TrueCrypt: an unexplained disappearance
Something very weird is going on with the popular free whole-disk encryption suite TrueCrypt. The story is still developing, but it does look like the suite ceases to exist right now.
 The only explanation its creators have provided so far is that using TrueCrypt “is not secure as it may contain unfixed security issues”.
The only explanation its creators have provided so far is that using TrueCrypt “is not secure as it may contain unfixed security issues”.
What kind of issues? – This is something people behind TrueCrypt have not disclosed so far. There are some speculations about the possibility of a backdoor in the software code, but it’s guesswork at best.
There was also speculation of a possible deface: TrueCrypt’s official site started redirecting people to the suite’s Sourceforge page all of sudden. Now, however, there is a sort of a consensus that it wasn’t a deface: along with redirect, the software itself is altered too, and now it is showing the very same warning as the Sourceforge site does.
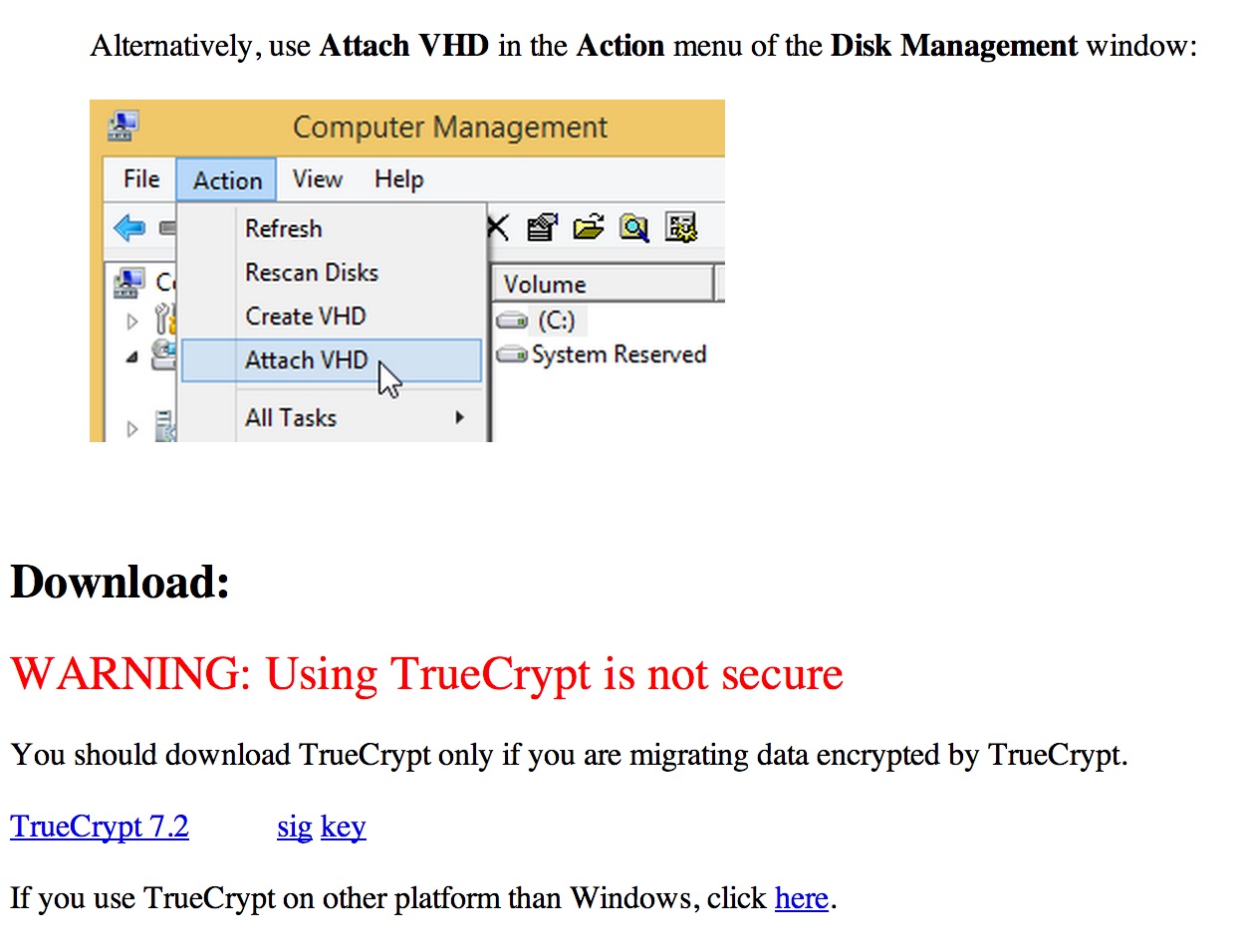
Users of TrueCrypt are recommended to migrate from TrueCrypt to Microsoft’s BitLocker: TrueCrypt’s developers offer a step-by-step instructions on how to do this. TrueCrypt is (well, was) a cross-platform, freeware, “source-available” encryption application that could create a virtual encrypted disk within a file or encrypt a partition or (under Microsoft Windows except Windows 8 with GPT) the entire storage device (pre-boot authentication).
It’s been around for almost 10 years, and all this time its developers stayed away from the limelight, even keeping their names in secret. The suite was highly praised for its stability, a formidable feature set, support of parallelized encryption for multi-core systems, and, specifically, “plausible deniability” function which allowed a single “hidden volume” to be created within another volume.
The developers had acknowledged that TrueCrypt is vulnerable to a few known attacks, for instance it may fall victim to a “Stoned” bootkit, so additional security measures should be applied. Other than that, TrueCrypt mostly received high acclaim, except for the vagueness of language in its license, which is unique, and differs from widely used open source and free software licenses since it contains distribution and copyright-liability restrictions.
By May, 2014 the software had been downloaded 28 million times. And now developers seem to have pulled the plug abruptly, and it does look like a withdrawal – a retreat from the uneasy world of encryption, which is made much more uneasy than before by E. Snowden’s revelations last year.
Actually, it was those revelations that, in part, led to a demand for an independent security audit to find out whether the suite might be tampered with at a certain point. A John Hopkins University’s cryptographer and research professor Matthew Green, a long-time “skeptic” of TrueCrypt launched a dual crowdfunding campaign to get such audit funded.
The community has shown a strong interest: Green eventually managed to collect as much as $70,000 (way above the campaign’s set goal), and the first round of audit had been successfully completed earlier this year, yielding no adverse discoveries. The second phase hadn’t even started yet, and now it looks there may not be one. Due to the “clouded” legal status of the TrueCrypt source code it is unclear if anyone would be able to pick up the development.
So, let’s put it straight: For now, nobody except for the TrueCrypt’s developers themselves, of course, actually know what is going on. No information on the nature of the security issue and the possibility to fix it.
The software was popular: 28 million downloads is a large amount itself, and even if only one third of those who downloaded the suite have actually been using it, that’s the population of a large city. Migration to BitLocker is actually available “out of the box” to some users, since it is only shipped with the top-tier versions of Windows (Vista, 7 and 8).
All these people now question whether their data has been secure at all since the day they have started using TrueCrypt. A lack of explanation doesn’t make them feel any easier.
While it is a common wisdom that noone reads EULAs, users expect they can trust software vendors, no matter if the sofware is commercial proprietary or open-source and/or free to use. The last thing people would expect from a software developer is a sudden vanishing into the mist without an explanation. This is not the way things should work. Especially in the information security area.
Axarhöfði 14,
110 Reykjavik, Iceland














