Jigsaw ransomware threatens to delete your files
A new ransomware variant called Jigsaw has come to light today, and it threatens and then deletes the user's files if the ransom note is not paid in due time, or when the victim reboots their computer.
 The way this ransomware reaches infected computers is currently unknown. What is known is that once the ransomware's payload is launched into execution, it will target 226 different file types, encrypting their content with an AES algorithm and appending the .fun extension at the end of each file name.
The way this ransomware reaches infected computers is currently unknown. What is known is that once the ransomware's payload is launched into execution, it will target 226 different file types, encrypting their content with an AES algorithm and appending the .fun extension at the end of each file name.
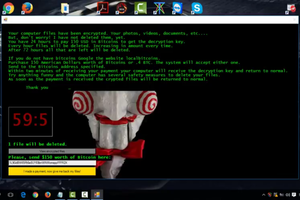
"Jigsaw ransomware uses the .fun file extension". Once this operation finishes, the ransom note is displayed on the user's screen, showing the infamous Jigsaw character from the Saw movie series, hence the ransomware's name. The ransomware asks for 0.4 Bitcoin (~$160) as payment, but there's a catch. To force the user's hand into paying the ransom as quickly as possible, the Jigsaw ransomware threatens to delete some of their files every hour.
The bad part is that the ransomware lives up to its word and actually starts deleting more and more files as the user waits. Even worse, @MalwareHunterTeam discovered that with every PC reboot, the ransomware also deletes an additional 1,000 files.
"Jigsaw ransomware can be decrypted"
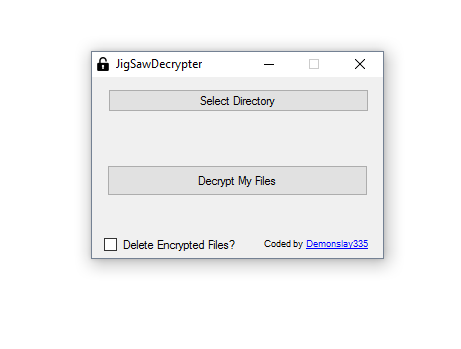
But there is good news as well. Malware analyst Michael Gillespie, along with Lawrence Abrams from Bleeping Computer and the MalwareHunterTeam have found a way to decrypt files locked by the Jigsaw ransomware without paying the ransom.
First things first, you'll need to stop the ransomware's processes. Open the Task Manager and look for the firefox.exe and the drpbx.exe processes in order to shut them down. Then download the JigSawDecrypter, unzip the archive, and launch it into execution. From here on out, it should be pretty self-explanatory how to use this tool.
If you've been reading Softpedia today, you’ve also found out that Mr. Gillespie is the same person who put together a cool site called ID Ransomware, which tells ransomware victims the name of the ransomware that infected their PC. Previously, he also created the decrypter for the CryptoHost (Manamecrypt) ransomware that moved and locked the user's files inside a password-protected RAR file.
Besides Mr. Gillespie and @MalwareHunterTeam, additional malware analysis has been provided by Lawrence Abrams from Bleeping Computer, who also put together a technical write-up on the malware's capabilities. Below we present a YouTube video showcasing a Jigsaw ransomware infection in progress, courtesy of Serbian security researcher GrujaRS.
MalwareHunterTeam told Softpedia that the team of researchers analyzing Jigsaw detected yesterday five new different variants of Jigsaw. These variants are also decryptable, and the researchers have updated the decrypter with the necessary code to help users unlock their files. The update can decrypt Jigsaw ransomware instances that use the .gws, .kkk,and .btc file extensions.
Axarhöfði 14,
110 Reykjavik, Iceland














