An Iranian hacker is in every server
Physically, Adelson and Sands are well protected. He appears in public with a phalanx of armed bodyguards, said to be former agents of the U.S. Secret Service and Mossad, Israel’s intelligence agency.
 Sands paid almost $3.3 million to protect Adelson and his family last year, according to a company filing. That’s on top of what Sands spends on vaults, security cameras, biometric screening devices, and one of the largest private police forces of any U.S. company, all to safeguard the millions of dollars of cash and chips that flow through its operations every day.
Sands paid almost $3.3 million to protect Adelson and his family last year, according to a company filing. That’s on top of what Sands spends on vaults, security cameras, biometric screening devices, and one of the largest private police forces of any U.S. company, all to safeguard the millions of dollars of cash and chips that flow through its operations every day.
But the company has been slow to adapt to digital threats. Two years ago it had a cybersecurity staff of five people protecting 25,000 computers, according to a former executive. The board authorized a major upgrade of tools and personnel in 2013, but the project was slated to be rolled out over 18 months, and it was in its infancy as Adelson mused about nuclear strikes at Yeshiva.
Unbeknownst to Sands, one month after Khamenei’s fiery speech, hackers began to poke around the perimeter of its computer networks, looking for weaknesses. Only later, after the attack, were investigators able to sift through computer logs and reconstruct their movements. These details appear in internal documents describing “Yellowstone 1,” the company’s code name for the incident, and have been corroborated in interviews with a half-dozen people familiar with the breach and its aftermath. Ron Reese, a spokesman for Sands, declined to answer specific questions about the attack or to make Adelson available.
By Jan. 8, 2014, the hackers were focused on Sands Bethlehem, a 3,000-slot-machine casino and resort in Bethlehem, Pa., which has its own website and computer network. It’s a minor outpost in the company’s empire, but going after the weak link in the security chain is a well-worn hacker trick. That day, the hackers launched a first, hourlong attack to try to break into the Sands Bethlehem virtual private network, or VPN, which gives employees access to their files from home or on the road.
The hackers used software that cracks password logins by systematically trying as many as several thousand letter combinations per minute; the software keeps going until it either guesses right or runs out of permutations. It’s a brute-force method, sort of like the safecracking tools in movies that spin through every possible combination to find the correct set of numbers.

