlawCountry, the project allows the CIA hackers to redirect all outbound network traffic on the targeted computer to CIA controlled computer systems for exfiltrate and infiltrate data. The OutlawCountry Linux hacking tool consists of a kernel module, which the CIA hackers load via shell access to the targeted system and create a hidden Netfilter table with an obscure name on a target Linux user.
Read moreMicrosoft's next big Windows update will use AI to fight malware
 Windows Fall Creators Update will come with a hefty serving of security upgrades, made timely by the increasingly rampant cyberattacks targeting the platform these days.
Windows Fall Creators Update will come with a hefty serving of security upgrades, made timely by the increasingly rampant cyberattacks targeting the platform these days.
Microsoft has revealed how the upcoming major update will level up Windows Defender Advanced Threat Protection, a Win 10 enterprise service that flags early signs of infection. Windows enterprise director Rob Lefferts said the upgrade will use data from Redmond's cloud-based services to create an AI anti-virus that will make ATP much better at preventing cyberattacks.
Read moreWikileaks dump reveals a creepy CIA location-tracking trick
![]() How many people specifically know where you are right now? Friends and family? Your coworkers? If you're using a Windows laptop or PC you could add another group to the list: the CIA.
How many people specifically know where you are right now? Friends and family? Your coworkers? If you're using a Windows laptop or PC you could add another group to the list: the CIA.
New documents released as part of WikiLeaks' series of CIA hacking revelations detail a method the agency uses to geolocate computers. The agency infects target devices with malware that can then check which public Wi-Fi networks a given computer can connect to at a given moment, as well as the signal strengths of those networks. From there, the malware compares the list of available Wi-Fi options to databases of public Wi-Fi networks to figure out where the device is.
Read moreWikileaks docs show how the CIA allegedly infected offline computers
 Hacking air-gapped machines — computers that are not connected to the internet, so theoretically less vulnerable — is always pretty interesting.
Hacking air-gapped machines — computers that are not connected to the internet, so theoretically less vulnerable — is always pretty interesting.
On Wednesday, Wikileaks published a series of alleged CIA documents that supposedly show how the intelligence agency's malware was designed to infect these sort of targets. Naturally, the documents indicate how the CIA has continued to develop its own hacking tools, allegedly targeting devices from smart TVs to internet routers. According to one of the documents, "Brutal Kangaroo is a tool suite for targeting closed networks by air gap jumping using thumbdrives."
Read moreWikiLeaks 'Cherry Blossom' documents reveal CIA hacks Wi-Fi routers
 Purported CIA documents published by WikiLeaks reveal the US Central Intelligence Agency has been hacking wireless routers for years as part of its surveillance efforts.
Purported CIA documents published by WikiLeaks reveal the US Central Intelligence Agency has been hacking wireless routers for years as part of its surveillance efforts.
The trove of documents released by the anti-privacy publication on Thursday details the CIA’s CherryBlossom project, in which the intelligence agency has compromised Wi-Fi routers in private homes, public spaces, businesses and enterprise environments in order to gather information about specific targets. The project comes from the CIA's elite hacking unit, the Engineering Development Group. The leaked files include installation guides, manuals and other documents.
Read moreTim Cook says Apple focused on autonomous systems in cars push
 After years toiling away in secret on a car project, Tim Cook has for the first time elaborated on the company’s plans in the automotive market. “We’re focusing on autonomous systems,” Cook said in a June 5 interview.
After years toiling away in secret on a car project, Tim Cook has for the first time elaborated on the company’s plans in the automotive market. “We’re focusing on autonomous systems,” Cook said in a June 5 interview.
“It’s a core technology that we view as very important.” He likened the effort to “the mother of all AI projects,” saying it’s “probably one of the most difficult AI projects to work on.” The prospect of self-driving cars has seen a slew of technology companies push into the auto industry, according to McKinsey & Co. Alphabet’s Waymo unit has signed partnerships with Fiat Chrysler Automobiles NV and Lyft to develop the technology.
Read moreWikiLeaks says CIA’s “Pandemic” turns servers into infectious Patient Zero
 WikiLeaks just published details of a purported CIA operation that turns Windows file servers into covert attack machines that surreptitiously infect computers of interest inside a targeted network.
WikiLeaks just published details of a purported CIA operation that turns Windows file servers into covert attack machines that surreptitiously infect computers of interest inside a targeted network.
"Pandemic," as the implant is codenamed, turns file servers into a secret carrier of whatever malware CIA operatives want to install, according to documents published Thursday by WikiLeaks. When targeted computers attempt to access a file on the compromised server, Pandemic uses a clever bait-and-switch tactic to surreptitiously deliver malicious version of the requested file. The Trojan is then executed by the targeted computers.
Read moreThis French school is using facial recognition to find out when students aren’t paying attention
 A business school in Paris will soon begin using artificial intelligence and facial analysis to determine whether students are paying attention in class. The software, called Nestor, will be used two online classes at the ESG business school beginning in September.
A business school in Paris will soon begin using artificial intelligence and facial analysis to determine whether students are paying attention in class. The software, called Nestor, will be used two online classes at the ESG business school beginning in September.
LCA Learning, the company that created Nestor, presented the technology at an event at the United Nations in New York last week. The idea is to use the data that Nestor collects to improve the performance of both students and professors. The software uses students’ webcams to analyze eye movements and facial expressions and determine whether students are paying attention to a video lecture.
Read moreWikiLeaks reveals Athena CIA spying program targeting all versions of Windows
 WikiLeaks has released the user guide, demo and more of a new spy malware strain allegedly created and used by the CIA. The spyware targets all Windows versions and allows attackers to completely hijack computers, steal data and send it to CIA severs, delete data and upload malicious software.
WikiLeaks has released the user guide, demo and more of a new spy malware strain allegedly created and used by the CIA. The spyware targets all Windows versions and allows attackers to completely hijack computers, steal data and send it to CIA severs, delete data and upload malicious software.
According to WikiLeaks' documents, the spyware was created by the CIA, with help from a private New Hampshire-based cybersecurity firm called Siege Technologies. The spyware has two modules. While Athena, the primary module, targets Windows XP to 10, the secondary module dubbed Hera targets Windows 8 through Windows 10.
Read moreCIA files released by WikiLeaks spur multi-agency manhunt
 Federal investigators suspect a vetted member of the U.S. intelligence community supplied WikiLeaks with the trove of previously unpublished CIA documents released by the anti-secrecy group last month.
Federal investigators suspect a vetted member of the U.S. intelligence community supplied WikiLeaks with the trove of previously unpublished CIA documents released by the anti-secrecy group last month.
A joint investigation launched by the CIA and FBI in the wake of last month’s WikiLeaks publication has given way to a manhunt within the federal government, sources familiar with the probe told this week. The material released by WikiLeaks was “classified and stored in a highly secure section of the intelligence agency,” and had likely been compromised by an individual with physical access to the documents, such as a CIA employee or contractor.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















