FruityArmor APT group used recently patched Windows zero-day flaw
One of the four zero-day vulnerabilities Microsoft patched last week was being used by an APT group called FruityArmor to carry out targeted attacks, escape browser-based sandboxes, and execute malicious code in the wild.
 A researcher at Kaspersky Lab, was credited by Microsoft for discovering the vulnerability last Tuesday but little was known about how it was actually being exploited until today.
A researcher at Kaspersky Lab, was credited by Microsoft for discovering the vulnerability last Tuesday but little was known about how it was actually being exploited until today.
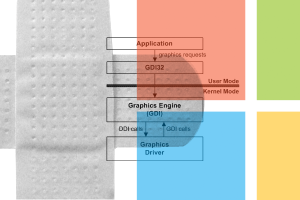
The vulnerability, CVE-2016-3393, stemmed from the way a component, Windows graphics device interface (GDI), handled objects in memory. GDI is an application programming interface in Windows that helps apps that use graphics and formatted text on the video display and printer. Microsoft said in bulletin MS16-120, which it marked critical, that an attacker could exploit the vulnerability multiple ways, either by tricking a user into opening a rigged document file, tricking a user into visiting a rigged site and then convincing them to click on a link, or tricking a user into opening an attachment sent via email.
FruityArmor was using a browser exploit to execute malicious code and pairing it with CVE-2016-3393 to escape browser sandboxes and elevate privileges. The vulnerability could be triggered by a module that when unpacked, loads a specialized TTF font rigged with the exploit. FruityArmor zigs when other groups zag in the sense that it uses a platform built completely around PowerShell, the Microsoft-based command-line shell and scripting language. Not only is the group’s primary malware implant written in PowerShell, so are the commands sent by operators.
Once in, a secondary payload is executed with even higher-level privileges to execute PowerShell and connect to the attackers’ command and control server. From there the group can deliver instructions and download additional modules. The module that unpacks the malicious TTF font was seen running directly in memory, and then loading the exploit’s code from memory.
Microsoft said that it fixed the vulnerability by addressing how Windows GDI handles objects in memory. A handful of malware strains have been spotted leveraging PowerShell over the past few months. A Brazilian banking Trojan was observed in August using PowerShell scripts to make proxy configuration changes in Internet Explorer to redirect connections to phishing pages. Last month, researchers with FireEye saw Hancitor, a malicious downloader, using PowerShell commands to obtain payloads and evade detection.
Kaspersky Lab has been credited with discovering two Adobe Flash zero days (CVE-2016-1010 and CVE-2016-4171) and another Windows elevation of privilege vulnerability, CVE-2016-0165, earlier this year. The company said it refrained from posting too much information about the APT out of risk other threat actors would adopt the tactics for their attacks. Expert said that the longer unpatched vulnerabilities tied to zero days linger, the more valuable they become to attackers.
“Even though there is a growing tendency for attackers to use off-the-shelf malware, unpatched zero-days remain the top prize, treasured by targeted threat actors,” Ivanov said Thursday. “The demand for such vulnerabilities is unlikely to diminish any time soon, which is why we need security researchers to continue hunting for them, protection technologies able to detect them, and software developers responding rapidly with a fix. We all have a shared responsibility to protect customers.”
Axarhöfði 14,
110 Reykjavik, Iceland














