New Android Trojan spies on users
 AVG researchers have discovered a new Android Trojan that tricks users into believing they have shut their device down while it continues working, and is able to silently make calls, send messages, take photos and perform many other tasks.
AVG researchers have discovered a new Android Trojan that tricks users into believing they have shut their device down while it continues working, and is able to silently make calls, send messages, take photos and perform many other tasks.
They dubbed it, and AVG's security solutions detect it as PowerOffHijack. PowerOffHijack has been discovered in China, where it has already infected over 10,000 devices. It is apparently being propagated via third-party online app stores, but the researchers haven't mentioned what apps it masquerades as. The Trojan is capable of infecting Android versions below v5.0 (Lollipop). How does it work?
Read moreStay away from Google Play at least now
 A couple of related vulnerabilities on the Google Play Store have left Android users vulnerable to malware-slingers. Security watchers warn that a flaw – when combined with a recent Android WebView bug – creates a means for hackers to silently install apps from the Google Play store.
A couple of related vulnerabilities on the Google Play Store have left Android users vulnerable to malware-slingers. Security watchers warn that a flaw – when combined with a recent Android WebView bug – creates a means for hackers to silently install apps from the Google Play store.
A lot of devices running installations of Android 4.3 and earlier ship with browsers with Universal Cross-site Scripting exposures. Using a browser not susceptible to widely known UXSS vulnerabilities can help mitigate the lack of universal X-Frame-Options for the play.google.com domain.
Read moreMost Android dating apps have security flaws
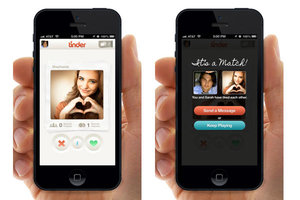 Using a dating app on your work's dime could end up putting your company's data at risk, new research has found. A study warned that a lot of the most popular dating mobile apps on the Android mobile platform have flaws that could put users at risk from data theft and cyber attacks.
Using a dating app on your work's dime could end up putting your company's data at risk, new research has found. A study warned that a lot of the most popular dating mobile apps on the Android mobile platform have flaws that could put users at risk from data theft and cyber attacks.
Making matters worse, half of all the companies examined in the study have at least one employee using dating apps – effectively punching a gaping hole in a company's security fence. The problem lies with the apps, but also highlights issues with Android. These Android apps often ask for access to an Android device's data.
Read moreA new banking trojan targets Android users
 A new Android Trojan that specializes in stealing banking information by intercepting SMS messages has been making the rounds. Trojan appears to be targeting Chinese Android users as many types of malware that came before it, at least for the moment.
A new Android Trojan that specializes in stealing banking information by intercepting SMS messages has been making the rounds. Trojan appears to be targeting Chinese Android users as many types of malware that came before it, at least for the moment.
The Trojan’s forte is sniffing out message having to do with banking and emailing those captured SMS messages to itself. In both cases the Trojan sends the information to a hardcoded Chinese email service and a hardcoded Chinese phone number. The Trojan’s SMS communication works both ways, because it can receive commands from the command and control server via SMS.
Read moreAndroid Wi-Fi Direct vulnerability details disclosed
 Google and Core Security are at odds over the severity of a vulnerability affecting a number of Android mobile devices, details of which were released by the security vendor today.
Google and Core Security are at odds over the severity of a vulnerability affecting a number of Android mobile devices, details of which were released by the security vendor today.
The issue was reported to the Android security team and in subsequent communication between the two parties, the severity of the vulnerability was debated, culminating with Core’s disclosure. Google three times acknowledged Core’s report and request for a timeline on a patch, and each time Google said it did not have one. The flaw is a remotely exploitable denial-of-service vulnerability in Wi-Fi-Direct, a standard that allows wireless devices to connect directly.
Read moreBanking customers are plagued with dangerous mobile apps
 The move towards mobile banking and mobile financial services has created many benefits for both financial institutions and their customers.
The move towards mobile banking and mobile financial services has created many benefits for both financial institutions and their customers.
However, in an attempt to better illustrate the risks in this area, RiskIQ has released data on the number of suspicious mobile apps being downloaded by Android users looking for banking and finance-related services. Branded malicious mobile apps come in the form of compromised versions of official mobile apps or mobile apps wrapped in branding. They imitate functionality consistent with a given brand and have been pre-installed with malware or data-stealing permissions.
Read moreFree "TOP Security!" app is available on Google Play
 TOP Security! is a new application of the Iceland company Safeum Communications ehf. It is up-to-date news in the field of information security. Install the app and be aware of the latest events.
TOP Security! is a new application of the Iceland company Safeum Communications ehf. It is up-to-date news in the field of information security. Install the app and be aware of the latest events.
Personal data protection has been one of the trending topics for the past few years. However, all people perceive it differently: someone thinks of governmental control, others do not want to become the victims of online frauds. But judging from your feedback, it’s clear that IT security is a topic of interest for too many people. We are sure – everyone should pay attention to protection of confidential information and personal security.
Read moreFree TOP Security! app is on Google Play
 TOP Security! is a new application of the Iceland company Safeum Communications ehf. It is up-to-date news in the field of information security. Install the app and be aware of the latest events.
TOP Security! is a new application of the Iceland company Safeum Communications ehf. It is up-to-date news in the field of information security. Install the app and be aware of the latest events.
Personal data protection has been one of the trending topics for the past few years. However, all people perceive it differently: someone thinks of governmental control, others do not want to become the victims of online frauds. But judging from your feedback, it’s clear that IT security is a topic of interest for too many people. We are sure – everyone should pay attention to protection of confidential information and personal security.
Read moreChina buys Trojans to spy on smartphones
 The police department of the Chinese city of Wenzhou in southeast China has spent thousands of dollars on a software that installs Trojan horse viruses into mobile phones, allowing police officers to spy on other people's activities on their phones.
The police department of the Chinese city of Wenzhou in southeast China has spent thousands of dollars on a software that installs Trojan horse viruses into mobile phones, allowing police officers to spy on other people's activities on their phones.
Investigative reporter first made the report when he posted on his Sina Weibo page a screenshot of a list of devices that were purchased by the Wenzhou police force and posted on the website of the Wenzhou Economic Technology Department Zone in Zheijiang province. The list includes a lot of Trojan horse viruses for mobile phones and a device that injects the virus into illegally unlocked iOS and Android phones.
Read moreBlackBerry is working with Boeing on a self-destructing phone
 BlackBerry Ltd is working with Boeing Co on Boeing's high-security Android-based smartphone, the Canadian mobile technology company's chief executive said. The Boeing Black phone being developed by the Chicago-based aerospace and defense contractor, which is best known for jetliners and fighter planes, can self-destruct if it is tampered with.
BlackBerry Ltd is working with Boeing Co on Boeing's high-security Android-based smartphone, the Canadian mobile technology company's chief executive said. The Boeing Black phone being developed by the Chicago-based aerospace and defense contractor, which is best known for jetliners and fighter planes, can self-destruct if it is tampered with.
The Boeing Black device encrypts calls and is aimed at government agencies and others that need to keep communications and data secure. The Boeing phone uses dual SIM cards to enable it to access multiple cell networks and can be configured to connect with biometric sensors and satellites.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















