China reportedly attacks Microsoft users
China mounted a cyberattack on users of Microsoft's Outlook email service on Saturday, with the apparent goal of spying on their communications, according to a Chinese Internet monitoring group.
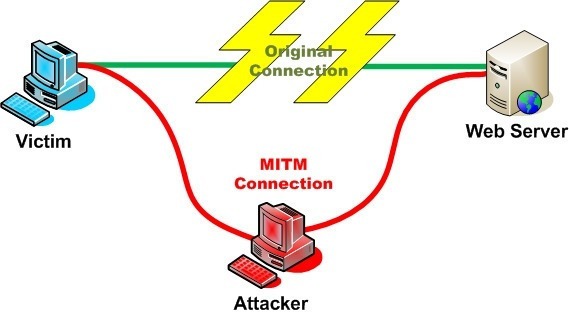
 On January 17, people within China using email clients to connect to their Outlook, Hotmail or Live accounts were subjected to a "man-in-the-middle" (MITM) attack in which the attacker tried to hijack what's normally a secure, encrypted connection, according to a report by GreatFire.
On January 17, people within China using email clients to connect to their Outlook, Hotmail or Live accounts were subjected to a "man-in-the-middle" (MITM) attack in which the attacker tried to hijack what's normally a secure, encrypted connection, according to a report by GreatFire.
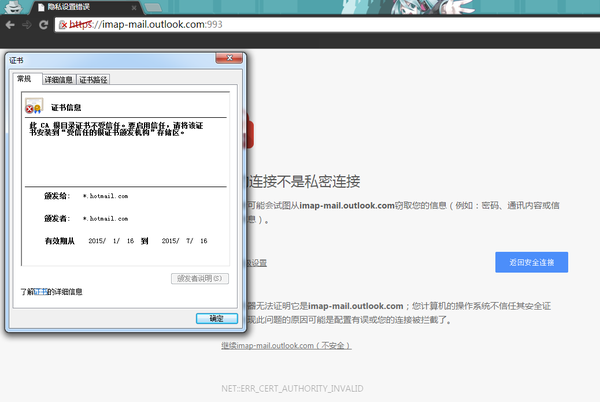
The activist group believes this is the latest attempt by China to intercept and spy on communications that it can't easily monitor. Some users reported the attack on Friday when they saw error messages using email clients connecting to Outlook's servers via IMAP and SMTP, protocols used to send and receive emails. (Connections to outlook.com and login.live.com, on the other hand, were not affected, according to a test performed by GreatFire.)
"We once again suspect that Lu Wei and the Cyberspace Administration of China have orchestrated this attack or have willingly allowed the attack to happen," GreatFire wrote in its detailed analysis of the attack. "If our accusation is correct, this new attack signals that the Chinese authorities are intent on further cracking down on communication methods that they cannot readily monitor."
GreatFire reported that the attack used "self-signed" certificates to impersonate Outlook's server. Internet certificates are used to verify the identity of a website or, in this case, a server, and to ensure that the connection is secure and private. Digital certificates are normally issued by official and trusted certificate authorities. But they can also be issued by a site or service certifying its own identity. These are called self-signed certificates, which usually prompt browsers and email clients to display a warning, since a self-signed certificate can be a sign of an MITM attack.
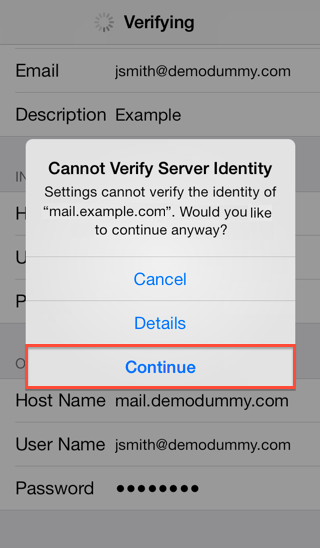
Microsoft confirmed the attack in a statement, but declined to answer any questions about it. "We are aware of a small number of customers impacted by malicious routing to a server impersonating Outlook.com," a Microsoft spokesperson told in an email. "If a customer sees a certificate warning, they should contact their Internet service provider for assistance."
The attack lasted only a day, but was still "especially devious" because users are more likely to ignore warning messages using email clients (such as the one below) than they are when using browsers like Chrome or Firefox, GreatFire said.
This new attack comes roughly three months after the Chinese government allegedly attacked Microsoft users trying to log in via Hotmail.com and Live.com, as well as iCloud users, trying to steal their credentials. A similar MITM attack on Yahoo was also reported in late September, during the protests in Hong Kong.
"This continues a pattern of organized MITM attacks on major communications platforms," Michael Carbone, a technologist at the human rights organization Access, told. Carbone stressed that users in China should not ignore any warnings, because these attacks could expose their personal information and communications.
"Users should take seriously any warnings raised by their email clients or web browsers, and seek to use access tools like VPNs, Tor, Lantern, Psiphon or others if they continue to run into these warnings as a way to better secure their communications," he said in an email. It's unclear if the Chinese government was really behind the attack, but experts believe that MITM attacks like this one can only be performed by telecom providers or a government.

The motive behind the attack is also unclear, but GreatFire speculated that China might be testing its MITM capabilities, and gauging whether users fall for this kind of attack despite the warnings to figure out how effective these attacks can be. It's also worth noting that Chinese browsers such as Baidu's or Qihoo's only display smaller warnings in these cases, according to Percy Alpha, one of the activists at GreatFire, making them less safe than Chrome or Firefox, which display full page warnings.
GreatFire is also asking tech companies to revoke trust on China's certificate authority, the CNNIC (China Internet Network Information Center), in case the Chinese government decides to use this organization to issue legitimate-looking certificates that wouldn't prompt browsers or clients to display warnings.
This would allow China to "better impersonate" Internet services and monitor them, according to Carbone. "It is something of a 'nuclear option,'" Carbone added, as using this strategy would probably force major web browsers and operating systems to blacklist the CNNIC and other Chinese certificate authorities.
Axarhöfði 14,
110 Reykjavik, Iceland














