An encrypted messaging service has been infiltrated by police
 Hundreds arrested after police infiltrate secret criminal phone network
Hundreds arrested after police infiltrate secret criminal phone network
An encrypted messaging service used exclusively by criminals has been infiltrated by police in a major operation, leading to hundreds of arrests and the seizure of firearms, drugs, and millions of dollars in cash.
Two-Factor Authentication What Is It and Why You Should Use It
 Most people are becoming familiar with the idea of two-factor authentication. But whether everyone realizes why it’s so important?
Most people are becoming familiar with the idea of two-factor authentication. But whether everyone realizes why it’s so important?
The post is a guide to two-factor authentication, its importance, and its nuances.
Logins via the long-accepted username and password method have grown increasingly insecure. Unfortunately, many users make use of the same username and password or rotate through a small number of login combinations. This makes it easier for hackers who might have gained access to user data in the data breaches we seem to hear about almost daily.
Read moreEncryption is under threat - this is how it affects you

What is encryption?
Encryption is the encoding of information such that only authorized parties may access it at the message’s final destination. One of the earliest examples of encryption – and the most cited in literature on the subject – is the Caesar cipher, a substitution cipher where each letter of a message is shifted 3 characters.
Should Big Decisions Be Based on Data or Your Intuition?
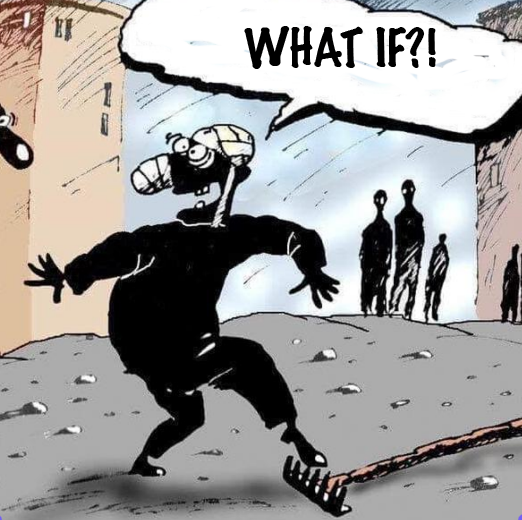 When making an important decision, should you trust your gut, or gather more information before deciding?
When making an important decision, should you trust your gut, or gather more information before deciding?
There are two factors to consider...
VPNFilter malware infecting 500,000 devices is worse than we thought
 Two weeks ago, officials in the private and public sectors warned that hackers working for the Russian government infected more than 500,000 consumer-grade routers in 54 countries with malware that could be used for a range of nefarious purposes.
Two weeks ago, officials in the private and public sectors warned that hackers working for the Russian government infected more than 500,000 consumer-grade routers in 54 countries with malware that could be used for a range of nefarious purposes.
Now, researchers say additional analysis shows that the malware is more powerful than originally thought and runs on a much broader base of models, many from previously unaffected manufacturers. The most notable new capabilities found in VPNFilter, as the malware is known, come in a newly discovered module that performs an active man-in-the-middle attack on incoming Web traffic.
Read moreHackers target Booking.com in criminal bid to steal hundreds of thousands from customers
 Cyber crooks have targeted travel firm Booking.com in a bid to steal hundreds of thousands of pounds from customers. Users were sent WhatsApp and text messages claiming a security breach meant they needed to change their password.
Cyber crooks have targeted travel firm Booking.com in a bid to steal hundreds of thousands of pounds from customers. Users were sent WhatsApp and text messages claiming a security breach meant they needed to change their password.
But the link gave hackers access to bookings and they then sent follow-up messages demanding full payment for holidays in advance with bogus bank details provided. These appeared genuine as they included personal data including names, addresses, phone numbers, dates and prices of bookings, and reference numbers. Marketing manager David Watts got a WhatsApp message but realised it was a scam.
Read moreOperator of World's Top Internet Hub Sues German Spy Agency
 The BND foreign intelligence service has long tapped international data flows through the De-Cix exchange based in the German city of Frankfurt. But the operator argues the agency is breaking the law by also capturing German domestic communications.
The BND foreign intelligence service has long tapped international data flows through the De-Cix exchange based in the German city of Frankfurt. But the operator argues the agency is breaking the law by also capturing German domestic communications.
"We have grave doubts about the legality of the current practice," said a statement Wednesday on the website of De-Cix Management GmbH, which is owned by European internet industry body the eco association. "We consider ourselves under obligation to our customers to work towards a situation in which strategic surveillance of their telecommunications only takes place in a legal manner."
Read moreUS says North Korea behind malware attacks
 The Trump administration issued a fresh warning Tuesday about malicious North Korean cyber activity, as that nation's leader dispatched a top adviser to New York to prepare for a possible summit on its nuclear arsenal.
The Trump administration issued a fresh warning Tuesday about malicious North Korean cyber activity, as that nation's leader dispatched a top adviser to New York to prepare for a possible summit on its nuclear arsenal.
The technical alert from the FBI and the Department of Homeland Security highlighted two pieces of malware said to have been used to target U.S. infrastructure and aerospace, financial and media companies for at least nine years to steal information and remotely manipulate networks. In recent years, the US has accused North Korea of launching a slew of cyberattacks, and it wasn't immediately clear if there was any significance to the timing of the latest warning.
Read moreFacebook and Google targeted as first GDPR complaints filed
 Facebook and Google have become the targets of the first official complaints of GDPR noncompliance, filed on the day the privacy law takes effect across the EU.
Facebook and Google have become the targets of the first official complaints of GDPR noncompliance, filed on the day the privacy law takes effect across the EU.
Across four complaints, related to Facebook, Instagram, WhatsApp and Google’s Android operating system, European consumer rights organisation Noyb argues that the companies have forced users into agreeing to new terms of service, in breach of the requirement in the law that such consent should be freely given. Max Schrems, the chair of Noyb, said: “Facebook has even blocked accounts of users who have not given consent.”
Read moreA new reason to not buy these cheap Android devices
 Researchers at Avast Threat Labs say that more than 100 different low-cost Android devices from manufacturers like ZTE, Archos, and myPhone come with malware pre-installed. Users in more than 90 countries, including the US, are said to be infected. The good news is there’s a fix.
Researchers at Avast Threat Labs say that more than 100 different low-cost Android devices from manufacturers like ZTE, Archos, and myPhone come with malware pre-installed. Users in more than 90 countries, including the US, are said to be infected. The good news is there’s a fix.
According to the report, this adware variant has been in the wild for three years. It’s called “Cosiloon” and was first noticed by Dr. Web in 2016. Because it’s located in the device’s firmware, it’s extremely difficult to remove. Avast has detected its presence on 18,000 of its users’ devices, so far.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















