Bug hunter found ways to hack any Instagram accounts
How to hack an Instagram account? The answer to this question is difficult to find, but a bug bounty hunter just did it without too many difficulties.
 Belgian bug bounty hunter Arne Swinnen discovered two vulnerabilities in image-sharing social network Instagram that allowed him to brute-force Instagram account passwords and take over user accounts with minimal efforts.
Belgian bug bounty hunter Arne Swinnen discovered two vulnerabilities in image-sharing social network Instagram that allowed him to brute-force Instagram account passwords and take over user accounts with minimal efforts.
Both brute-force attack issues were exploitable due to Instagram’s weak password policies and its practice of using incremental user IDs. "This could have allowed an attacker to compromise many accounts without any user interaction, including high-profile ones," Swinnen wrote in a blog post describing details of both vulnerabilities.
Brute-Force Attack Using Mobile Login API
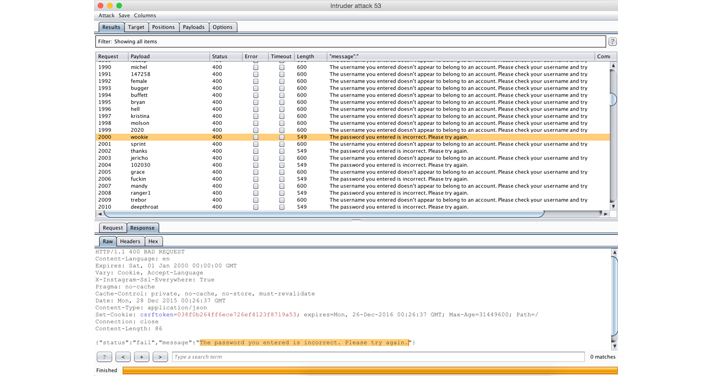
Swinnen discovered that an attacker could have performed brute force attack against any Instagram account via its Android authentication API URL, due to improper security implementations. According to his blog post, for first 1000 incorrect brute-force attempts on Mobile login API, Instagram responds "password you entered is incorrect," but he also noticed that for next 1000 attempts server displays, "username not found" ‒ some sort of rate limiting error responses.
However, Swinnen continued the brute force attack with patience and found that server again started displaying reliable response after the 2,000th attempt, followed by an unreliable responses (i.e. username not found). So, an attacker could create a script that simply mounts a reliable brute-force attack and replays the inaccurate responses until a reliable one was obtained. He developed a script that tested 10,001 passwords against a targeted Instagram account. "The only limitation of this attack was that on average, 2 authentication requests had to be made for one reliable password guess attempt," Swinnen said.
The worst part comes in:
The researcher was able to log into the compromised account from the same IP address that he used for carrying out brute-force attack against the password, which is the worst security practice to protect accounts against unauthorized logins. The first vulnerability was discovered and reported to Facebook by Swinnen in late December.
Brute-Force Attack using the Web-based Registration System
The second brute-force attack vulnerability that affected Instagram's Web registration page was discovered and reported to Facebook in May by the same researcher. The vulnerability could have allowed an attacker to carry out another trivial brute-force attack against the Instagram Web registration endpoint that did not even trigger an account lockout or other security measures.
Swinnen registered a test account on Instagram and recorded the HTTP request sent during registration. However, after replaying the same request removing the username and password parameters, he received an error response saying "Those credentials belong to an active Instagram account."
Since there was no rate limitation activated on the registration page, Swinnen was able to brute force more than 10,000 attempts before sending over the correct username and password and receiving an affirmative response from the page. Facebook awarded the researcher a combined bounty of $5,000 and patched both the vulnerabilities in Instagram by limiting the number of login attempts as well as hardening its password policy.
Now, Instagram no longer allows users to choose simple passwords. It now requires passwords to be a combination of numbers, letters, and punctuation. The company also recommends Instagram passwords not be used elsewhere online. The similar steps should be adopted by every online website and services that are responsible for the security of their users.
Instead of expecting from users to keep their every online password strong and complex, it is websites and developers’ duty to enforce a strong password policy by not allowing users to sign up with weak passwords, as well as recommend users to adopt a password manager.
Axarhöfði 14,
110 Reykjavik, Iceland














