Can your iPhone be hacked? Cellebrite says it can crack iPhone 6, 6 Plus devices
 Cellebrite, an Israel-based cybersecurity firm, announced on Thursday it has added the capability to crack a number of locked Apple devices running iOS, including the iPhone 6 and iPhone 6 Plus.
Cellebrite, an Israel-based cybersecurity firm, announced on Thursday it has added the capability to crack a number of locked Apple devices running iOS, including the iPhone 6 and iPhone 6 Plus.
Word of the new ability came from Shahar Tal, the director of forensics research for Cellebrite, who announced the breakthrough on Twitter. “Proud of the team's continuous research achievements almost as much as I'm proud of the true justice we help serve around the world,” he wrote. “Seeing murder cases solved and child molesters jailed drives us and fills our day-to-day with immense cause. I'm thankful.”
Read moreiPhone message prank crashes phones with a single text
 A three character-long text message can temporarily disable iPhones, a hacker has shown. On receiving the message, iPhones instantly freeze for around a minute, and sometimes users are forced to restart.
A three character-long text message can temporarily disable iPhones, a hacker has shown. On receiving the message, iPhones instantly freeze for around a minute, and sometimes users are forced to restart.
Besides blocking the number that the malicious messages come from the victim has no way of preventing the attack, although its effects are temporary and do not work on the most recent version of iOS. The bug is the latest in a series of strange text-message vulnerabilities that have affected iPhones in recent years. The offending message appears to contain just three characters - a white flag emoji, a “0” and a rainbow emoji.
Read moreResearchers break Apple's iPhone and iPad activation lock
 A lock is only good at protecting things if it actually stays locked. The activation lock in iOS, for example, makes it very hard for someone other than the owner to wipe an iPhone or iPad and set it up as a new device. Very hard, but not impossible.
A lock is only good at protecting things if it actually stays locked. The activation lock in iOS, for example, makes it very hard for someone other than the owner to wipe an iPhone or iPad and set it up as a new device. Very hard, but not impossible.
Two different bugs have recently been discovered that could allow someone to bypass Apple’s activation lock. One impacts devices running iOS 10.1 and another on the most current version of the software, iOS 10.1.1. Expert workaround exploited a weakness in the iOS device setup process, and he tested it on a locked iPad he purchased from eBay.
Read moreThis three-second video can crash almost every iPhone ever made
 A corrupted video being shared online will crash any iPhone or iPad it is played on, and in some cases causes the device to switch off and become unresponsive. The video is a file which can be played in the iOS Safari web browser, but quickly slows the device to a crawl, before causing it to lock up and freeze.
A corrupted video being shared online will crash any iPhone or iPad it is played on, and in some cases causes the device to switch off and become unresponsive. The video is a file which can be played in the iOS Safari web browser, but quickly slows the device to a crawl, before causing it to lock up and freeze.
The flaw is being described as "completely crazy" and will crash any iOS device. It comes a year after a certain text message was discovered to crash and reboot iPhones whenever it was received. But where the text bug caused the iPhone to reboot, the newly discovered video file crashes the phone to such an extent that only a hard reset will bring the phone back to life.
Read moreApple keeps constant log of iPhone calls in iCloud, warns cop contractor
 Apple has a hidden feature for you in its iPhones: call logs going back as far as four months are stored in near real-time in the iCloud. That’s the warning today from a Russian provider of iPhone hacking tools, Elcomsoft, which claimed the feature was automatic and there was no way to turn it off bar shutting down iCloud Drive altogether.
Apple has a hidden feature for you in its iPhones: call logs going back as far as four months are stored in near real-time in the iCloud. That’s the warning today from a Russian provider of iPhone hacking tools, Elcomsoft, which claimed the feature was automatic and there was no way to turn it off bar shutting down iCloud Drive altogether.
Whilst it was well-known that iCloud backups would store call logs, contacts and plenty of other valuable data, users should be concerned to learn that their communications records are consistently being sent to Apple servers without explicit permission, said Elcomsoft CEO Vladimir Katalov.
Read moreNew Hack: How to bypass iPhone passcode to access photos and messages
 Setting a passcode on your iPhone is the first line of defense to help prevent other people from accessing your personal details. However, it's pretty much easy for anyone with access to your iPhone to bypass the passcode protection and access your personal photos and messages.
