How hackers can hack your chip-and-pin credit cards
October 1, 2015, was the end of the deadline for U.S. citizens to switch to Chip-enabled Credit Cards for making the transactions through swipe cards safer.
 Now, a group of French forensics researchers have inspected a real-world case in which criminals played smart in such a way that they did a seamless chip-switching trick with a slip of plastic that it was identical to a normal credit card.
Now, a group of French forensics researchers have inspected a real-world case in which criminals played smart in such a way that they did a seamless chip-switching trick with a slip of plastic that it was identical to a normal credit card.
The researchers from the École Normale Supérieure University and the Science and Technology Institute CEA did a combined study of the subject, publishing a research paper [PDF] that gives details of a unique credit card fraud analyzed by them. What's the Case? Back in 2011 and 2012, police arrested five French citizens for stealing about 600,000 Euros (~ $680,000) as a result of the card fraud scheme, in spite of the Chip-and-PIN cards protections.
How did the Chip-and-Pin Card Fraud Scheme Work?
On investigating the case, the researchers discovered that the now-convicted criminals actually modified stolen credit cards to insert a second chip inside them, which is: Capable of spoofing the PIN verification the cards sent to a Point of Sale (POS) terminal. A strange thing here is, the researchers used microscopic analysis and X-ray scans to look at where the chip-and-pin cards had been tampered with.
Performing Man-in-the-Middle Attack
The fraudsters took advantage of a long-known vulnerability in Chip-and-PIN systems to perform a "man-in-the-middle" (MITM) attack. The flaw is a known protocol vulnerability in Chip and Pin cards that, in 2006, allowed criminals to use a genuine card to make payments without knowing the card's PIN. The flaw actually takes advantage of how cards and card readers communicate with each other.
The second hobbyist chip (dubbed a FUNcard) - that the fraudsters inserted onto the card’s original chip - accepts any PIN entry. A typical EMV transaction involves three steps:
- Card authentication
- Cardholder verification
- Transaction authorization
When a buyer inserts the altered card, the original chip allows to respond with the card authentication as normal. But, during cardholder authorization, the POS system would ask to enter a PIN. In this case, the fraudster could respond with any PIN, and the fraudulent chip comes into play and will result in a "YES" signal regardless of whatever random PIN the thief has entered. "The attacker intercepts the PIN query and replies that it is correct, whatever the code is," said ENS security researcher Rémi Géraud. "That is the core of the attack." The good part is: the vulnerabilities compromised by the fraudsters has been fixed—at least in Europe, the researchers declined to fully detail the new security measures.
What Does the Forensic Analysis say?
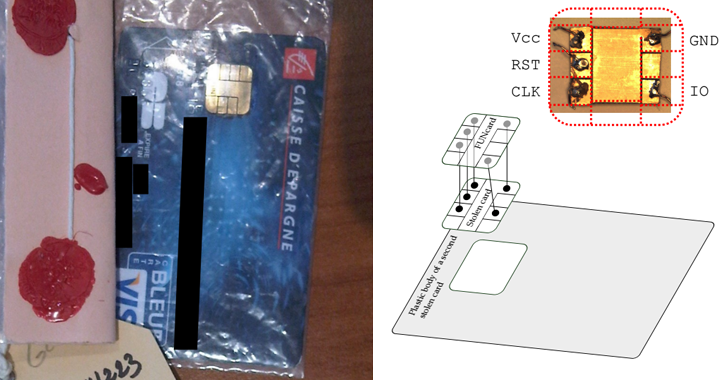
The cyber criminals had miniaturized the backpack setup into a tiny FUN card chip, a cheap and programmable device used by DIY hobbyists. The size of the chip was not larger than the regular security chip used in credit cards. This may increase the thickness of the chip from 0.4mm to 0.7mm, but perfectly feasible when inserted into a PoS system.
The now-convicted criminals stole credit cards and then removed the chip from them, solder it to the FUN card chip, and fixed both chips back-to-back onto the plastic body of another stolen card. The result was a powerful device that the fraudsters then used to run victims out of their money. "It was small enough they could fit the whole attack inside the card and use it to buy things in stores…It would be a bit harder to put it into the reader, but not so hard that you’d suspect anything," Géraud said. "It was quite clever, quite hard to detect, and for some time they managed to evade detection."
Role of X-Rays
The researchers could not perform a full tear-down or run any tests that would alter the data on the chip-and-pin card, so they used X-ray scans. The researchers examined one of the devices (forged credit cards) with non-invasive X-ray scans, prior to which they discovered a hidden FUNcard logo on a chip inside. They then reverse engineered the forged card's computational activity by analyzing the way the chips distributed electricity when inserted into a card reader; the timing of the card's power use revealed the occurrence of a man-in-the-middle attack. To read the full research paper, download this PDF.
Axarhöfði 14,
110 Reykjavik, Iceland