The hackers redoubled their efforts on Jan. 21 and 26, again throwing hourslong attacks at the Bethlehem Sands network. Later, investigators would detect the work of at least two different hackers or teams trying different ways to get in. At the time, IT managers in Bethlehem, alarmed at the sudden surge in failed login attempts, began a conference call with Sands security managers in Las Vegas. But brute-force attempts are common—almost half of all companies experience them, according to Alert Logic, a Houston security firm—and the casino staff wasn’t overly concerned. They put another layer of security on the accounts that were being attacked, so that entering the network would require more than just a password.
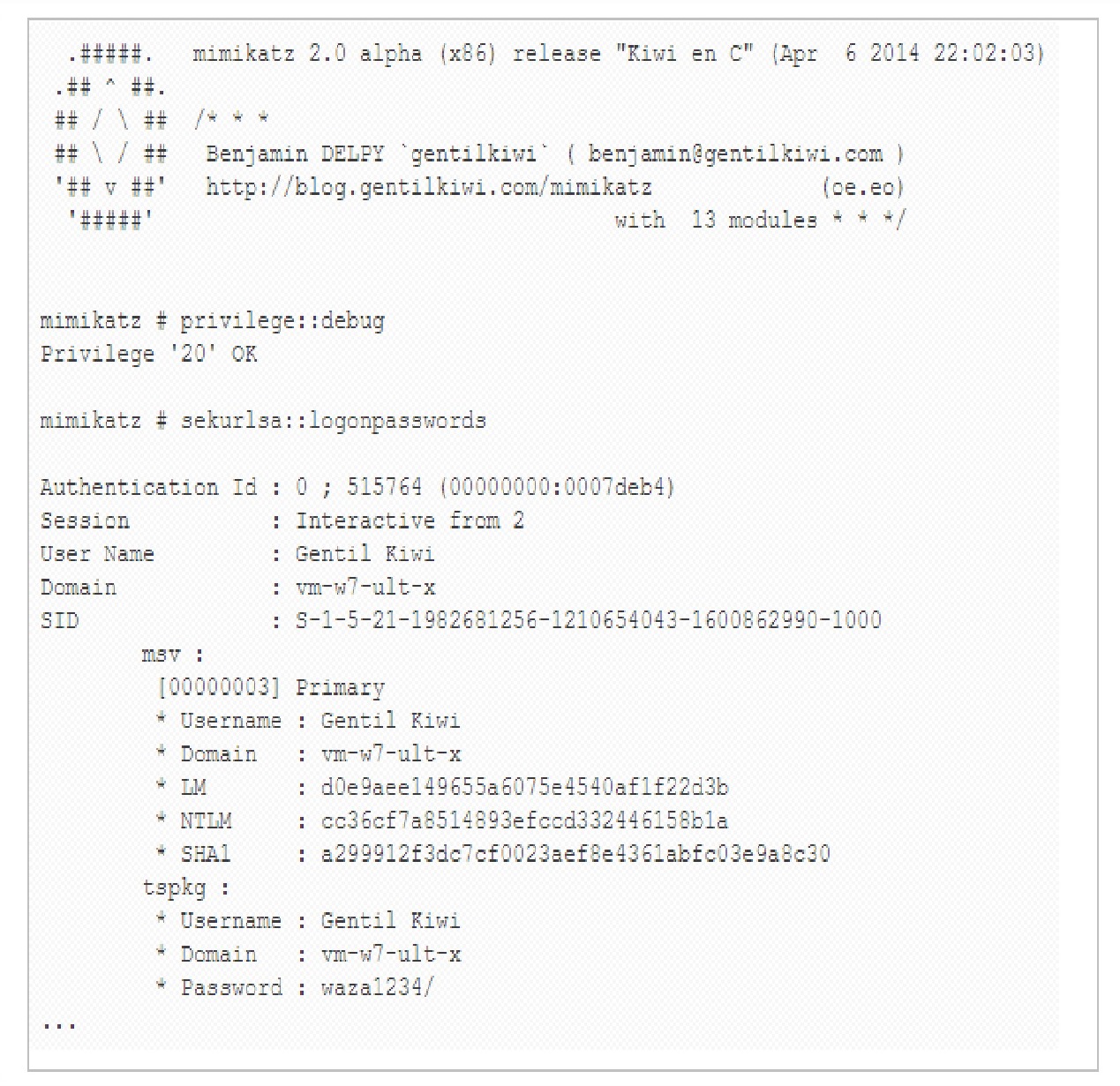
It was of little use: Five days later, on Feb. 1, the hackers found a weakness in a Web development server used by Sands Bethlehem to review and test Web pages before they went live. Once inside, the pace of the attack quickly escalated. Hackers used a tool called Mimikatz to reveal passwords used previously to log in to a computer or server. Collecting passwords as they went, the hackers gained access to almost every Sands file in Bethlehem, according to three people familiar with the incident. But the Bethlehem computer system was a box—and what they were really after was the key that would let them out.
Sometime before Feb. 9, they found it: the login credentials of a senior computer systems engineer who normally worked at company headquarters but whose password had been used in Bethlehem during a recent trip. Those credentials got the hackers into the gaming company’s servers in Las Vegas. As they rifled through the master network, the attackers readied a malware bomb.
Typing from a Sony (SNE) VAIO computer, they compiled a small piece of code, only about 150 lines long, in the Visual Basic programming language. The program proved potent. Not only does it wipe the data stored on computers and servers, but it also automatically reboots them, a clever trick that exposes data that’s untouchable while a machine is still running. Even worse, the script writes over the erased hard drives with a random pattern of ones and zeros, making data so difficult to recover that it is more cost-effective to buy new machines and toss the hacked ones in the trash.
Investigators from Dell SecureWorks working for Sands have concluded that the February attack was likely the work of “hacktivists” based in Iran, according to documents obtained by Bloomberg Businessweek. The security team couldn’t determine if Iran’s government played a role, but it’s unlikely that any hackers inside the country could pull off an attack of that scope without its knowledge, given the close scrutiny of Internet use within its borders. “This isn’t the kind of business you can get into in Iran without the government knowing,” says James Lewis, a senior fellow at the Center for Strategic and International Studies in Washington. Hamid Babaei, a spokesman for Iran’s Permanent Mission to the United Nations, didn’t return several phone calls and e-mails.
Axarhöfði 14,
110 Reykjavik, Iceland














