FastPOS malware abuses Windows Mailslots to steal POS data
The group behind the FastPOS malware has updated their trojan with a new data exfiltration mechanism that abuses the Windows Mailslots mechanism to store data before exfiltration from infected systems.
 This new version of POS (Point Of Sale) malware came to light this past summer, in June, when Trend Micro security researchers discovered ads for it on underground carding forums.
This new version of POS (Point Of Sale) malware came to light this past summer, in June, when Trend Micro security researchers discovered ads for it on underground carding forums.
Analysis of the malware showed a new POS malware family that focused on speed and sacrificed stealth, an opposite approach to how most POS malware operate today. Trend Micro continued its analysis of this malware after the initial detection and discovered traces of FastPOS activity dating back to March 2015. Further, the company discovered that the FastPOS operator updates his malware every September, just in time for the holiday season. Since September just passed, Trend Micro has now published new details on the latest FastPOS version.
FastPOS now includes 32-bit and 64-bit support
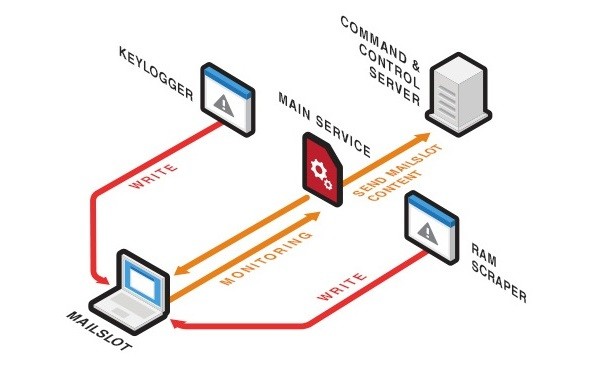
The security vendor says the malware received the ability to infect Windows computers running both 32-bit and 64-bit architectures. FastPOS, which uses two main modules (memory scrapper and keylogger), has also changed the way it works at the OS process level. The previous FastPOS version operated from one self-contained process, while in the recent version, its main and secondary modules operate from across different OS processes, making them harder to remove, but also louder for AV software. In fact, Trend Micro says that detecting the HTTP streams through which the malware steals credit card data from POS software is quite easy since the data is not encrypted.
FastPOS now abuses Windows Mailslots
But the change that stood out the most in this recent version was how FastPOS stored collected data before sending it to its C&C server. Just like in past iterations, the malware saved all data inside the computer's memory (RAM) to avoid creating local files. This was, and is, a planned feature because the malware never intends to keep the stolen information for extended amounts of time, hence the malware's name - "Fast POS."
This recent version abuses a Windows mechanism called Mailslots, which are pseudo-files (temporary files) that reside only in the computer's RAM, used to store inter-process communications (IPC). Since FastPOS modules inject themselves in processes such as explorer.exe and services.exe, they have easy access to create mailslots and store stolen data.
FastPOS targets smaller businesses
Another POS malware called LogPOS also abuses mailslots to steal data it collects from POS software. Windows mailslots fit perfectly with FastPOS' default mode of operation, which exfiltrates data as soon as the user presses Enter on a keyboard or swipes a card through a POS terminal. "Given FastPOS’s emphasis on speed, it is mainly designed to target businesses whose primary network gateways have a relatively lesser footprint," the Trend Micro team explains, revealing FastPOS' penchant for targeting small-to-medium companies.
Axarhöfði 14,
110 Reykjavik, Iceland














