MarsJoke: the cryptor and the cure
Every day, new versions and variations of ransomware pop up. Malware creators are still sure that ransomware is their ticket to easy street, despite the fact that law enforcement agencies are paying more and more attention to the problem.
 In fact, so many different versions are out there, ransomware creators have started to repeat themselves or copy the work of others. For example, the recently discovered Trojan-cryptor Polyglot, aka MarsJoke, is a knockoff of the infamous (and rather nasty) CTB-Locker ransomware.
In fact, so many different versions are out there, ransomware creators have started to repeat themselves or copy the work of others. For example, the recently discovered Trojan-cryptor Polyglot, aka MarsJoke, is a knockoff of the infamous (and rather nasty) CTB-Locker ransomware.
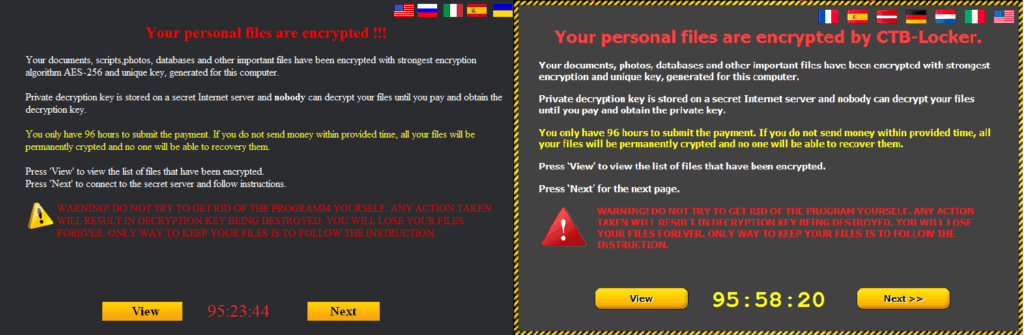
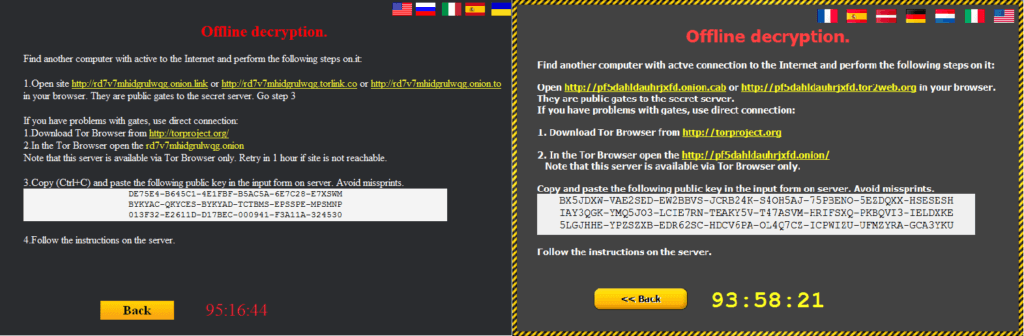
You can see traces of CTB-Locker all over Polyglot. Its interface is absurdly reminiscent of the older Trojan. It changes victims’ desktop wallpaper the same way and, just like CTB-Locker, it lets victims decrypt five files free as proof that they can be decrypted. Polyglot’s instructions to victims are also identical to those of CTB-Locker — the text looks to have been copied and pasted. Even the “Request failed” window that pops up in case there is no Internet connection looks the same.
 The encryption algorithms Polyglot uses are also the same — and they are rather strong.
The encryption algorithms Polyglot uses are also the same — and they are rather strong.
Polyglot is delivered mostly through spam — the letters contain malicious links allegedly leading to some important documents. Of course, there are no documents — just an archive with a malicious executable file. Once installed, Polyglot connects to its command-and-control sever to send information about the infected PC and handle the ransom. In our case, it demanded 0.7 bitcoins, which is about $320.
Perhaps the only visual discrepancy between CTB-Locker and its new clone is that MarsJoke/Polyglot leaves the encrypted files with their original extensions, whereas CTB-Locker changed the extension — usually to .ctbl or .ctb2. Despite the apparent similarities between Polyglot and CTB-Locker, they are two completely different malware species. They share almost no code. Our experts think that by mimicking CTB-Locker’s looks, Polyglot’s creators were trying to put researchers on the wrong track.
As you may know, there is no known way to decrypt files encrypted by CTB-Locker without paying the ransom. But again, Polyglot and CTB-Locker are not the same under the hood. And fortunately, Polyglot’s creator made a mistake with the key generator, and that made it possible for researchers to come up with a cure — a free utility that can decrypt all of the damaged files. To decrypt the files encrypted by Polyglot/MarsJoke, download and install the free RannohDecryptor utility (version 1.9.3.0 or newer) from noransom.kaspersky.com. It will restore your files.
Truth be told, experts got lucky with Polyglot/MarsJoke. Malware creators are constantly adapting and improving their creations. For example, after experts solved CryptXXX three times, its creator finally tuned the encryption algorithm such that our utilities could not handle it. Maybe Polyglot’s creator will manage the same feat. Bottom line: You can’t rely on a decryption utility being available for any ransomware you might encounter.
The best way to stay safe from ransomware is to catch it before it starts doing anything. And that is what good antivirus solutions do. To be on the safe side, experts also recommend that you back up your data frequently and avoid opening suspicious attachments or clicking on suspicious links.
Axarhöfði 14,
110 Reykjavik, Iceland














