Firefox, Chrome start calling HTTP connections insecure
 Firefox 51, released today, and Chrome 56, currently due for release next week, have started describing some HTTP connections as insecure as they continue the industry-wide push to promote the use of encrypted HTTPS.
Firefox 51, released today, and Chrome 56, currently due for release next week, have started describing some HTTP connections as insecure as they continue the industry-wide push to promote the use of encrypted HTTPS.
As luck would have it, Chrome 56 was released while I was writing, and is out now. Rollouts are staggered, so systems should see the update over the next few days. The non-secure labelling will occur on pages delivered over HTTP that include forms. Specifically, pages that include password fields, and in Chrome, credit card fields, will put warnings in the address bar to explicitly indicate that the connection is not secure.
Read more95% of HTTPS servers vulnerable to trivial connection hijacking
 With just 5 percent of web servers correctly implementing HTTP Strict Transport Security, the remaining 95 percent are vulnerable to trivial connection hijacking attacks, research shows.
With just 5 percent of web servers correctly implementing HTTP Strict Transport Security, the remaining 95 percent are vulnerable to trivial connection hijacking attacks, research shows.
As Netcraft’s Paul Mutton explained in a recent blog post, these vulnerabilities can be exploited in phishing, pharming and man-in-the-middle (MiTM) attacks when a user unintentionally attempts to access a secure site via HTTP, meaning that the attacker does not have to spoof a valid TLS certificate to be successful. These attacks are easier to be carried out compared to those targeting TLS, such as the DROWN attack.
Read moreCookie handling in browsers can break HTTPS security
 Cookies, the files that websites create in browsers to remember logged-in users and track other information about them, could be abused by attackers to extract sensitive information from encrypted HTTPS connections.
Cookies, the files that websites create in browsers to remember logged-in users and track other information about them, could be abused by attackers to extract sensitive information from encrypted HTTPS connections.
The issue stems from the fact that the HTTP State Management standard which defines how cookies should be created and handled, does not specify any mechanism for isolating them or checking their integrity. As such, Web browsers don't always authenticate the domains that set cookies. ookies are also not isolated by port number or scheme. A server can host multiple websites accessible via the same domain, but on different port numbers.
Read moreGame-over HTTPS defects in dozens of Android apps expose user passwords
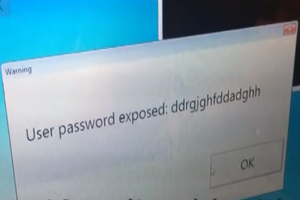 Researchers have unearthed dozens of Android apps in the official Google Play store that expose user passwords because the apps fail to properly implement HTTPS encryption during logins or don't use it at all.
Researchers have unearthed dozens of Android apps in the official Google Play store that expose user passwords because the apps fail to properly implement HTTPS encryption during logins or don't use it at all.
The roster of faulty apps have more than 200 million collective downloads from Google Play and have remained vulnerable even after developers were alerted to the defects. The apps include the official titles from the National Basketball Association, the Match.com dating service and the PizzaHut restaurant chain. They were uncovered by AppBugs, a developer of a free Android app that spots dangerous apps installed on users' handsets.
Read moreInternet.org is not neutral, not secure, and not the Internet
 Facebook's Internet.org project, which offers people from developing countries free mobile access to selected websites, has been pitched as a philanthropic initiative to connect two thirds of the world who don’t yet have Internet access.
Facebook's Internet.org project, which offers people from developing countries free mobile access to selected websites, has been pitched as a philanthropic initiative to connect two thirds of the world who don’t yet have Internet access.
The global digital divide should be closed and we agree that some Internet access is better than none. However, we question whether this is the right way to do it. There's a real risk that the few websites that Facebook and its partners select for Internet.org could end up becoming a ghetto for poor users instead of a stepping stone to the larger Internet.
Read moreHow to stay safe on public Wi-Fi networks
 Public Wi-Fi networks — like those in coffee shops or hotels — are not nearly as safe as you think. Even if they have a password, you're sharing a network with tons of other people, which means your data is at risk. Here's how to stay safe when you're out and about.
Public Wi-Fi networks — like those in coffee shops or hotels — are not nearly as safe as you think. Even if they have a password, you're sharing a network with tons of other people, which means your data is at risk. Here's how to stay safe when you're out and about.
Just because most wireless routers have a firewall to protect you from the internet doesn't mean you're protected from others connected to the same network. It's remarkably easy to steal someone's username and password, or see what they're doing just by being on the same network. Don't take that chance. We're going to show you which settings are the most important ones.
Read moreLogjam attack exposes data passed over TLS connections
 Scientists have identified weaknesses in the way popular cryptographic algorithm Diffie-Hellman key exchange is deployed – notably, they discovered an attack that could enable the reading and modifying of data passed over TLS connections.
Scientists have identified weaknesses in the way popular cryptographic algorithm Diffie-Hellman key exchange is deployed – notably, they discovered an attack that could enable the reading and modifying of data passed over TLS connections.
The attack can be used by a MITM attacker to downgrade TLS connections to 512-bit export-grade cryptography that is weaker and easier to crack, thus enabling the reading and modifying of data. The attack is similar to the FREAK attack, except it attacks Diffie-Hellman key exchange as opposed to RSA key exchange, and is the result of a flaw in TLS protocol.
Read more5 ways to protect your money online
 In a security survey asking why people complete their shopping online, 73 percent of respondents cited saving time as the primary reason. Shopping online can so easily be completed from a smartphone or tablet that its prevalence is rapidly increasing.
In a security survey asking why people complete their shopping online, 73 percent of respondents cited saving time as the primary reason. Shopping online can so easily be completed from a smartphone or tablet that its prevalence is rapidly increasing.
One report expects e-commerce revenues to more than double between 2012 and 2018. With identity theft cited as the Federal Trade Commission’s top consumer complaint for 13 years in a row, people have valid reason to be concerned about entering credit card numbers, addresses, and other personal information into a website form. There are, however, ways you can decrease your risk.
Read moreCoding website GitHub hit by massive DDoS attack
 A popular coding website of the USA is enduring an onslaught of Internet traffic meant for China’s most popular search engine, and security experts say the episode likely represents an attempt by China to shut down anticensorship tools.
A popular coding website of the USA is enduring an onslaught of Internet traffic meant for China’s most popular search engine, and security experts say the episode likely represents an attempt by China to shut down anticensorship tools.
The attack on a service world-wide software development used by programmers and major tech firms appears to underscore how China’s Internet censors increasingly reach outside the country to clamp down on content they find objectionable. Security experts said the traffic onslaught directed huge amounts of traffic from overseas users of Chinese search giant Baidu Inc. to GitHub.
Read morePopular apps are still vulnerable to FREAK attack
 A lot of Android apps that have been downloaded 6.3 billion times from the Google Play store are still vulnerable to the FREAK bug. Research published Tuesday by the company shows just how vulnerable both Android and iOS apps still are to a FREAK attack.
A lot of Android apps that have been downloaded 6.3 billion times from the Google Play store are still vulnerable to the FREAK bug. Research published Tuesday by the company shows just how vulnerable both Android and iOS apps still are to a FREAK attack.
FREAK is a cryptographic weakness that permits attackers to force data traveling between a vulnerable website or operating system to servers to use weak encryption protocols. If combined with a so-called man-in-the-middle attack, the data could theoretically be intercepted and cracked as the user is unwittingly using a lower level of encryption than believed.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















