Attackers are turning MySQL servers into DDoS bots
Someone has been compromising MySQL servers around the world and using them to mount DDoS attacks. The latest targets of these attacks are an (unnamed) US hosting provider and a Chinese IP address.
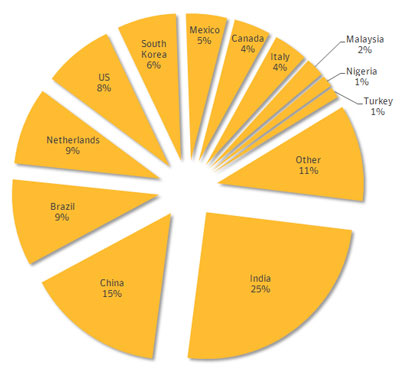
 Most of the servers affected in this campaign are located in India, China, Brazil and the Netherlands, but others can be found around the globe.
Most of the servers affected in this campaign are located in India, China, Brazil and the Netherlands, but others can be found around the globe.
"We believe that the attackers compromised MySQL servers to take advantage of their large bandwidth. With these resources, the attackers could launch bigger DDoS campaigns than if they used traditional consumer targets," Symantec security researchers explained. "MySQL is also the second most popular database management system in the world, giving the attackers a wide range of potential targets." The researchers didn't say how many servers in total were compromised. The attackers used a variant of the Chickdos Trojan to make the servers listen to their commands.
The variant is very similar to the initial Chickdos Trojan first spotted by cyber defenders in December 2013. The attackers perform an SQL injection attack in order to install a malicious user-defined function (UDF) on the target server, which is then loaded into MySQL and executed.
The UDF acts as a downloader, but also modifies registry entries to enable TerminalServices so that the attackers can control the compromised server from a remote location, and sometimes adds a new user to the system. It finally downloads two variants of the Chikdos Trojan from two compromised websites. "In the latest Chikdos campaign that we observed, the attackers likely used an automated scanner or possibly a worm to compromise MySQL servers and install the UDF. However the exact infection vector has not been identified," the researchers noted.
They have provided the hashes for both the downloader and the DoS Trojan, so administrators can check their systems for evidence of compromise. The researchers advised admins never to run SQL servers with administrator privileges (if possible), and to regularly patch apps that use them. They also urged them to follow good programming practices to mitigate SQL injection vulnerabilities, and to check for the presence of new user accounts and to ensure that remote access services are configured securely.
Axarhöfði 14,
110 Reykjavik, Iceland














