FBI says it can't release iPhone hacking tool because it might still be useful
 Justice Dept. officials say that details of a hacking tool used to access a terrorist's iPhone should not be released because it may still be "useful" to federal investigators.
Justice Dept. officials say that details of a hacking tool used to access a terrorist's iPhone should not be released because it may still be "useful" to federal investigators.
The government is fighting a case against three news organizations, which are fighting to release details of the hacking tool that FBI agents used to unlock a passcode-protected phone used by San Bernardino shooter Syed Farook. Details of the hacking tool have remained classified, not least because the Justice Dept. believes the tool may still be used by the FBI in similar cases. A third-party company created the hacking tool that was used to break the passcode lock on the iPhone 5c, the company's name has not been revealed.
Read moreFBI probes FDIC hack linked to China's military
 The FBI is investigating how hackers infiltrated computers at the Federal Deposit Insurance Corporation for several years beginning in 2010 in a breach senior FDIC officials believe was sponsored by China's military.
The FBI is investigating how hackers infiltrated computers at the Federal Deposit Insurance Corporation for several years beginning in 2010 in a breach senior FDIC officials believe was sponsored by China's military.
The security breach, in which hackers gained access to dozens of computers including the workstation for former FDIC Chairwoman Sheila Bair, has also been the target of a probe by a congressional committee. The FDIC is one of three federal agencies that regulate commercial banks in the USA. It oversees confidential plans for how big banks would handle bankruptcy and has access to records on millions of individual American deposits.
Read moreFBI to gain expanded hacking powers as Senate effort to block fails
 A last-ditch effort in the Senate to block or delay rule changes that would expand the U.S. government's hacking powers failed Wednesday, despite concerns the changes would jeopardize the privacy rights of innocent Americans and risk possible abuse by the incoming administration of President-elect Donald Trump.
A last-ditch effort in the Senate to block or delay rule changes that would expand the U.S. government's hacking powers failed Wednesday, despite concerns the changes would jeopardize the privacy rights of innocent Americans and risk possible abuse by the incoming administration of President-elect Donald Trump.
Democratic Senator Ron Wyden attempted three times to delay the changes, which will take effect on Thursday and allow U.S. judges will be able to issue search warrants that give the FBI the authority to remotely access computers in any jurisdiction, potentially even overseas. His efforts were blocked by Senator John Cornyn of Texas.
Read moreThe FBI used a non-public vulnerability to hack suspects on Tor
 When the FBI hacked thousands of computers related to a child porn investigation in 2015, the agency took advantage of a “non-publicly-known vulnerability,” according to a judge in a related case.
When the FBI hacked thousands of computers related to a child porn investigation in 2015, the agency took advantage of a “non-publicly-known vulnerability,” according to a judge in a related case.
The news highlights the ongoing trend of the FBI leveraging security issues in software and devices, especially as criminal suspects turn to anonymization technology such as Tor, or use consumer products that have encryption features baked into them. In this case, the vulnerability may not have been a so-called zero-day which would bring up contentious issues of the FBI’s responsibility to disclose it to affected parties.
Read moreFBI hacked into over 8,000 computers in 120 countries with just one warrant
 In January, experts reported on the FBI's “unprecedented” hacking operation, in which the agency, using a single warrant, deployed malware to over one thousand alleged visitors of a dark web child pornography site. Now, it has emerged that the campaign was actually several orders of magnitude larger.
In January, experts reported on the FBI's “unprecedented” hacking operation, in which the agency, using a single warrant, deployed malware to over one thousand alleged visitors of a dark web child pornography site. Now, it has emerged that the campaign was actually several orders of magnitude larger.
In all, the FBI obtained over 8,000 IP addresses, and hacked computers in 120 different countries, according to a transcript from a recent evidentiary hearing in a related case. The figures illustrate the largest ever known law enforcement hacking campaign to date, and starkly demonstrate what the future of policing crime on the dark web may look like.
Read moreFeds can unlock most devices they need to get into
 The FBI is able to unlock or access data on most of the phones and computers it encounters during its investigations, as well as those of local and state cops, according to the bureau’s General Counsel Jim Baker.
