Wikileaks unveils CIA implants that steal SSH credentials from Windows & Linux PCs
WikiLeaks has today published the 15th batch of its ongoing Vault 7 leak, this time detailing two alleged CIA implants that allowed the agency to intercept and exfiltrate SSH (Secure Shell) credentials from targeted Windows and Linux operating systems using different attack vectors.
 Secure Shell or SSH is a cryptographic network protocol used for remote login to machines and servers securely over an unsecured network.
Secure Shell or SSH is a cryptographic network protocol used for remote login to machines and servers securely over an unsecured network.
Dubbed BothanSpy — implant for Microsoft Windows Xshell client, and Gyrfalcon — targets the OpenSSH client on various distributions of Linux OS, including CentOS, Debian, RHEL (Red Hat), openSUSE and Ubuntu. Both implants steal user credentials for all active SSH sessions and then sends them to a CIA-controlled server. BothanSpy is installed as a Shellterm 3.x extension on the target machine and only works if Xshell is running on it with active sessions. Xshell is a powerful terminal emulator that supports SSH, SFTP, TELNET, RLOGIN and SERIAL for delivering industry leading features including dynamic port forwarding, custom key mapping, user defined buttons, and VB scripting.
WikiLeaks has today published the 15th batch of its ongoing Vault 7 leak, this time detailing two alleged CIA implants that allowed the agency to intercept and exfiltrate SSH (Secure Shell) credentials from targeted Windows and Linux operating systems using different attack vectors. Secure Shell or SSH is a cryptographic network protocol used for remote login to machines and servers securely over an unsecured network. Dubbed BothanSpy — implant for Microsoft Windows Xshell client, and Gyrfalcon — targets the OpenSSH client on various distributions of Linux OS, including CentOS, Debian, RHEL (Red Hat), openSUSE and Ubuntu. Both implants steal user credentials for all active SSH sessions and then sends them to a CIA-controlled server.
BothanSpy — Implant for Windows OS BothanSpy is installed as a Shellterm 3.x extension on the target machine and only works if Xshell is running on it with active sessions. Xshell is a powerful terminal emulator that supports SSH, SFTP, TELNET, RLOGIN and SERIAL for delivering industry leading features including dynamic port forwarding, custom key mapping, user defined buttons, and VB scripting. "In order to use BothanSpy against targets running a x64 version of Windows, the loader being used must support Wow64 injection," the leaked CIA user manual reads. "Xshell only comes as a x86 binary, and thus BothanSpy is only compiled as x86. Shellterm 3.0+ supports Wow64 injection, and Shellterm is highly recommended." Gyrfalcon — Implant for Linux OS
Gyrfalcon targets Linux systems (32 or 64-bit kernel) using a CIA-developed JQC/KitV rootkit for persistent access. Gyrfalcon is also capable of collecting full or partial OpenSSH session traffic, and stores stolen information in an encrypted file for later exfiltration.
The user manual for Gyrfalcon v2.0 says that the implant is consist of "two compiled binaries that should be uploaded to the target platform along with the encrypted configuration file."
Previous Vault 7 CIA Leaks
Last week, WikiLeaks dumped a classified CIA project that allowed the spying agency to hack and remotely spy on PCs running the Linux operating systems. Dubbed OutlawCountry, the project lets the CIA hackers redirect all outbound network traffic on the targeted machine to CIA controlled computer systems for exfiltrate and infiltrate data.
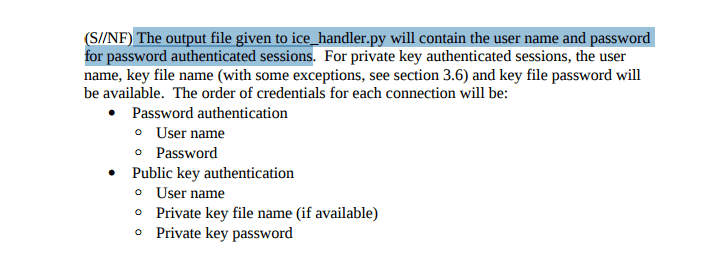
Gyrfalcon targets Linux systems (32 or 64-bit kernel) using a CIA-developed JQC/KitV rootkit for persistent access. Gyrfalcon is also capable of collecting full or partial OpenSSH session traffic, and stores stolen information in an encrypted file for later exfiltration. "The tool runs in an automated fashion. It is configured in advance, executed on the remote host and left running," the user manual of Gyrfalcon v1.0 reads. "Sometime later, the operator returns and commands gyrfalcon to flush all of its collection to disk. The operator retrieves the collection file, decrypts it, and analyzes the collected data."
The user manual for Gyrfalcon v2.0 says that the implant is consist of "two compiled binaries that should be uploaded to the target platform along with the encrypted configuration file." "Gyrfalcon does not provide any communication services between the local operator computer and target platform. The operator must use a third-party application to upload these three files to the target platform."
Previous Vault 7 CIA Leaks Last week, WikiLeaks dumped a classified CIA project that allowed the spying agency to hack and remotely spy on PCs running the Linux operating systems. Dubbed OutlawCountry, the project lets the CIA hackers redirect all outbound network traffic on the targeted machine to CIA controlled computer systems for exfiltrate and infiltrate data.
Download SafeUM — communicate privately, without advertising and spam.
Axarhöfði 14,
110 Reykjavik, Iceland

















