20-year-old Windows bug lets printers install malware
For more than two decades, Microsoft Windows has provided the means for clever attackers to surreptitiously install malware of their choice on computers that connect to booby-trapped printers, or other devices masquerading as printers, on a local area network.
 Microsoft finally addressed the bug on Tuesday during its monthly patch cycle. The vulnerability resides in the Windows Print Spooler, which manages the process of connecting to available printers and printing documents.
Microsoft finally addressed the bug on Tuesday during its monthly patch cycle. The vulnerability resides in the Windows Print Spooler, which manages the process of connecting to available printers and printing documents.
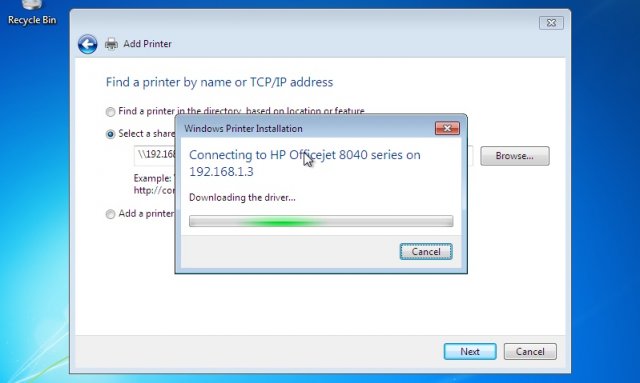
A protocol known as Point-and-Print allows people who are connecting to a network-hosted printer for the first time to automatically download the necessary driver immediately before using it. It works by storing a shared driver on the printer or print server and eliminates the hassle of the user having to manually download and install it. Researchers with security firm Vectra Networks discovered that the Windows Print Spooler doesn't properly authenticate print drivers when installing them from remote locations.
The failure makes it possible for attackers to use several different techniques that deliver maliciously modified drivers instead of the legitimate one provided by the printer maker. The exploit effectively turns printers, printer servers, or potentially any network-connected device masquerading as a printer into an internal drive-by exploit kit that infects machines whenever they connect.
"Not only will that unit be able to infect multiple machines in your network, but it would also be able to re-infect [them] over and over," Vectra researcher Nick Beauchesne wrote in a blog post detailing the vulnerability. "Finding the root cause might be harder since the printer itself might not be your usual suspect. This situation comes to life because we end up delegating the responsibility of holding the driver safely to the printer, and those devices might not be as secure or impregnable as one would hope."
Watering hole attacks
Security expert HD Moore, who is principal at a firm called Special Circumstances, told that there are a variety of ways attackers can go about exploiting the vulnerability. One method is to connect a laptop or other portable device that falsely advertises itself as a network printer. When people on the same network connect to it, the device can be set up to automatically deliver a booby-trapped driver.
Another approach is to monitor traffic set to a legitimate network printer and wait for a victim to add the printer to their system. The attacker would then hijack the request for the printer drivers and respond with a malicious driver. Such a man-in-the-middle attack "can be done over open Wi-Fi or by using ARP spoofing over wired networks," Moore said. "It should be possible to tweak open source MITM tools like Bettercap to accomplish this."
Attackers could also reverse engineer a printer and tamper with its firmware so that it delivers a maliciously modified driver. While this approach may seem unrealistic, it was successfully carried out by the Vectra researchers. A separate bug involving the point-and-print protocol also makes it possible for untrusted users on a network to elevate their account privileges to all-powerful administrator status.
The Vectra researchers tested their exploits on a mix of devices, including an unidentified printer and computers running Windows XP 32bit, Windows 7 32bit, Windows 7 64 bit, Windows 2008 R2 AD 64, Ubuntu CUPS, and Windows 2008 R2 64 print server. In an advisory accompanying Tuesday's patch Microsoft rated the code-execution vulnerability critical for all supported Windows versions. Vectra said the vulnerability dates back to Windows 95.
A word of caution to those concerned about this vulnerability: Moore said Tuesday's update doesn't close the code-execution hole, but rather it merely adds a warning as part of the update. "Knowing how most users respond to warnings, this doesn't seem like an effective approach," he said.
On the brighter side, code-execution attacks won't work in enterprise settings that use Microsoft's Active Directory unless administrators have modified default settings. Still, the attack is likely viable in many homes and small- and medium-sized businesses, especially those that allow people to connect their own devices.
"This is mostly a risk for BYOD laptops within a company, folks using personal laptops on public networks, and corporate networks where the group policy explicitly enables this feature," Moore said. "Convincing someone to add a printer might be tricky, but there may be other ways to drive that behavior through other network attacks, such as by hijacking HTTP requests and telling the user to do so."
Axarhöfði 14,
110 Reykjavik, Iceland