The FBI is able to unlock or access data on most of the phones and computers it encounters during its investigations, as well as those of local and state cops, according to the bureau’s General Counsel Jim Baker.
So far in the fiscal year 2016, the FBI has encountered passwords or passcodes—that is locked phones or laptops—in 31 percent mobile devices analyzed by its forensic labs, Baker said according to attendants at a public meeting on encryption and the challenges it poses to law enforcement, celebrated in Washington DC on Friday. The numbers disclosed by Baker, which have never been published before, seem to indicate that the reality, however, is a little different.
Read moreUnsealed court docs show FBI used malware like a grenade
 In 2013, the FBI received permission to hack over 300 specific users of dark web email service TorMail. But now, after the warrants and their applications have finally been unsealed, experts say the agency illegally went further, and hacked perfectly legitimate users of the privacy-focused service.
In 2013, the FBI received permission to hack over 300 specific users of dark web email service TorMail. But now, after the warrants and their applications have finally been unsealed, experts say the agency illegally went further, and hacked perfectly legitimate users of the privacy-focused service.
“That is, while the warrant authorized hacking with a scalpel, the FBI delivered their malware to TorMail users with a grenade,” Christopher Soghoian, principal technologist at the American Civil Liberties Union, told in an email. The move comes after the ACLU pushed to unseal the case dockets in September.
Read moreYahoo: an innocent victim or a government stooge?
 Someone in mid-2015 had installed software that scanned emails containing a string of characters, just as a nation state hacker might if they sought specific information without having to go through each message manually.
Someone in mid-2015 had installed software that scanned emails containing a string of characters, just as a nation state hacker might if they sought specific information without having to go through each message manually.
It turned out, though, that unlike a recently-revealed 2014 attack, a foreign state was not to blame. Instead, Yahoo executives helped the US government install a tool that would scan every email for that string, still unknown outside of those who carried out the surveillance project. CEO Marissa Mayer and her lawyers decided not to tell the Yahoo security team, a group called the Paranoids well-known for its dislike of invasive state surveillance.
Read moreFBI says hackers have made more attempts to breach state voter registration systems
 During a House Judiciary Committee hearing, FBI Director James Comey revealed hackers have attempted to hack into voter registration sites in more than a dozen states and on several occasions. Investigators believe Russia is behind the attempted hacks, officials said.
During a House Judiciary Committee hearing, FBI Director James Comey revealed hackers have attempted to hack into voter registration sites in more than a dozen states and on several occasions. Investigators believe Russia is behind the attempted hacks, officials said.
"There have been a variety of scanning activities which is a preamble for potential intrusion activities as well as some attempted intrusions at voter database registrations beyond those we knew about in July and August," Comey said. Comey told states to remain vigilant of their voter registration systems, warning that would-be hackers are "poking around".
Read moreFBI director — you should cover your webcam with tape
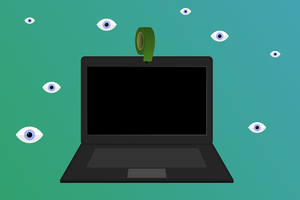 Should you put a tape or a sticker over the lens of your laptop's webcam? Yes, even Facebook CEO Mark Zuckerberg and FBI Director James Comey do that. Covering your laptop's webcam might be a hell cheap and good idea to guard against hackers and intruders who might want to watch your private life and environment through your devices.
Should you put a tape or a sticker over the lens of your laptop's webcam? Yes, even Facebook CEO Mark Zuckerberg and FBI Director James Comey do that. Covering your laptop's webcam might be a hell cheap and good idea to guard against hackers and intruders who might want to watch your private life and environment through your devices.
In fact, Comey recently came out defending his own use of tape to cover his personal laptop's webcam. However, putting a tape over the lens of your computer's webcam would not solve the problem, especially in this era when we are surrounded by so many Internet-connected devices that are a security nightmare.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















