China intercepts iCloud logins
Chinese authorities are attacking users who are connecting to Apple's iCloud website in what appears to be a surveillance push to steal users' login credentials, according to a Chinese censorship monitoring group.
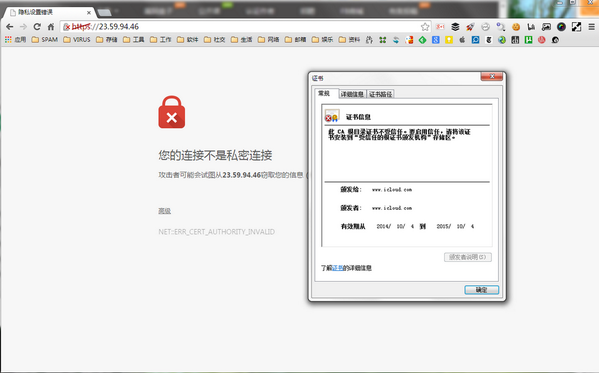
 In the attack, which was first reported on Saturday, less than 24 hours after the new iPhone 6 went on sale in China, connections to iCloud.com were hijacked and stripped of the usual encryption that prevents hackers and government spies from intercepting the username and password typed by someone connecting to the site.
In the attack, which was first reported on Saturday, less than 24 hours after the new iPhone 6 went on sale in China, connections to iCloud.com were hijacked and stripped of the usual encryption that prevents hackers and government spies from intercepting the username and password typed by someone connecting to the site.
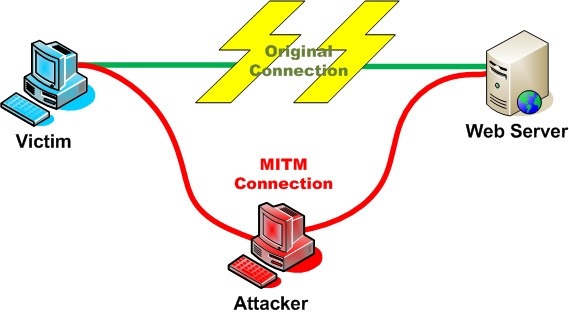
This is another example of what is technically known as a "man-in-the-middle" (MITM) attack, in which an attacker intercepts a connection between a user and a website in order to steal or tamper the data being exchanged. In the past year alone, China has been accused of intercepting connections with a MITM attack against Github, Google, and, more recently, Yahoo, in what was seen as an attempt to censor information on the Hong Kong protests.
After several users reported the attack online, the anti-Chinese censorship activist group GreatFire tweeted about the MITM attack. It's unclear whether the attack is being carried out by the Chinese government (calls to China's embassy press line did not receive an answer), but such an attack can only be performed by telecom providers or the government, according to experts.
"[It's] part of the trend of controlling and monitoring web services even more closely. Connections to iCloud.com were still affected at the time of writing.” (Apple did not answer to request for comment.) The attack on iCloud.com came just several weeks after another, which went almost unnoticed. This MITM attack affected users connecting to Microsoft's Hotmail and Live.com.
Microsoft confirmed the attack last week, though the company was cautious in describing the incident. "We’re aware of reports that a small number of account logins in China were affected by a redirect caused by invalid certificates," a Microsoft spokesperson told via email. (The spokesperson declined to respond a series of follow-up questions.)
"This is Microsoft's speech that we were attacked by China but we don't want to publicly accuse China to further enrage it," Alpha told in reaction to Microsoft's statement. The attack on Microsoft, like the one on iCloud, followed the same modus operandi as the previous MITM attacks in China against Github, Google and Yahoo. In these attacks, the connection between the user and the intended site, which is normally encrypted, is intercepted in China and redirected using a fake certificate, as confirmed by a forensic analysis of the attacks made by Erik Hjelmvik at Netresec.
Certificates are used to tell a browser that an encrypted connection goes to the intended site. Normally, when you go to iCloud.com, a certificate tells your Chrome or Safari browser that the site is indeed iCloud — and that your connection to it is secure. But with a fake certificate, an attacker can insert himself between the user and the website and intercept all data sent by the user, including usernames and passwords.
At this point, the reasons behind the attacks on Microsoft and Apple remain unclear. Segal, the Council on Foreign Relations expert, noted that in August, Apple pledged to move Chinese iCloud users' data into China. With that data inside the country, China could access users' data through legal means, without having to steal their passwords, Segal said.
Collin Anderson, a security researchers who focuses on online censorship and surveillance, was surprised by China's attack on Microsoft. In that case, he noted, the fake certificate had a typo in it. Instead of "hotmail.com," the certificate read "hotmai.com," which seemed to indicate a lack of attention to detail and thus a lack of concern with getting caught, Anderson said.
Despite the typo, many likely ignored their browser's warning and clicked through, allowing China to steal their credentials, Anderson told. "This the dumbest way of going about that sort of trick." China could likely carry out even more sophisticated and harder-to-detect MITM attacks, but these are still worrisome.
"This certainly is becoming a trend," Michael Carbone, a technologist at the human rights organization Access, told. "It let's Silicon Valley know that even if you are very cooperative with Chinese government authorities your customers may get targeted."
Axarhöfði 14,
110 Reykjavik, Iceland














