Hackers say they’re revealing more from trove of NSA data
 A group calling itself “Shadow Brokers” says it has released another gem from its trove of high-level hacking tools stolen from the U.S.’s National Security Agency, potentially offering added insight into how America’s spies operate online.
A group calling itself “Shadow Brokers” says it has released another gem from its trove of high-level hacking tools stolen from the U.S.’s National Security Agency, potentially offering added insight into how America’s spies operate online.
The leak discloses NSA-style codenames and carries internet protocol information about scores of organizations, many based in Japan, China and South Korea. Matthew Hickey, co-founder of UK-based cybersecurity consultancy Hacker House, said it was plausible that the servers would have seen use as staging posts to help obfuscate the origin of electronic eavesdropping operations.
Read moreProbe of leaked US NSA hacking tools examines operative's mistake
 A US investigation into a leak of hacking tools used by the National Security Agency is focusing on a theory that one of its operatives carelessly left them available on a remote computer and Russian hackers found them, four people with direct knowledge of the probe told.
A US investigation into a leak of hacking tools used by the National Security Agency is focusing on a theory that one of its operatives carelessly left them available on a remote computer and Russian hackers found them, four people with direct knowledge of the probe told.
The tools, which enable hackers to exploit software flaws in computer and communications systems from vendors such as Cisco Systems and Fortinet Inc, were dumped onto public websites last month by a group calling itself Shadow Brokers. One reason for suspecting government instead of criminal involvement, officials said, is that the hackers revealed the NSA tools rather than immediately selling them.
Read moreCisco finds new zero-day exploit linked to NSA hackers
 Network equipment vendor Cisco is finally warning its customers of another zero-day vulnerability the company discovered in the trove of NSA's hacking exploits and implants leaked by the group calling itself "The Shadow Brokers."
Network equipment vendor Cisco is finally warning its customers of another zero-day vulnerability the company discovered in the trove of NSA's hacking exploits and implants leaked by the group calling itself "The Shadow Brokers."
Last month, the Shadow Brokers published firewall exploits, implants, and hacking tools allegedly stolen from the NSA's Equation Group, which was designed to target major vendors including, Cisco, Juniper, and Fortinet. Cisco analyzed the exploit and noted that it had not identified any new flaws related to this exploit in its current products.
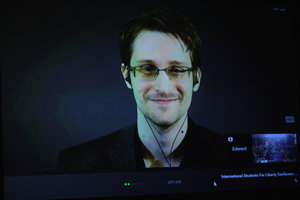
Read moreCongressional report slams NSA leaker Edward Snowden
 A House intelligence committee report condemned Edward Snowden, saying the National Security Agency leaker is not a whistleblower and that the vast majority of the documents he stole were defense secrets that had nothing to do with privacy.
A House intelligence committee report condemned Edward Snowden, saying the National Security Agency leaker is not a whistleblower and that the vast majority of the documents he stole were defense secrets that had nothing to do with privacy.
The Republican-led committee released a three-page unclassified summary of its two-year bipartisan examination of how Snowden was able to remove more than 1.5 million classified documents from secure NSA networks, what the documents contained and the damage their removal caused to US national security. Snowden was an NSA contract employee when he leaked the documents to journalists.
Read moreNew leaked files reveal more about NSA satellite eavesdropping
 Leaks by NSA whistleblower Edward Snowden have revealed how his former employer used the US spy base at Menwith Hill in Yorkshire to conduct ‘kill or capture’ missions in its global shadow war.
Leaks by NSA whistleblower Edward Snowden have revealed how his former employer used the US spy base at Menwith Hill in Yorkshire to conduct ‘kill or capture’ missions in its global shadow war.
The new files published by the Intercept partly lay to rest speculation by journalists and campaigners over what really goes on at the US base. They show that secretive NSA kill-capture operations in the Middle East have been developed and initiated from inside the base’s heavily guarded perimeter wire. The programs, which carry names like GHOSTWOLF and GHOSTHUNTER, have been used to support conventional operations in war zones.
