Become a SafeUM tester and get free PREMIUM subscription for a year
 Be among the first users of SafeUM! Participate in testing of the innovative secure messenger and become a part of developers professional team.
Be among the first users of SafeUM! Participate in testing of the innovative secure messenger and become a part of developers professional team.
Make sure you share your comments and reviews in the social networks, using hashtag #SafeUM, as the most active participants will get PREMIUM subscription for a year! We are looking forward to your suggestions, comments and reviews about SafeUM. Become a tester here
Read moreFacebook's iOS app now uses the device's microphone to listen to
![]() Facebok has recently launched a new feature that tries to identify television or music content while using the device's microphone to listen to the environment when posting a status update.
Facebok has recently launched a new feature that tries to identify television or music content while using the device's microphone to listen to the environment when posting a status update.
To utilize this option, the user has to click the “mood” icon when starting to create a status update and the app will start listening to identify a song, a movie or a TV show. It is possible to turn off the feature by tapping the microphone icon at the top right of the screen. Facebook assures that none of the sound data is saved and the user is given the choice whether to add it to the post or not, but adding will only be possible if the program identifies the content.
Read moreRussian hackers have learnt to extort money for locked iPhone

The exact number of hacked phones is unknown. The representatives of Apple declined to comment.
The attackers use the fact that in the new version of iOS 7 has become possible to block stolen smartphone that cannot be removed with help of a reset or flashing devices. If you want to use this feature, you must know the user‘s name (Apple ID, also known as e-mail address) and password.
Hackers hacked iOS 7 Activation Lock with iCloud breach
 Dutch group of hackers named doulCi can activate blocked by means of Activation Lock function iPhones, using false iCloud servers.
Dutch group of hackers named doulCi can activate blocked by means of Activation Lock function iPhones, using false iCloud servers.
Team DoulCi published a workaround that requires users to plug a bricked device into their computer and alter the "hosts" file inside. The iPhone or iPad is then tricked into connecting to the hacked server, which unlocks the gadget. Then the device is enough to be connected to iTunes and to dump Activation Lock regularly. DoulCi system works only partially: in attempt to unblock iPhone by their method, GSM module remains disconnected because hackers have no corresponding activation keys, however they promise to correct a problem shortly. The user gets access only to device operating system and Wi-Fi.
Read moreFacebook app knows what you’re hearing, watching
 Facebook’s mobile app just grew a keen sense of hearing. Starting Wednesday, the app has the ability to recognize music and television shows playing in the vicinity of users.
Facebook’s mobile app just grew a keen sense of hearing. Starting Wednesday, the app has the ability to recognize music and television shows playing in the vicinity of users.
The feature is designed to make it easier for users to share. When users begin to write a post, the Facebook app will offer to include information about music or shows playing in the background. “We want to help people tell better stories,” said Aryeh Selekman, the product manager who led the development of the feature. “I hope there are people who love the feature and post more.” If Facebook users share more about themselves, that can boost the value of ads targeted at some of its 1.28 billion users.
Read moreApple has disclosed the scale of the cooperation with the U.S. authorities
 Apple has the technical ability to disclose a wide range of information about a user upon the request of the authorities – from the person’s name and contact information to their photos and e-mail content.
Apple has the technical ability to disclose a wide range of information about a user upon the request of the authorities – from the person’s name and contact information to their photos and e-mail content.
This refers to the new company policy of cooperation with the law enforcement agencies. If there is a valid search warrant and the serial number of the iPhone, iPod touch or iPad the Cupertino-based company may extract some types of data, even if the device has a password.
In particular, this refers to the user files created with proprietary applications. These include SMS-messages, photos, videos, contacts, and call history records. In case if the iOS-device is password-protected, the Apple cannot disclose the contents of the e-mail, calendar plans or the data of the third party applications.
Read moreApple does not encrypt email attachments in iOS 7
 Apple's Mail app in iOS 7 is failing to encrypt email attachments, leaving user data vulnerable to hackers, a security researcher claims. Andreas Kurtz posted his findings online, saying Apple's email app in the latest version of its iPhone and iPad software is not securing files that are attached to emails.
Apple's Mail app in iOS 7 is failing to encrypt email attachments, leaving user data vulnerable to hackers, a security researcher claims. Andreas Kurtz posted his findings online, saying Apple's email app in the latest version of its iPhone and iPad software is not securing files that are attached to emails.
This makes the files readily available to anyone with the proper software. The researcher said he confirmed this by trying out a method on email stored in an iPhone 4 running the latest version of iOS 7. He said he was able to find the device's email attachments unprotected, and he said he later confirmed the process on an iPhone 5s and an iPad 2. Advertisement "I found all attachments accessible without any encryption/restriction," Kurtz wrote.
Read moreViber mobile messenger app leaves user data unencrypted
 Viber, a mobile messenger app that allows users to make phone calls and send text messages and images for free, also gives up plenty of free user data to anyone who wants to listen.
Viber, a mobile messenger app that allows users to make phone calls and send text messages and images for free, also gives up plenty of free user data to anyone who wants to listen.
According to researchers from the University of New Haven (UNH) in Connecticut, US, Viber's app sends user messages in unencrypted form - including photos, videos, doodles, and location images.
All of that rich data from users is also stored unencrypted on Viber's servers, rather than being deleted immediately, and is accessible without credentials, just a link, the UNH researchers said.
Read moreFacebook Launches Friend-Spying Feature ‘Nearby Friends’
 A new feature introduced by Facebook to allow meeting the Facebook friends in real time when they are actually close by has had mixed reactions from its users. Nearby Friends, an optional mobile application, taps steady stream of location information and makes it possible for friends to track each other in real time and meet up in real life.
A new feature introduced by Facebook to allow meeting the Facebook friends in real time when they are actually close by has had mixed reactions from its users. Nearby Friends, an optional mobile application, taps steady stream of location information and makes it possible for friends to track each other in real time and meet up in real life.
For example, when you’re headed to the movies, ”Nearby Friends” will let you know if friends are nearby so you can see the movie together or meet up afterward,” says the Facebook newsroom. When selected, it means one can have information about:
Read moreSteve Jobs planned 'Holy War' with Google
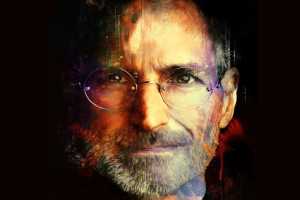 Apple founder Steve Jobs was planning to wage a "Holy War" against Google a year before he died, a higly confidential email has revealed.
Apple founder Steve Jobs was planning to wage a "Holy War" against Google a year before he died, a higly confidential email has revealed.
Jobs sent the email in 2010 to his top 100 most senior executives, in which he outlined the company's strategy for the following year.
In it, he announced that 2011 would see a 'Holy War' between Apple and Google, and outlined all the ways in which the two companies would compete – from cloud services to mobile operating systems.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















