HTC phone stored unencrypted fingerprints
Researchers from FireEye have found that data that could be used to clone a user’s fingerprint was stored as an unencrypted “world readable” image file on HTC smartphones.
 Four security researchers discovered that the image file, which is clear replica of a user’s fingerprint, could be stolen by rogue apps or hackers.
Four security researchers discovered that the image file, which is clear replica of a user’s fingerprint, could be stolen by rogue apps or hackers.
“While some vendors claimed that they store user’s fingerprints encrypted in a system partition, they put users’ fingerprints in plaintext and in a world readable place by mistake,” the authors wrote. “On the HTC One Max X the fingerprint is saved as /data/dbgraw.bmp with a 0666 permission setting (world readable). Any unprivileged processes or apps can steal user’s fingerprints by reading this file.” The researchers presented their findings at the Black Hat security conference in Las Vegas.
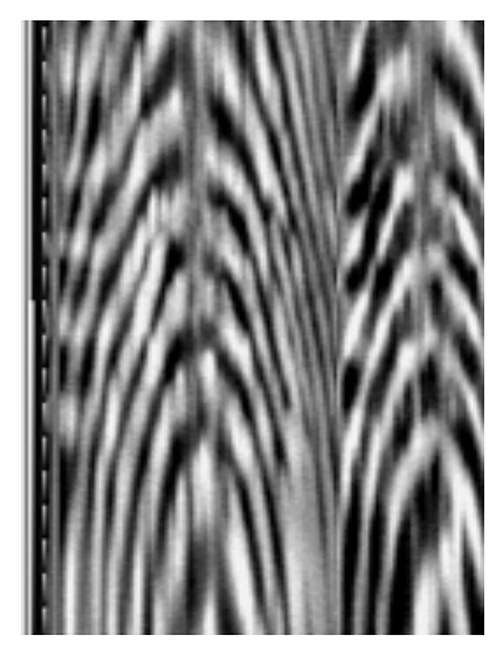
They were able to pull fingerprint images from the smartphone and see sufficient detail to tell that, for instance, the fingerprint image was a bit blurry in the bottom section and that the fingerprint sensor had reproducible characteristics. “To make the situation even worse, each time the fingerprint sensor is used ... [it] will refresh that fingerprint bitmap to reflect the latest wiped finger. So the attacker can sit in the background and collect the fingerprint image of every swipe of the victim,” wrote the authors.
HTC isn’t the only smartphone manufacturer doing a very poor job of securing users’ fingerprints. Most store them within secure parts of the smartphone’s processor and associated chips designed to keep user credentials safe such as the “TrustZone or Secure Enclave”, but even those have “known vulnerabilities for attackers to leverage to peek into the secret world”, according to the authors of the report.
An HTC spokesperson said on Tuesday: “HTC is aware of the FireEye report on fingerprint scanner security. We have already addressed the issue for the HTC One max in all regions, and it doesn’t affect any other HTC devices. As always, HTC takes security issues very seriously and makes it a top priority.”
Failing to lock down fingerprint sensors
The authors also found that the fingerprint sensors themselves are vulnerable to attack as most manufacturers, including Samsung and HTC, do not use the built-in security features of the ARM-based chips that most smartphones use.
“Most vendors fail to lock down the [fingerprint] sensor... without the proper lock down, an attacker from normal world can directly read the fingerprint sensor. Note that attackers can do this stealthily in the background and they can keep reading the fingerprints on every touch of the victim’s fingers,” wrote the authors.
The poor security allows programs running on the smartphone to steal data from the sensor without having to hack into the secure layer chips, and opens the door to the remote stealing of data, should the user be unwittingly targeted by smartphone malware. Smartphones have become an increasingly important target for hackers, containing a large amount of personal data, while security vulnerabilities such as the recent Stagefright bug have shown that users can do little to stop remote hacking.
While the theft of passwords is an immediate danger, stolen biometric data such as fingerprints represents a bigger risk as they are increasingly used for proof of identity for citizen services such as boarder control. Unlike a password, a fingerprint can’t be changed.
Google recently introduced support for fingerprint scanners into Android, while payment services such as Samsung Pay, Apple Pay and Android Pay, are secured by the biometric devices, meaning their proliferation is likely. While biometric data such as fingerprints offer an alternative to passwords, they must be secured to prevent identity fraud, the authors urge.
Axarhöfði 14,
110 Reykjavik, Iceland














