PowerSniff malware used in Macro-based attacks
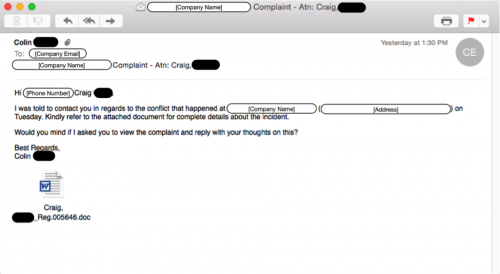
Security researchers have discovered a new kink in the tactics of malware operators, who are now combining spam campaigns, malicious Word documents, and PowerShell code to deliver fileless malware to their targets.
 None of these techniques is new, but they have never been used together until now, showing that malware operators are also paying closer attention to security research and the work of some of their peers, borrowing techniques from each other in their ever-present struggle to evade detection.
None of these techniques is new, but they have never been used together until now, showing that malware operators are also paying closer attention to security research and the work of some of their peers, borrowing techniques from each other in their ever-present struggle to evade detection.
Security researchers from Palo Alto Networks have discovered this campaign, and they're saying that it's relatively small at the moment, having detected only 1,500 of such emails until now. "Facepalm: It's 2016, and people can still get infected via Word macros." Malware operators are using spam emails to deliver infected Word documents to their victims.
Despite the fact that Word's macro feature has been known to be an avenue for delivering malware, there are still countless Microsoft Office installations where Word macros are turned on and will automatically execute when the document is opened.
This means that, in situations where the spam campaign manages to fool users into opening the documents, the malicious macro code will be executed automatically. Palo Alto researchers are saying that, for this campaign, the macro code packed with each malicious document will start a hidden instance of Windows PowerShell, a powerful scripting language added since Windows 7, and then download malicious scripts that will be executed by the PowerShell instance.
"Malware avoids educational and healthcare sectors"
Support is included for both 32-bit and 64-bit platforms, and the scripts first initiate a series of tests. They will check if the computer is not a virtual machine, if there are no software debugging apps running, and it will then look for "trigger" words in the computer's cache and network configuration.
The string check includes good and bad words. If strings like hospital, school, college, nurse, and doctor are discovered, the script will immediately stop from execution. If strings related to shops, stores, and PoS systems are found on the target, the scripts will proceed to download whatever malware family the C&C servers instruct it to download.
When this happens, the malware, named PowerSniff, is written directly to the computer's memory, without ever touching the user's hard drive, so it won't be subjected to classic antivirus detection procedures. Besides Palo Alto, security researchers from SANS' Internet Storm Center (ISC) have also come across the same campaign and have provided an alternative analysis. At the moment, the spam campaign has mainly targeted users living in countries such as the US, Canada, the UK, France, Germany, Austria, and Poland.
Axarhöfði 14,
110 Reykjavik, Iceland














