13 million passwords appear to have leaked from free web host
A security researcher has discovered a trove of more than 13 million plaintext passwords that appear to belong to users of 000Webhost, a service that says it provides reliable and high-speed webhosting for free.

The leaked data, which also includes users' names and e-mail addresses, was obtained by Troy Hunt, an Australian researcher and the operator of Have I Been Pwned?, a service that helps people figure out if their personal data has been exposed in website breaches.
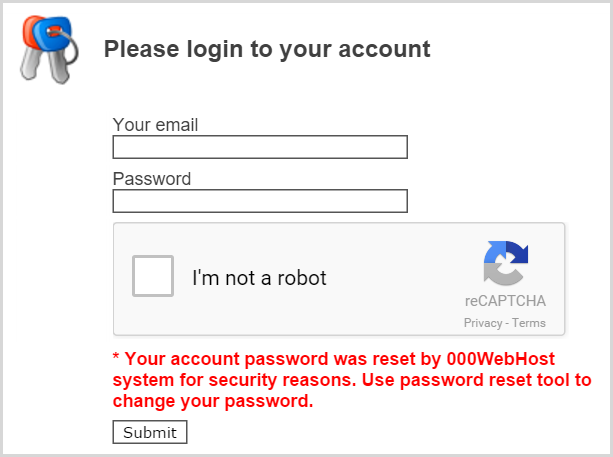
Hunt received the data from someone who contacted him and said it was the result of a hack five months ago on 000Webhost. Hunt has so far confirmed with five of the people included in the list that it contains the names, passwords, and IP addresses they used to access 000Webhost. "By now there’s no remaining doubt that the breach is legitimate and that impacted users will have to know," he wrote in a blog post published Wednesday. He said that he worked hard to notify company officials and get them to publicly warn users that their passwords have been exposed. So far, all that's happened, he said, is that the service has notified users who log in that their passwords have been reset "by 000Webhost system for security reasons."
In a Facebook post published Wednesday morning, 000Webhost officials confirmed the breach and said it was the result of hackers who exploited an old version of the PHP programming language to gain access to 000Webhost systems. The advisory makes no reference to the plaintext passwords, although it does advise users to change their credentials. Hunt has also encountered evidence the breach may extend to other Web hosting providers, presumably because of partnerships they had with 000Webhost.
Hunt uncovered a variety of weaknesses, including the use of unencrypted HTTP communications on the login page and a code routine that placed a user's plaintext password in the resulting URL. That means the unobfuscated passwords were likely written to all kinds of administer logs. It's also possible that the site didn't follow standard industry practices and cryptographically hash the passwords when storing them. In any event, the data may have been accessed by executing a SQL injection exploit or other common website attack or by an insider with privileged access to the 000Webhost system.
As password leaks go, 13 million is a large number, but it's still dwarfed by some of the biggest breaches. The recent compromise of clandestine affairs website Ashley Madison, for instance, spilled 34 million passwords. Then again, Ashley Madison administrators went through the trouble of hashing passwords using the extremely onerous bcrypt function (although a critical programming error ultimately made it possible to crack 11 million passwords). Although not perfect, the measure gave Ashley Madison users time to change their passwords and required a fair amount of effort on the part of crackers. By contrast, the availability of plaintext passwords here makes it easy to abuse the passwords and means that even extremely strong passcodes are instantly available.
Anyone who has used 000Webhost should be on the alert for fraud. In the event that users have used the same or a similar password on other websites, they should change it immediately. The fresh infusion of 13 million passwords into the already massive corpus of existing passwords should bring new urgency to the oft-repeated admonition to use a long, randomly generated password that's unique to every site. Advice on how to do that is here.
Axarhöfði 14,
110 Reykjavik, Iceland