Setting a passcode on your iPhone is the first line of defense to help prevent other people from accessing your personal details. However, it's pretty much easy for anyone with access to your iPhone to bypass the passcode protection and access your personal photos and messages.
A new critical security flaw discovered in iOS 8 and newer, including 10.2 beta 3, allows anyone to bypass iPhone's passcode and gain access to personal information using the benevolent nature of Apple's personal assistant Siri. The security glitch has been discovered by EverythingApplePro and iDeviceHelps and now that they have gone public with a video.
Read moreiPhone passcode bypassed with NAND mirroring attack
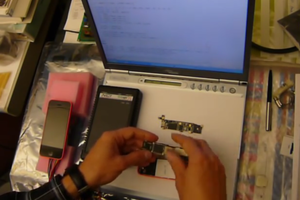 Passcodes on iPhones can be hacked using store-bought electronic components worth less than $100, according to one Cambridge computer scientist. Sergei Skorobogatov has demonstrated that NAND mirroring — the technique dismissed by James Comey, the director of the FBI, as unworkable—is actually a viable means of bypassing passcode entry limits on an Apple iPhone 5C.
Passcodes on iPhones can be hacked using store-bought electronic components worth less than $100, according to one Cambridge computer scientist. Sergei Skorobogatov has demonstrated that NAND mirroring — the technique dismissed by James Comey, the director of the FBI, as unworkable—is actually a viable means of bypassing passcode entry limits on an Apple iPhone 5C.
What's more, the technique, which involves soldering off the phone's flash memory chip, can be used on any model of iPhone up to the iPhone 6 Plus, which use the same type of LGA60 NAND chip. Later models, however, will require "more sophisticated equipment and FPGA test boards."
Read moreSnowden designs device to warn when an iPhone is tracking users
 Mobile devices have without a doubt brought convenience to the masses, but that benefit comes at a high price for journalists, activists, and human rights workers who work in war-torn regions or other high-risk environments.
Mobile devices have without a doubt brought convenience to the masses, but that benefit comes at a high price for journalists, activists, and human rights workers who work in war-torn regions or other high-risk environments.
Now, NSA whistleblower Edward Snowden has designed an iPhone accessory that could one day be used to prevent the devices from leaking their whereabouts. Working with renowned hardware hacker Andrew “Bunnie” Huang, Snowden has devised the design for what the team is calling the "Introspection Engine." For now, it's aimed only at iPhone 6 models, but eventually the pair hopes to create specifications for a large line of devices.
Read moreYour iPhone can be hacked remotely with just a message
 Do you own an iPhone? Mac? Or any Apple device? Just one specially crafted message can expose your personal information, including your authentication credentials stored in your device's memory, to a hacker.
Do you own an iPhone? Mac? Or any Apple device? Just one specially crafted message can expose your personal information, including your authentication credentials stored in your device's memory, to a hacker.
The vulnerability is quite similar to the Stagefright vulnerabilities, discovered a year ago in Android, that allowed hackers to silently spy on almost a Billion phones with just one specially-crafted text message. Cisco Talos senior researcher Tyler Bohan, who discovered this critical Stagefright-type bug in iOS, described the flaw as "an extremely critical bug, comparable to the Android Stagefright as far as exposure goes."
Read moreDangers for iPhone users: vulnerabilities in the iPhone
 Apple iPhone users are notorious for their slight indulgence towards those who prefer alternative platforms. Android is constantly under attack by malware and Trojans, they say, while iOS is immune to threats. Is it really that secure as Apple fans see it?
Apple iPhone users are notorious for their slight indulgence towards those who prefer alternative platforms. Android is constantly under attack by malware and Trojans, they say, while iOS is immune to threats. Is it really that secure as Apple fans see it?
The answer is: no, it isn’t. In this article we will discuss several types of attacks which are as bad for the iPhones as they are for other devices. Phishing attacks target ‘what’s between a chair and a keyboard,’ meaning the users themselves. Phishers typically prey on human carelessness or a lack of overall awareness of security issues. It might seem as if the attributes of a phishing attack are known to everyone.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















