Cryptolocker flogged on YouTube
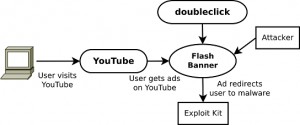
Cryptolocker is being flogged over YouTube by vxers who have bought advertising space, researchers Vadim Kotov and Rahul Kashyap have found.
 The researchers made the discovery while monitoring YouTube and website banners for instances where malware writers had actually purchased space to foist their wares on unpatched web users.
The researchers made the discovery while monitoring YouTube and website banners for instances where malware writers had actually purchased space to foist their wares on unpatched web users.
The duo who will present at the upcoming Virus Bulletin 2014 conference in Seattle wrote in a paper advertisement networks was a viable way to flog virus and trojans. "We conclude that ad networks could be leveraged to aid, or even be substituted for current exploit kits," they said.
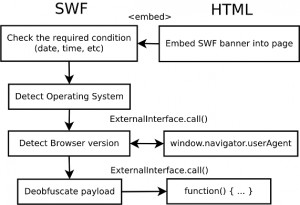
Purchased ad space was a cheap and effective means of foisting browser malware allowing attackers to filter victims by language, location, and interests, VB reported. Malware contained in ads could be obfuscated and then unleashed once conditions like operating systems, browser versions and other elements were met.
CryptoLocker surfaced in September distributed through Gameover ZeuS. It encrypted important files such as images and documents on compromised Windows machines before demanding that victim pay up to $500 in BitCoins within 72 hours for the private keys necessary to unlock files.
CryptoLocker used AES symmetric cryptography to encrypt the files and encrypted the AES key with an RSA-2048 bit public key generated on its server side.
In apparent uptick in malvertising prompted the US Senate to issue a report Online advertising and hidden hazards to consumer security and data privacy and said the Federal Trade Commission should enforce better industry protections against the scams.
Many excess ad spaces were flogged through affiliates which may accept advertisements without checking the authenticity of the buyer nor the code to be run. Even those that do could end up foisting malware if they failed to detect an attackers' code alterations made after the purchase in order to quietly slip in the malware.
The research pair said there was very little advertising networks could do to prevent the attacks.
Axarhöfði 14,
110 Reykjavik, Iceland