Trojanized Android games hide malicious code inside images
Over 60 Android games hosted on Google Play had Trojan-like functionality that allowed them to download and execute malicious code hidden inside images.
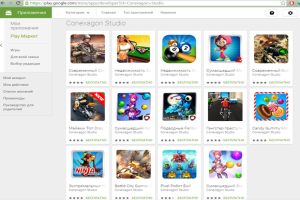 The rogue apps were discovered by researchers from Russian antivirus vendor Doctor Web and were reported to Google last week. The researchers dubbed the new threat Android.Xiny.19.origin.
The rogue apps were discovered by researchers from Russian antivirus vendor Doctor Web and were reported to Google last week. The researchers dubbed the new threat Android.Xiny.19.origin.
Malicious Android apps were a common occurrence on Google Play until a few years ago when Google implemented more rigorous checks. This included an automated scanner called Bouncer that used emulation and behavior-based detection. Bypassing Bouncer detection is not impossible, but is hard enough to keep most malware creators away. Most Android Trojans these days are distributed through third-party app stores, targeting users who have enabled the installation of apps from "unknown sources."
The authors of Android.Xiny.19.origin seem to have been a bit more determined. Their trojanized games are functional, but in the background they collect identifying information from targeted devices.
This information includes the phone's unique IMEI and IMSI identifiers, MAC address, mobile operator, country and language settings, operating system versions and more. The attackers can also instruct the apps to display advertisements, to silently install or delete apps if root access is enabled on the phone and to launch APKs (Android application packages) that are hidden inside images.
The latter functionality, which uses steganography, is the most interesting feature of the malware and makes it harder to detect the malicious code. "Unlike cryptography that is used for encryption of source information, which may arouse suspicion, steganography is applied to hide information covertly," the Dr. Web researchers said in a blog post. "Virus makers presumably decided to complicate the detection procedure expecting that security analysts would not pay attention to benign images."
After a specially crafted image is downloaded from the command-and-control server, the Trojan extracts an APK from it by using a special algorithm. It then loads the malicious code in the device's memory by using the DexClassLoader Android function. The attack is very similar to a concept presented at the Black Hat Europe security conference in October 2014 by researchers Axelle Apvrille and Ange Albertini.
The two researchers showed at the time that they could hide an APK inside an image file while keeping the image valid when opened. However, when applying a decryption algorithm to it, they could recover the APK. Furthermore, the researchers even mentioned that DexClassLoader can be used to dynamically load the APK into memory, exactly as Android.Xiny.19.origin does now.
Axarhöfði 14,
110 Reykjavik, Iceland














