Private records of 93.4 million Mexican voters exposed in data breach
The personal information of more than 93.4 million Mexican voters was exposed this week in a massive data breach.
 A leaky database, which was not password-protected, is said to contain Mexican citizens’ names, addresses, dates of birth, as well as occupations and the names of the voters’ parents, according to noted MacKeeper Security Researcher Chris Vickery. The database was reportedly downloaded to an Amazon server by an unknown party.
A leaky database, which was not password-protected, is said to contain Mexican citizens’ names, addresses, dates of birth, as well as occupations and the names of the voters’ parents, according to noted MacKeeper Security Researcher Chris Vickery. The database was reportedly downloaded to an Amazon server by an unknown party.
The database has now been secured. It contained no financial information about the voters, according to Vickery. An official with Mexico’s Instituto Nacional Electoral (INE) said the Amazon server containing the millions of voter records did not belong to the Mexican government. An INE spokesperson was not immediately available for comment. It remains unclear to whom the server belongs.
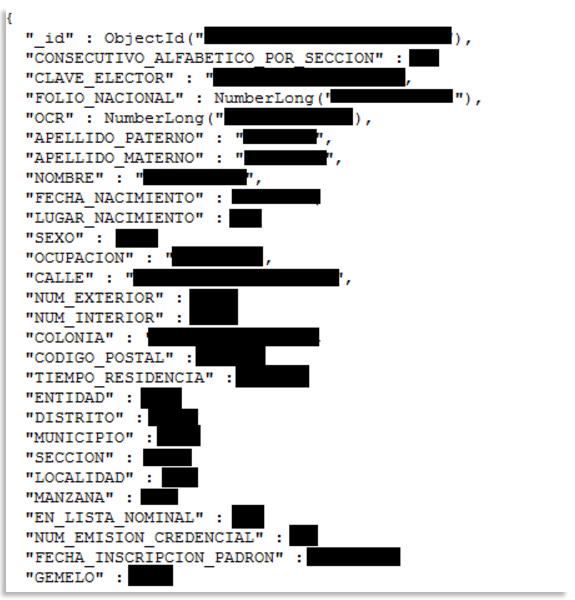
According to Vickery, there was no password or authentication of any kind protecting the information. “It was configured purely for public access,” he said. “Why? I have no clue.” On Friday morning, Vickery provided experts with a screenshot of an individual record, redacted to protect the Mexican citizen’s identity:
Vickery reported the breach to the U.S. State Department and its Office of Mexican Affairs, but the database remained online. He eventually contacted the U.S. Secret Service, the Department of Homeland Security, and the U.S. Computer Emergency Readiness Team (US-CERT), the agency responsible for assessing cyberthreats against the nation. Corresponding with the U.S. government, however, did not result in the database’s removal.
“It was very difficult to get this taken down,” Vickery says. “I eventually went straight to Amazon and worked my way through their abuse reporting system.” Amazon’s automated system for reporting abuse was equally frustrating to navigate, Vickery said. It repeatedly asked him to submit irrelevant information.
He eventually wrote the company back: “This is not an acceptable response. My abuse report clearly explained that the database is a server using MongoDB software. I gave the IP address and port number. That is the only existing connection information available (and it is all you should need).”
Vickery, who considered the leak to have life-threatening implications, continued pleading with Amazon: “The existence of this database is, itself, a violation of federal Mexican law. The server is, at this very moment, allowing the public to copy 93.4 million voter registration records. Under Mexican law, these records are ‘strictly confidential’. People's lives are at stake here. Kidnapping is a considerable problem in Mexico. Right now one of your servers is handing out the home addresses of 93.4 million Mexicans. Is Amazon seriously not willing to do anything about this?”
The database was eventually taken down in the small hours of Friday morning following an email from Amazon that contained an apology. “I’m not sure if it was my abuse report that finally got it taken down or if the Mexican INE got to Amazon,” said Vickery, “but one of us made the difference.”
This isn’t the first time Mexico’s confidential electoral rolls have been discovered on the servers of a U.S. company. In 2003, the Atlanta-based corporation ChoicePoint Inc. acquired extensive personal information on Mexican voters, including passport numbers, which it purchased from a Mexican company for $250,000. In return for the data, ChoicePoint reportedly received a five-year, $67 million contract from the George W. Bush administration. In 2003 alone, ChoicePoint received $11 million from the U.S. government.
A subsidiary of ChoicePoint, Database Technologies, was also hired by the state of Florida during former Gov. Jeb Bush’s administration prior to the 2000 presidential election. The company was supposed to overhaul voter registration lists, but instead of exclusively removing felons from the electoral rolls, thousands of eligible voters were disenfranchised.
Last December, a misconfigured database was identified by Vickery containing the personal information of more than 191 million American voters, including their full names, dates of birth, home addresses, and more. The information was accessible online to anyone who knew the right IP address.
Axarhöfði 14,
110 Reykjavik, Iceland














