Mirai Trojan is the next big threat to IoT devices and Linux servers
A new trojan named Mirai has surfaced, and it's targeting Linux servers and IoT devices, mainly DVRs, running Linux-based firmware, for the purpose of enslaving these systems as part of a large botnet used to launch DDoS attacks.
 According to security researcher MalwareMustDie! (MMD), Mirai is an evolution of an older trojan, also used for DDoS attacks, known under many names, such as Gafgyt, Lizkebab, BASHLITE, Bash0day, Bashdoor, and Torlus.
According to security researcher MalwareMustDie! (MMD), Mirai is an evolution of an older trojan, also used for DDoS attacks, known under many names, such as Gafgyt, Lizkebab, BASHLITE, Bash0day, Bashdoor, and Torlus.
Mirai's predecessor is serious. According to a Level 3 report, Gafgyt has infected over one million IoT devices during the past months, and there's one crook running a Gafgyt-powered botnet of over 120,000 bots. Mirai's mode of operation is largely the same as Gafgyt, targeting IoT devices running Busybox, a slimmed-down version of select GNU tools and libraries, usually deployed on small embedded hardware. The trojan also targets only a specific set of platforms, such as ARM, ARM7, MIPS, PPC, SH4, SPARC, and x86, on which IoT devices are usually built.
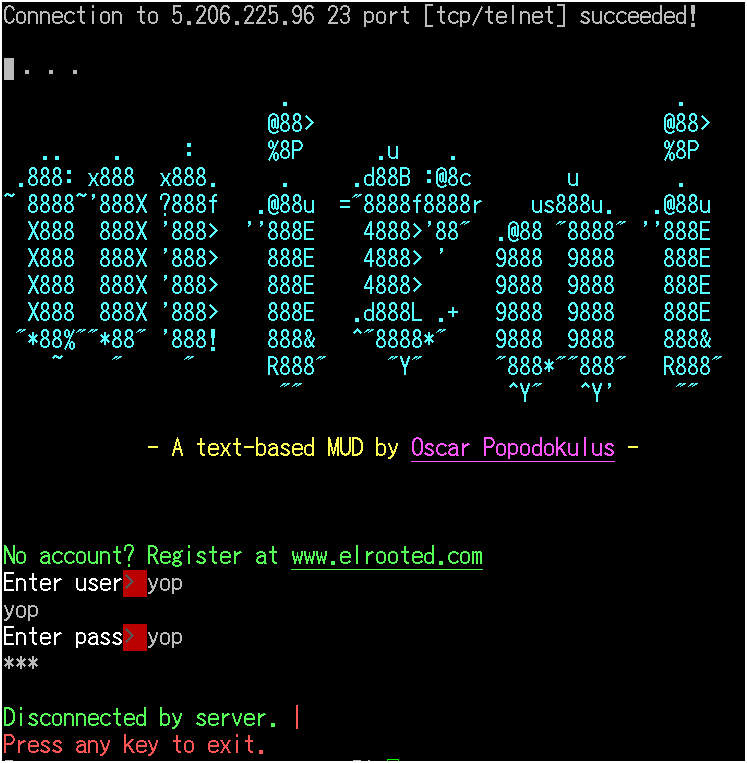
Mirai infects devices via brute-force attacks on the Telnet port, using a list of default admin credentials, trying to exploit cases where device owners have forgotten to change the built-in password. Once it infects a device, it reports to the C&C server and awaits commands. Mirai comes with support for launching DDoS attacks, but it also brute-force attacks, which it uses to spread itself to other IoT devices.
"Mirai mainly targets DVRs and IP cameras"
Based on the "/dvrHelper" string found in Mirai's source code, MMD suspects the trojan was specifically built to target DVRs and IP cameras. The researcher also says that Mirai is either coded by the same Gafgyt crew, or its creators have copy-pasted a large chunk of its codebase into Mirai. "ELF Linux/Mirai is the next generation of what they called it as 'GayFgt/LizKebab/Torlus' or what we call it as 'Bash0day, Bashdoor, or Bashlite' in the past," MMD writes. "Which is desigend [sic] to be more sophisticated in aiming Linux boxes in internet for the botnet purpose (obviously for the DDoS attack cannons)."
For server administrators and sysadmins, some mitigations are available in order to filter Mirai brute-force traffic and avoid getting your servers and IoT devices compromised. In the past few months, other researchers have spotted DDoS botnets made up of DVRs and CCTV systems, some of them as big as 25,000 bots. Other Linux trojans that have targeted IoT devices and Linux servers to enslave in DDoS botnets include PNScan and Remaiten.
Axarhöfði 14,
110 Reykjavik, Iceland














