Your hot hands can give away your smartphone PIN
 If you were protecting your smartphone passcode from someone lurking over your shoulder, or from unseen security cameras, you might cover the screen as you tap in the PIN’s four or six digits.
If you were protecting your smartphone passcode from someone lurking over your shoulder, or from unseen security cameras, you might cover the screen as you tap in the PIN’s four or six digits.
But once you’ve unlocked the phone, perhaps you’d let down your guard, and leave the screen in full view — especially if it’s off. That would be unwise, according to researchers at two German universities. At an upcoming conference, they will present a new study that explains how someone armed with a thermal-imaging camera would have little trouble extracting your passcode from the heat signature left on your smartphone’s screen.
Read moreHackers are using Mac malware to track Iranian activists
 In response to more activists using Apple Mac computers instead of Windows PCs, suspected Iranian government hackers have apparently developed their own Mac-based malware, according to a new report from security researchers.
In response to more activists using Apple Mac computers instead of Windows PCs, suspected Iranian government hackers have apparently developed their own Mac-based malware, according to a new report from security researchers.
The finding highlights the constant ebb-and-flow of governments disrupting and tracking activist movements. As one group adopts a new tool or technique, state-sponsored hackers may need to adapt to get the information they're after. "This demonstrates that Iranian actors are responsive to their environment," Collin Anderson, one of the security researchers behind the report, told in an email.
Read moreHoneywell SCADA controllers exposed passwords in clear text
 A series of remotely exploitable vulnerabilities exist in a popular web-based SCADA system made by Honeywell that make it easy to expose passwords and in turn, give attackers a foothold into the vulnerable network.
A series of remotely exploitable vulnerabilities exist in a popular web-based SCADA system made by Honeywell that make it easy to expose passwords and in turn, give attackers a foothold into the vulnerable network.
The flaws exist in some versions of Honeywell’s XL Web II controllers, systems deployed across the critical infrastructure sector, including wastewater, energy, and manufacturing companies. An advisory from the Department of Homeland Security’s Industrial Control Systems Cyber Emergency Response Team warned about the vulnerabilities. It’s unclear how widespread the usage of Honeywell’s XL Web II controllers is.
Read moreClash of Clans forum hack: Developer Supercell admits breach that hit 1.1 million accounts
 Supercell, the developers of mobile game Clash of Clans, has confirmed the details of users on its official community forum that have been stolen by hackers. A breach notification website, LeakBase, claims that the leak involves roughly 1.1 million accounts.
Supercell, the developers of mobile game Clash of Clans, has confirmed the details of users on its official community forum that have been stolen by hackers. A breach notification website, LeakBase, claims that the leak involves roughly 1.1 million accounts.
The hacked information reportedly includes usernames, email addresses, hashed passwords and IP addresses, according to experts who obtained and verified a small number of the forum's total accounts. Like many hacks before it, the incident has been blamed on forum-making software vBulletin. The Helsinki-based firm released a statement about the incident.
Read more“123456” is the most common password
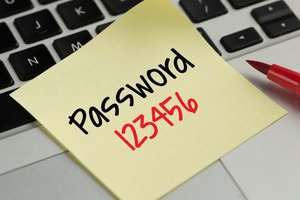 It looks like Internet users never learn from their own mistakes. A research published the past weekend by Keeper Security reveals that the most popular password in 2016 was “123456,” which is arguably the password that can be not hacked, but guessed the easiest.
It looks like Internet users never learn from their own mistakes. A research published the past weekend by Keeper Security reveals that the most popular password in 2016 was “123456,” which is arguably the password that can be not hacked, but guessed the easiest.
No less than 17 percent of the users set this particular password for their accounts, the research reveals after the parent company analyzed data from 10 million passwords that went public after breaches. The number two most popular password in 2016 is a bit more complex because these people do care about their security (end of sarcasm note): “123456789” is currently the runner-up password.
Read moreThis device lets you steal a Mac encryption password in 30 seconds
 If you’re paranoid, and you know what hackers can do when they can get their hands on your computer even for just a few moments, you probably already know that you shouldn’t leave your laptop unattended.
If you’re paranoid, and you know what hackers can do when they can get their hands on your computer even for just a few moments, you probably already know that you shouldn’t leave your laptop unattended.
Now, if you’re an Apple user, you have another great reason not to do that. Using a contraption that costs around $300 and some open source software, a hacker could steal your MacBook password from your own laptop while it’s sleeping or locked in just 30 seconds. This would allow them to unlock the computer and even decrypt the files on your hard drive. In other words, game over. As it turns out, Mac stores the password in memory in cleartext.
Read moreFacebook buys leaked passwords from black market
 Facebook is reportedly buying stolen passwords that hackers are selling on the underground black market in an effort to keep its users' accounts safe.
Facebook is reportedly buying stolen passwords that hackers are selling on the underground black market in an effort to keep its users' accounts safe.
On the one hand, we just came to know that Yahoo did not inform its users of the recently disclosed major 2014 hacking incident that exposed half a billion user accounts even after being aware of the hack in 2014. On the other hand, Facebook takes every single measure to protect its users' security even after the company managed to avoid any kind of security scandal, data breach or hacks that have recently affected top notch companies. Facebook provides you a whole bunch of tools to tighten up the security of your account.
Read moreMeet PoisonTap, the $5 tool that hijacks password-protected computers
 The perils of leaving computers unattended just got worse, thanks to a newly released exploit tool that takes only 30 seconds to install a privacy-invading backdoor, even when the machine is locked with a strong password.
The perils of leaving computers unattended just got worse, thanks to a newly released exploit tool that takes only 30 seconds to install a privacy-invading backdoor, even when the machine is locked with a strong password.
PoisonTap runs freely available software on a $5 Raspberry Pi Zero device. Once the payment card-sized computer is plugged into a computer's USB slot, it intercepts all unencrypted Web traffic, including any authentication cookies used to log in to private accounts. PoisonTap then sends that data to a server under the attacker's control. The hack also installs a backdoor that makes the owner's Web browser and local network remotely controllable by the attacker.
Read more100 guesses is enough to crack your password
 You probably know a trick or two to help strengthen your passwords by now. You might work in a number or two, or maybe even toss in a little punctuation to make it harder for the bad guys to figure out.
You probably know a trick or two to help strengthen your passwords by now. You might work in a number or two, or maybe even toss in a little punctuation to make it harder for the bad guys to figure out.
Perhaps you sneak in the name of a site or the first letter of its name to change things up. Whatever you’re doing, it’s probably not enough. Experts describe how they were able to successfully crack some passwords in fewer than 100 guesses. Even if someone was typing those guesses in manually, that’s a ridiculously small amount of effort. Their algorithm, called TarGuess, achieved success rates of up to 73% in some test scenarios.
Read moreWi-Fi signal interference can leak your passwords and keystrokes
 Hackers can steal your sensitive information, such as your Passwords, PINs and Keystrokes, from your phone by observing changes in the wireless signal as you enter them into your smartphones.
Hackers can steal your sensitive information, such as your Passwords, PINs and Keystrokes, from your phone by observing changes in the wireless signal as you enter them into your smartphones.
A group of researchers from the Shanghai Jaio Tong University have demonstrated a new technique that can reveal private information by analyzing the radio signal Interference, using just one rogue Wi-Fi hotspot. Dubbed WindTalker, the attack sniffs a user's fingers movement on the phone's touchscreen or a computer's keyboard by reading the radio signal patterns called Channel State Information.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















