Are you Android user? New Trojan is coming
Due to the appearance of a great amount of new extortion viruses, which like only Android devices, hackers have estimated a new way how to earn.
 Almost all malwares that spread are working on the same pattern: after the launch, Trojan locks the device and gets a message about money transfer to unlock. This is a very clear example of fraud.
Almost all malwares that spread are working on the same pattern: after the launch, Trojan locks the device and gets a message about money transfer to unlock. This is a very clear example of fraud.
Nevertheless this virus, found by Dr.Web experts, is more functional: except locking the device and message payment, he immediately puts a password on unlock screen using a simple system diagram.
In addition, Trojan sends all kinds of messages that can lead to large financial losses.
Attackers extend this program as system updates that require administrator rights while starting. Then the appearance of installation is created, during which Trojan deletes its icon from the screen, and sends data that the phone has successfully infected to hackers.
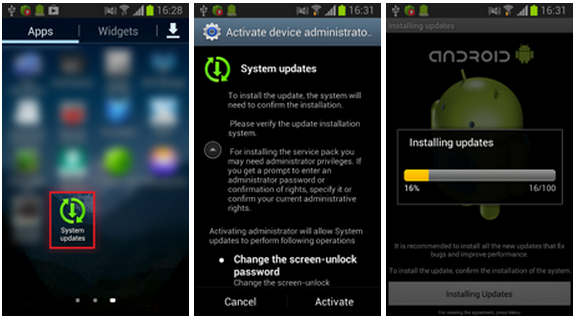
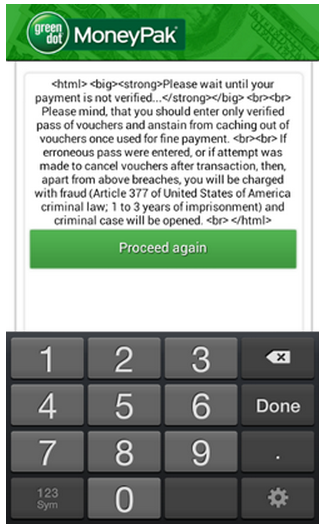
Then it is waiting for further orders, which hackers can sent with the help of JSON-request from web-server or by SMS with “set_lock” inscription. Just like other viruses of Android.Locker class, Android.Locker.38.origin locks the device, highlighting the message about redemption at the same time, which is impossible to get rid of.
If you try to take away administrator rights from Trojan, Android.Locker.38.origin uses a stronger locking level that is not peculiar to any malware, associated with Android. Trojan puts the device into standby mode, thus locks the screen. If you try to unlock, the fake warning about deleting all data on the device comes up.
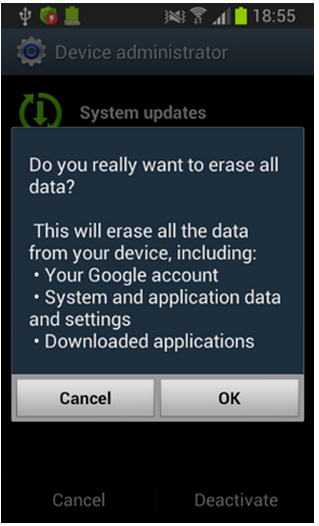
After confirmation, the gadget is locked again, while Android.Locker.38.origin activates the standard system function of password protection, during transition to «standby» mode. The fact whether the function was active before does not matter. The malware installs its own password, which contains such numbers as "12345".
As a result of all actions, mentioned above smartphone or tablet is permanently locked until the hackers get money (unlocking is possible only if hackers send “set_unlock” command) or reset to factory settings. Except locking of the devices, Android.Locker.38.origin has the function of SMS-bot that sends fake messages. It can lead to a great financial loss.
Axarhöfði 14,
110 Reykjavik, Iceland