Read moreThe NSA leak is real, Snowden documents confirm
 A hacking group calling itself the “ShadowBrokers” announced an auction for what it claimed were “cyber weapons” made by the NSA.
A hacking group calling itself the “ShadowBrokers” announced an auction for what it claimed were “cyber weapons” made by the NSA.
Based on documents provided by Edward Snowden, The Intercept can confirm that the arsenal contains authentic NSA software, part of a powerful constellation of tools used to covertly infect computers worldwide. The provenance of the code has been a matter of heated debate this week among cybersecurity experts, and while it remains unclear how the software leaked, one thing is now beyond speculation: The malware is covered with the NSA’s virtual fingerprints and clearly originates from the agency.
Read moreNSA's hacking group hacked! Bunch of private hacking tools leaked online
 A mysterious hacker or hackers going by the name “The Shadow Brokers” claims to have hacked a group linked to the NSA and dumped a bunch of its hacking tools. In a bizarre twist, the hackers are also asking for 1 million bitcoin in an auction to release more files.
A mysterious hacker or hackers going by the name “The Shadow Brokers” claims to have hacked a group linked to the NSA and dumped a bunch of its hacking tools. In a bizarre twist, the hackers are also asking for 1 million bitcoin in an auction to release more files.
The hackers referred to their victims as the Equation Group, a codename for a government hacking group widely believed to be the NSA. The security firm Kaspersky Lab unmasked Equation Group in 2015, billing it as the most advanced hacking group Kaspersky researchers had ever seen. The Shadow Brokers claimed to have hacked the Equation Group and stolen some of its hacking tools.
Read moreThis is what the world's spies used instead of MSN messenger
 What do spies use to chat online? A terribly ugly Windows programme. At least, that's what the Five Eyes intelligence alliance was using back in 2003, according to a newly released Snowden document.
What do spies use to chat online? A terribly ugly Windows programme. At least, that's what the Five Eyes intelligence alliance was using back in 2003, according to a newly released Snowden document.
“The Five-Eyes SIGINT [signals intelligence] Directors will soon be using a new tool to enhance their collaboration on subjects ranging from current intelligence objectives to future collection planning,” reads an issue of SID Today, the NSA's internal newsletter, dating from September 2003. InfoWorkSpace, as the tool is called, allowed text chat, audio conferencing, shared screen views, and virtual whiteboards, the newsletter explains.
Read moreNSA looking to exploit Internet of Things, including biomedical devices
 The national security agency is researching opportunities to collect foreign intelligence — including the possibility of exploiting internet-connected biomedical devices like pacemakers, according to a senior official.
The national security agency is researching opportunities to collect foreign intelligence — including the possibility of exploiting internet-connected biomedical devices like pacemakers, according to a senior official.
“We’re looking at it sort of theoretically from a research point of view right now,” Richard Ledgett, the NSA’s deputy director, said at a conference on military technology at Washington’s Newseum. Biomedical devices could be a new source of information for the NSA’s data hoards — “maybe a niche kind of thing … a tool in the toolbox,” he said, though he added that there are easier ways to keep track of overseas terrorists and foreign intelligence agents.
Read moreThe Intercept is broadening access to the Snowden archive
 From the time we began reporting on the archive provided to us in Hong Kong by NSA whistleblower Edward Snowden, we sought to fulfil his two principal requests for how the materials should be handled.
From the time we began reporting on the archive provided to us in Hong Kong by NSA whistleblower Edward Snowden, we sought to fulfil his two principal requests for how the materials should be handled.
They should be released in conjunction with careful reporting that puts the documents in context and makes them digestible to the public, and that the welfare and reputations of innocent people should be safeguarded. As time has gone on, The Intercept has sought out new ways to get documents from the archive into the hands of the public, consistent with the public interest as originally conceived.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















