Malware uses word puzzles to derive C&C server IP address
Malware authors can be quite creative when it comes to avoiding security researchers, but after almost three decades of malware analysis, there are malware families that manage to surprise infosec professionals once in a while.
 Such is the case of a backdoor trojan that Palo Alto Network has detected in two separate cyber-espionage campaigns.
Such is the case of a backdoor trojan that Palo Alto Network has detected in two separate cyber-espionage campaigns.
Palo Alto says the two samples they looked at used a very peculiar and inventive method of determining their C&C servers. CONFUCIUS malware takes novel approach to C&C server resolution. While low-quality malware uses IP addresses hardcoded in its source code, top-shelf threats use dynamic domain name generation algorithm (DGA) in order to hide the real C&C server IP addresses under ever-changing domain names. The two malware samples, which they named CONFUCIUS, didn't use either of these two methods. Researchers say that during analysis, the samples didn't query any out-of-the-ordinary sites, nor employed complex DGAs.
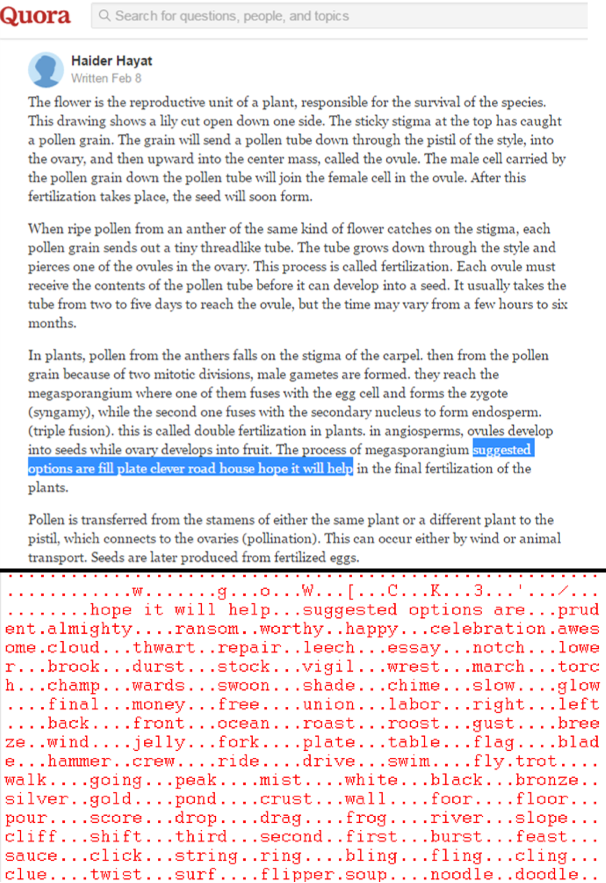
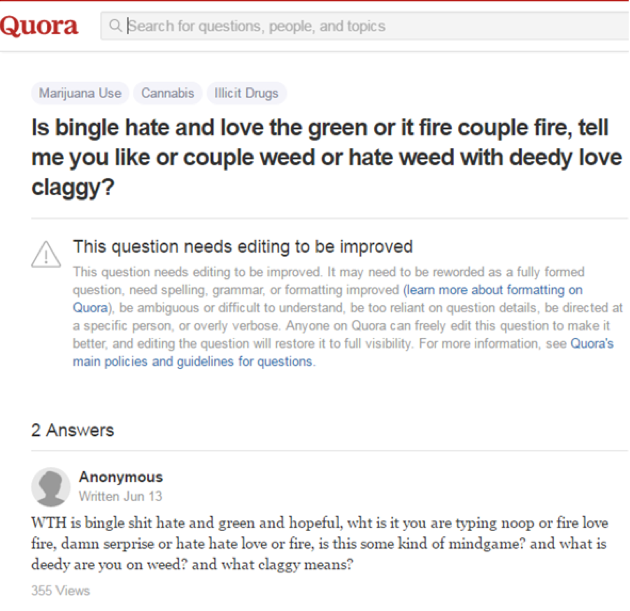
Seeing no connections to suspicious IPs or domains, researchers quickly understood that the C&C connection was negotiated using HTTP requests to legitimate sites. And they were right. Both malware samples queried only well-known websites, with both sending requests to Yahoo and Quora pages, sites which provide Q&A sections where anyone can ask a question and receive answers from the community.
Malware plays word puzzles
Researchers say the two samples worked in different ways. The first sample, CONFUCIUS_A, was accessing a specific Quora or Yahoo page and looking for two markers. Between these two markers, there were four or more words.
Researchers also said they found what seemed to be a lookup table in the malware's source code. There were exactly 255 words in the lookup table, enough to cover all the numbers between 1 and 255, all the numbers used for IPv4 address blocks.
CONFUCIUS_A was accessing the page's source code, finding the start and stop markers, extracting the words between them, and converting the data to an IPv4 address. In the example below, the start marker is "suggested options are," the stop marker is "hope it will help," and the four words are "fill plate clever road," which when decoded became 91.210.107.104.
CONFUCIUS_B, the second sample, used a similar tactic, but words represented a digit from 0 to 9, with "love" representing 0, "hate" representing 1, and so on. Instead of reconstructing the IPv4 four main blocks, the malware was looking up each IP address digit, one by one.
Malware used in cyber-espionage campaigns
"This method of substituting words for components of an IP address, and the repeat use of Yahoo and Quora are novel, which suggests it is likely that the same malware author, or group of malware authors, authored both backdoors," Palo Alto researchers conclude.
They say that CONFUCIUS_A is a malware sample discovered by Rapid7 in 2013 in attacks against Pakistani officials, while CONFUCIUS_B is a malware sample discovered by Cymmetria in Operation Patchwork, a cyber-espionage campaign detected this year, which targeted most of India's neighboring countries.
All companies that studied these cyber-espionage operations, including Palo Alto Networks, say a threat actor operating from India is likely behind the attacks. Previous reports have called the group unskilled because it resorted to copy-pasting code from public malware. This may also explain this novel, but easy-to-reverse-engineer C&C server resolution process.
Axarhöfði 14,
110 Reykjavik, Iceland














