Little anonymous or who finances Tor?
 For a long time many people use Tor for information security. The Department of State expenses were increased in 2,5 times, and the government of the USA invests more than 47% money in the Tor network now.
For a long time many people use Tor for information security. The Department of State expenses were increased in 2,5 times, and the government of the USA invests more than 47% money in the Tor network now.
The Tor Corporation has published the financial report for 2013 that on the Tor project which gives users the chance to remain anonymous, more 47% budgetary funds of the USA were spent. In 2012 Tor Project received from the government $1,24 million, and in 2013 – $1,82 million, from them $882,3 were allocated by the Department of State, the Ministry of Defence of the USA donated $830,3 thousand, the National Science Foundation handed over $100,3 thousand and $10 were given by the Agency for International Development (USAID).
Read more375m customer data records were compromised
 More than 175 million customer records of personal and financial information were compromised between April and June due to 237 data breaches, bringing the total number of records stolen for the first half of this year to 375 million, a new report has said.
More than 175 million customer records of personal and financial information were compromised between April and June due to 237 data breaches, bringing the total number of records stolen for the first half of this year to 375 million, a new report has said.
The report released by the SafeNet, Inc., a global leader in data protection solutions, said more than 375 million customer records were stolen or lost as a result of 559 breaches worldwide in the first half of this year. "Even amidst continued warnings about data security, the breach epidemic is trending in the wrong direction. 2014 has proven to be more of the same, with 375 million customer records stolen in the first six months alone," said Sebastien Pavie, Regional Sales Director Middle East and Africa, SafeNet.
Read moreAirplanes can be hacked via Wi-Fi
 Almost a year ago, at the ‘Hack In The Box’ security summit in Amsterdam, a security researcher at N.Runs and a commercial airline pilot, Hugo Teso presented a demonstration that it's possible to take control of aircraft flight systems and communications using an Android smartphone and some specialized attack code.
Almost a year ago, at the ‘Hack In The Box’ security summit in Amsterdam, a security researcher at N.Runs and a commercial airline pilot, Hugo Teso presented a demonstration that it's possible to take control of aircraft flight systems and communications using an Android smartphone and some specialized attack code.
Quite similar to the previous one, a security researcher claims to have devised a method that can give cyber criminals access to the satellite communications equipment on passenger jets through their WiFi and in-flight entertainment systems. Santamarta research paper titled “SATCOM Terminals: Hacking by Air, Sea and Land” explains that ships, aircraft and industrial facilities are all at risk of being compromised — perhaps with catastrophic results.
Read moreGoogle gives child pornography email evidence to police
 Federal law requires people and companies to report child exploitation when they see it. This includes Google, whose automated eyes tipped law enforcement about a Houston-area man whom the police say was using the company’s Gmail service to email pornographic images of a child.
Federal law requires people and companies to report child exploitation when they see it. This includes Google, whose automated eyes tipped law enforcement about a Houston-area man whom the police say was using the company’s Gmail service to email pornographic images of a child.
The man, John Henry Skillern, 41, was arrested and charged with promotion and possession of child pornography. According to the police, the arrest was set in motion when Google sent a tip to the National Center for Missing & Exploited Children. The group alerted David Nettles, a detective in Webster, Tex., who works full time for the Houston Metro Internet Crimes Against Children Task Force.
Read moreFacebook sued by law student Max Schrems for privacy violations

An Austrian man is fronting a class action lawsuit against Facebook for violations of European privacy laws. Law student Max Schrems announced today that he is suing Facebook subsidiary Facebook Ireland in a commercial court in Vienna, Austria. Mr. Schrems is bringing the lawsuit against Facebook for violations regarding: “[t]he privacy policy, participation in the PRISM program, Facebook’s graph search, apps on Facebook, tracking on other web pages (e.g. via the “like buttons”), ‘big data’ systems that spy on users or the non-compliance with access requests,” according to the group’s website FBClaim.com.
Read moreTor anonymity service says its network was hacked
 The Tor encryption service is a high-profile bastion of computer security, but the project appears to have been compromised earlier this year.
The Tor encryption service is a high-profile bastion of computer security, but the project appears to have been compromised earlier this year.
Today, the Tor Project blog announced that an unknown party likely managed to gather information about people who were looking up hidden services — websites that users can operate and visit anonymously, like Silk Road — and could theoretically have compromised other parts of the network. Anyone who used Tor between early February and July 4th of 2014 "should assume they were affected" by the attack, says the Tor team. But they don't know what exactly that means.
Read moreConcept Google contact lens for the password "input"
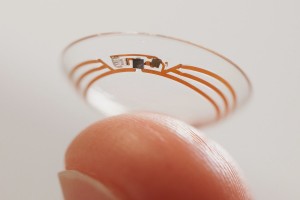 Google is developing smart contact lens that can identify a person faster and easier. In the bowels of Google X actively pursuing smart contact lenses that can help diabetics control glucose levels in the blood.
Google is developing smart contact lens that can identify a person faster and easier. In the bowels of Google X actively pursuing smart contact lenses that can help diabetics control glucose levels in the blood.
However, the ideas of science fiction in respect of contact lenses does not end there - Google has released a couple of new patents relating to this topic. If Google is able to translate his ideas into practice in the future we can have contact lenses that transform the human eye in a simple and rapid means of identification. As is known, the iris of the human eye is unique and can act as one of the biometric identifiers of the individual. Process Google patent consists of three stages. First - the delivery of light to the iris.
Read moreHackers hacked Gizmodo Blog
 The main page Gizmodo was changed. Hackers have made all the users to be redirected to another web-page with the help of optional script.
The main page Gizmodo was changed. Hackers have made all the users to be redirected to another web-page with the help of optional script.
The group of attackers compromised the well-known design Gizmodo`s reputation. Attackers tried to hack the site in order to spoil their reputation. Hackers changed the page of Brazilian web-portal Gizmodo by adding the script with the help of which guests of the site were redirected to an absolutely another page. The page on which the users were redirected was located in Sweden, under the domain name .se. The sheathing for server control was loaded on a site.
Read moreChina denies hacking Canadian tech research group
 A Chinese official said Thursday that Canada should withdraw its accusation that China was behind the hacking of Canada's top technology development organization.
A Chinese official said Thursday that Canada should withdraw its accusation that China was behind the hacking of Canada's top technology development organization.
"It is irresponsible for the Canadian side to make groundless accusations against China when there is no credible evidence," Foreign Ministry spokesman Qin Gang said. "We are strongly opposed to that." Canada's Treasury Board said on Tuesday that a "highly sophisticated Chinese state-sponsored actor" hacked into the National Research Council, which partners with private industry to bring new technologies to market. The government said one of Canada's spy agencies detected the cyberattack and the council's computers were isolated as a precaution.
Read moreElectronic DNA is not a fantasy, but the near future
 According to The Guardian, every year the information security standards increase their quality. In order to identify the user such patterns as speed of typing, the manner of movement of the cursor and how the user holds a phone can be used.
According to The Guardian, every year the information security standards increase their quality. In order to identify the user such patterns as speed of typing, the manner of movement of the cursor and how the user holds a phone can be used.
Researches from University of Oxford suppose that habits and manners of people‘s behavior will be applied for secure login on personal computer and mobile devices. Peculiarities of human behavior such as typing speed, the manner of movement of the cursor and how the user holds a phone can be used to user‘s authentication. Scientists called it “electronic DNA”(eDNA) or electronically Defined Natural Attributes.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















