Chrome extension caught stealing Bitcoin from users
Slovenia-based Bitcoin exchange portal Bitstamp is warning users of a Google Chrome extension that steals their Bitcoin when making a transfer.
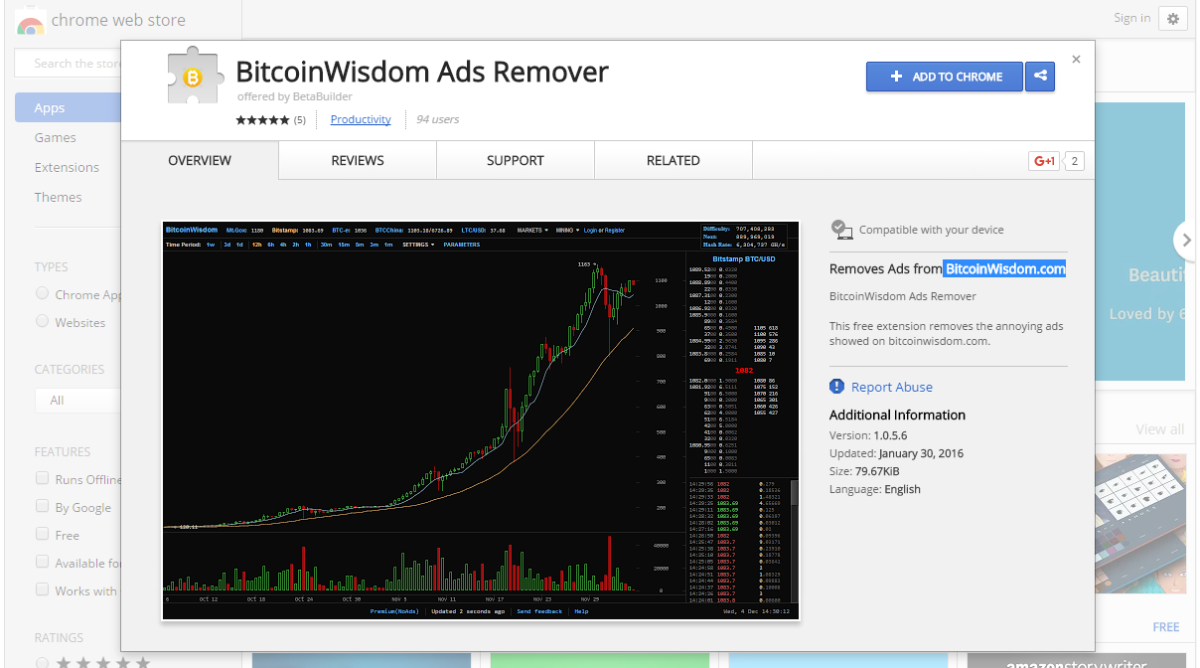
 The extension's name is BitcoinWisdom Ads Remover and is a Chrome extension that removes ads from the BitcoinWisdom.com, a website for consulting all kinds of Bitcoin-related statistics, all presented in easy-to-understand charts.
The extension's name is BitcoinWisdom Ads Remover and is a Chrome extension that removes ads from the BitcoinWisdom.com, a website for consulting all kinds of Bitcoin-related statistics, all presented in easy-to-understand charts.
According to Bitstamp, a website that lets users exchange Bitcoin for US dollars, this extension contains malicious code that is redirecting payments to its own Bitcoin address, instead of the one intended by the user making the transaction. Bitcoin Web app developer Devon Weller confirmed Bitstamp's findings. The Nashville, Tennessee-based developer said that the extension was secretly replacing QR codes with its own.
"Extension was replacing QR codes payment destinations"
For those that haven't used Bitcoin until now, QR codes are one of the methods through which you can make payments or transfer Bitcoin from one account to the other. Because Bitcoin account (also called wallet) addresses are extremely long strings of random characters, some Bitcoin exchange portals provide the option of taking the whole string and rendering as a QR code. Users can then scan the QR code with their phone (running a Bitcoin payments app) and approve the payment/transfer.
The BitcoinWisdom Ads Remover Chrome extension was abusing its position to manipulate a Web page's source code and replace the QR code of a payment's destination with one of its own.
Since Bitcoin doesn't use vanity addresses (like name.surname), technologies like QR codes are still needed to simplify the process of making a transaction, and most people use them because typing a 30- or 40-character-long string can sometimes lead to typing errors, and also a lot of wasted time.
At the time of this article, the Chrome extension was still available through Google's Chrome Web Store. In July 2015, many users reported having similar issues with the same extension. Experts have been in contact with Mr. Weller who, after continuing his investigation in the extension's source code, discovered that it only targets users of the following Bitcoin services: Bitstamp, BTC-E, and Hashnest.
Axarhöfði 14,
110 Reykjavik, Iceland














