Highly complex USB trojan targeting air-gapped systems discovered
Security experts are warning organizations about a new USB trojan that is extremely difficult to spot, can target air-gapped systems, and is ideal for cyber and industrial espionage campaigns.
 Nicknamed USB Thief (detected as Win32/PSW.Stealer.NAI trojan), this is probably the most complex trojan ever discovered, using encryption and self-protection procedures to infect targets and hide from prying eyes.
Nicknamed USB Thief (detected as Win32/PSW.Stealer.NAI trojan), this is probably the most complex trojan ever discovered, using encryption and self-protection procedures to infect targets and hide from prying eyes.
As ESET's Tomáš Gardoň explains, the trojan binds itself on each USB stick, using the USB drive's details (as an encryption key) to hide its malicious files under AES128 encryption. If the trojan is copied to another USB or on a classic storage device, the encryption breaks, and the content of the malicious files cannot be determined. It is clear that USB Thief was implemented for covert operations, where the attacker impregnates one USB at a time, for the sole purpose of targeting one person or organization.
Once the USB stick is plugged into a computer, the trojan steals data like pictures and documents, and stores them in an encrypted format on the same USB drive. After the USB is pulled out of the computer, victims or security researchers investigating the attacked system have no clue as to what happened because the trojan leaves no traces behind on the attacked PC.
"USB Thief can deliver all kinds of threats, not just infostealers"
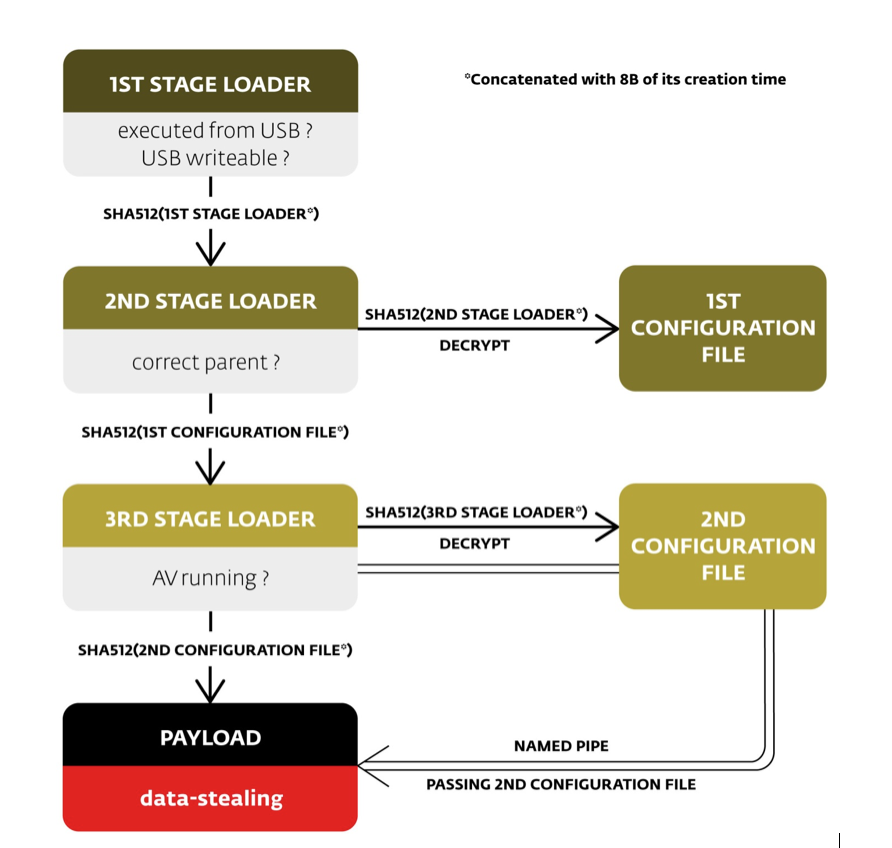
A peculiar USB Thief feature is the presence of a self-protection mechanism that makes reverse engineering extremely difficult. The trojan is composed of four executables and two configuration files. In order to execute, these files have to run in a certain order. If security researchers don't know the exact order in which these files execute, then they can't reproduce the malicious behavior, even if they managed to brute-force the trojan's encryption and have access to its content.
Even worse, the trojan's final infostealing payload can be easily modified. "The (relatively simple) data-stealing payload is very powerful, especially since it does not leave any evidence on the affected computer," Mr. Gardoň explains. "It would not be difficult to redesign the malware to change from a data-stealing payload to any other malicious payload."
"Victims can launch USB Thief without even knowing"
While our above-mentioned infection scenario involves a malicious actor putting the USB Thief-infected trojan in a computer and launching the malicious application, this is not the only attack scenario. Mr. Gardoň says that USB Thief can also be packed as a plugin or add-on for portable applications often installed on USBs, like Firefox, Chrome, TrueCrypt, Notepad++, and so on.
An attacker could find ways to deliver the trojan to the victim's USB, hide it as a plugin in one of those portable apps, and let the victim carry the trojan into air-gapped systems and use it in their own time. When the portable app is launched into execution, the trojan would execute as well, the attacker only needing to show patience to let the attack roll out on its on.
Axarhöfði 14,
110 Reykjavik, Iceland














