Hackers found a way to disable car airbags system
Car Hacking is a hot topic today. Today, many automobiles companies are offering vehicles that run on the mostly drive-by-wire system, which means that a majority of car's functions are electronically controlled, from instrument cluster to steering, brakes, and accelerator.
 No doubt these auto-control systems makes your driving experience better, but at the same time they also increase the risk of getting hacked. Previously researchers demonstrated how hackers can remotely hijack your car to control its steering, brakes and transmission.
No doubt these auto-control systems makes your driving experience better, but at the same time they also increase the risk of getting hacked. Previously researchers demonstrated how hackers can remotely hijack your car to control its steering, brakes and transmission.
And Now… According to a team of security researchers, Hackers can successfully disable car's airbags – as well as other functions – by exploiting a zero-day vulnerability in third-party software that is commonly used by car mechanics. The team, including András Szijj and Levente Buttyán of CrySyS Lab, and Zsolt Szalay of Budapest University, demonstrated the hack on an Audi TT car sold by Volkswagen, and said any car brand potentially hackable. This is because the vulnerability doesn’t exist in VW itself and relates solely to third-party software widely used and compatible with cars sold by the Volkswagen as well as other companies.
How Does the Hack Work?
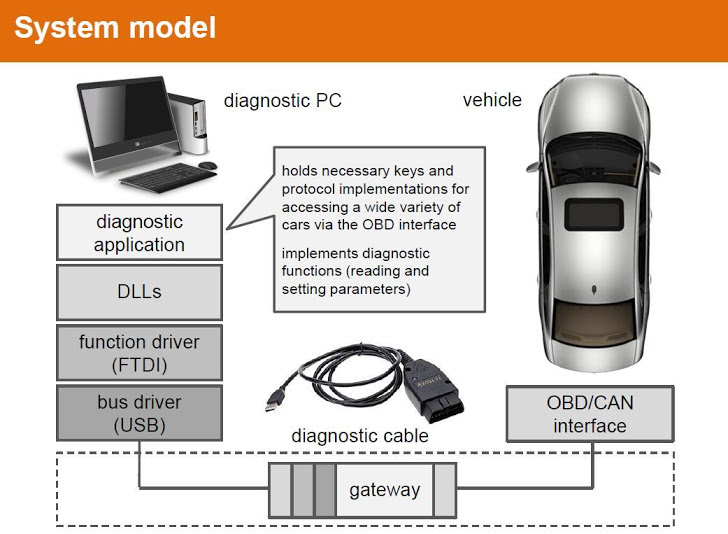
Many mechanics make use of this software to run diagnostics. Hacking car requires: a mechanic's PC to be compromised or a malicious USB to be plugged into the vehicle. One of the above two options is needed for the working of exploit. The attack replaces the FTDI DLL – used to communicate with the diagnostic cable – with a malicious version, which according to the trio, is the easiest means of owning connected cars. Once infected, the hacker can take control of the car's diagnostic system, allowing items to be switched ON or OFF without even driver’s knowledge.
"Anything that can be switched on or off from the diagnostic application could have been switched on or off," Buttyán told the Reg. "After switching off the airbag, we can consistently report to the application that it is still switched on." Researchers found difficulty in reverse engineering the software and protocols used to make their attack work, but they said the hack is completely feasible for a reasonably skilled hacker.
What's even Worse?
Moreover, the hack could be made more dangerous if hackers could somehow update a car's embedded control unit firmware via the OBD2 port, allowing them to inject a backdoor to be triggered later on while the car is in motion.
The trio said their work is a proof-of-concept (POC) of prior 2011 research paper [PDF] by Stephen Checkoway, titled "Comprehensive Experimental Analyses of Automotive Attack Surfaces," who described the possible ways to infect a car through diagnostic equipment. For in-depth information about the recent hack, you can go through these slides [PDF], describing "Hacking cars in the style of Stuxnet."
Axarhöfði 14,
110 Reykjavik, Iceland














