Norton antivirus overhauls consumer products from 9 to 1
 Beginning Sept. 23, Symantec will shift from having nine versions of its consumer-oriented Norton antivirus program to just one — Norton Security. "We're kind of catching up with our customers," said Fran Rosch,vice president of Norton's business unit.
Beginning Sept. 23, Symantec will shift from having nine versions of its consumer-oriented Norton antivirus program to just one — Norton Security. "We're kind of catching up with our customers," said Fran Rosch,vice president of Norton's business unit.
"When they call in and we ask them 'Which Norton product do you have?' they always just say 'I have Norton.'" Norton is computer security giant Symantec's consumer-oriented division. Using something akin to the Netflix model, the program will allow each customer to sign up for one account which can be applied to multiple devices, including desktop and laptop computers, smartphones and tablets.
Read moreYour smartphone can spy on you without permission
 Your Android phone can be turned into a microphone without your permission or knowledge. All that’s needed are the gyros in your phone that measure orientation. Stanford researchers have shown how to rewire them to pick up sound waves.
Your Android phone can be turned into a microphone without your permission or knowledge. All that’s needed are the gyros in your phone that measure orientation. Stanford researchers have shown how to rewire them to pick up sound waves.
Together with the defense firm Rafael, they created an Android app called Gyrophone, which shows just how easy it is to get the vibrating pressure plates used by the gyroscope to pick up vibrations of sound at frequencies in the 80-250Hz range – the base frequencies of the human voice. “We show that the MEMS gyroscopes found on modern smartphones are sufficiently sensitive to measure acoustic signals in the vicinity of the phone.
Read moreTwitter: 23 million active users are actually bots
 A new SEC filing says more than 8% of the accounts on the social media site are automated. While these bots may provide some kind of public service information, they may also be created to drum up buzz about a company or artificially boost a user's number of followers.
A new SEC filing says more than 8% of the accounts on the social media site are automated. While these bots may provide some kind of public service information, they may also be created to drum up buzz about a company or artificially boost a user's number of followers.
The social network currently has 271 million active users but, according to a new filing with the Security and Exchange Commission, over 8% of them aren't operated by humans. One of Twitter's big selling points, whether it be to music fans, grass roots political activists, sports obsessives, movie buffs or journalists, is that it breaks down the barriers between you and the person or the subject that most interests or excites you.
Read moreApple started negotiations with the medical companies for HealthKit
 In anticipation of the launch of the new operating system iOS 8, the company Apple started negotiations with working in health organizations about the deployment of the service HealthKit.
In anticipation of the launch of the new operating system iOS 8, the company Apple started negotiations with working in health organizations about the deployment of the service HealthKit.
Platform HealthKit, presented at the developer conference WWDC 2014 will allow to gather in one place from a variety of sources of data on the user’s vital signs, including pulse, blood pressure, cholesterol and sugar, the amount of steps you’ve walked and calories burned, and make recommendations to maintain your health and even notify the attending physician in the case of the emergence of anxiety symptoms. Service HealthKit, as the application Health, integrated into iOS, 8, which will be released this fall.
Read moreCloudBot is a free, malwareless, alternative to traditional Botnets
 Researchers take advantage of cloud service providers' free trials and lousy anti-automation controls to use cloud instances like bots.
Researchers take advantage of cloud service providers' free trials and lousy anti-automation controls to use cloud instances like bots.
Thrifty attackers, are you tired of investing your dollars in a botnet that's constantly being disrupted by new anti-virus signatures and bot downtime? A "cloudbot" might be just what you seek. As shown at Black Hat last week by Rob Ragan and Oscar Salazar, senior security associates at Bishop Fox, cloudbots are entirely free and very resilient, and they offer all the uptime of a cloud service with no need for malware. Good news for bot masters working on the cheap.
Read moreNow it is possible to watch hackers‘ attacks in real time
 Think you’re safe on the internet? Think again: Map reveals millions of cyber-attacks happening around the world in real time
Think you’re safe on the internet? Think again: Map reveals millions of cyber-attacks happening around the world in real time
A fascinating interactive map from security firm Norse serves as a stark reminder to just how dangerous the web can be. The live graphic plots every attack taking place on the internet, in real-time and reveals the number of attacks, where the attacks originate, and which locations they are aimed at. Norse’s interactive live map, allows viewers to watch as live attacks unfold around the world. The most popular target seems to be the U.S., with many attacks originating in China.
Read moreTwo examples of commercial censorship
 Two examples of commercial censorship: the first is American hotel fines guests $500 for bad reviews and the second one is French judge orders food blogger to pay €2500 for writing negative review.
Two examples of commercial censorship: the first is American hotel fines guests $500 for bad reviews and the second one is French judge orders food blogger to pay €2500 for writing negative review.
A New York hotel has a rather bizarre booking policy - it charges wedding couples $500 for every bad review left online by their guests. The Union Street Guest House said that it levies the fines because visitors "may not understand" its vintage interior and period furniture. "If your guests are looking for a Marriott type hotel they may not like it here," the inn added. According to the hotel's wide-ranging terms and conditions, a couple making a wedding booking will have the fine deducted from their deposit "for every negative review of USGH placed on any internet site by anyone in your party".
Read moreHow to spy on someone using a bag of potato chips?
 Researchers and scientists from the Massachusetts Institute of Technology (MIT) have figured out a way to reproduce sound using the most fantastic and weirdest of "microphones."
Researchers and scientists from the Massachusetts Institute of Technology (MIT) have figured out a way to reproduce sound using the most fantastic and weirdest of "microphones."
These boffins have captured speech reflected off everyday objects such as a glass of water, a potted plant and a bag of chips. In effect, these objects become "microphones" that can record vibrations with the aid of a high speed camera. In collaboration with Microsoft and Adobe, MIT scientists developed a method that uses vibrations on reflective surfaces to eavesdrop on conversations. Instead of using expensive, professional equipment such as lasers, this ingenious method uses everyday objects to extract sound vibrations turned into audio from high speed video.
Read moreConcept Google contact lens for the password "input"
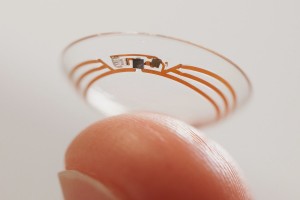 Google is developing smart contact lens that can identify a person faster and easier. In the bowels of Google X actively pursuing smart contact lenses that can help diabetics control glucose levels in the blood.
Google is developing smart contact lens that can identify a person faster and easier. In the bowels of Google X actively pursuing smart contact lenses that can help diabetics control glucose levels in the blood.
However, the ideas of science fiction in respect of contact lenses does not end there - Google has released a couple of new patents relating to this topic. If Google is able to translate his ideas into practice in the future we can have contact lenses that transform the human eye in a simple and rapid means of identification. As is known, the iris of the human eye is unique and can act as one of the biometric identifiers of the individual. Process Google patent consists of three stages. First - the delivery of light to the iris.
Read moreElectronic DNA is not a fantasy, but the near future
 According to The Guardian, every year the information security standards increase their quality. In order to identify the user such patterns as speed of typing, the manner of movement of the cursor and how the user holds a phone can be used.
According to The Guardian, every year the information security standards increase their quality. In order to identify the user such patterns as speed of typing, the manner of movement of the cursor and how the user holds a phone can be used.
Researches from University of Oxford suppose that habits and manners of people‘s behavior will be applied for secure login on personal computer and mobile devices. Peculiarities of human behavior such as typing speed, the manner of movement of the cursor and how the user holds a phone can be used to user‘s authentication. Scientists called it “electronic DNA”(eDNA) or electronically Defined Natural Attributes.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















