Spy agency NSA triples collection of U.S. phone records
 The National Security Agency collected 534 million records of phone calls and text messages of Americans last year, more than triple gathered in 2016.
The National Security Agency collected 534 million records of phone calls and text messages of Americans last year, more than triple gathered in 2016.
The sharp increase from 151 million occurred during the second full year of a new surveillance system established at the spy agency after U.S. lawmakers passed a law in 2015 that sought to limit its ability to collect such records in bulk. The spike in collection of call records coincided with an increase reported on Friday across other surveillance methods, raising questions from some privacy advocates who are concerned about potential government overreach and intrusion into the lives of U.S. citizens.
Read moreThe NSA worked to “track down” bitcoin users, Snowden documents reveal
 Internet paranoiacs drawn to bitcoin have long indulged fantasies of American spies subverting the booming, controversial digital currency.
Internet paranoiacs drawn to bitcoin have long indulged fantasies of American spies subverting the booming, controversial digital currency.
Increasingly popular among get-rich-quick speculators, bitcoin started out as a high-minded project to make financial transactions public and mathematically verifiable — while also offering discretion. Governments, with a vested interest in controlling how money moves, would, some of bitcoin’s fierce advocates believed, naturally try and thwart the coming techno-libertarian financial order. It turns out the conspiracy theorists were onto something.
Read moreHacking group expands espionage operation with new attacks
 A hacking operation has expanded its operations taking advantage of new tools - including the EternalBlue SMB exploit - to attack organisations across the Middle East for the purposes of surveillance and intelligence gathering.
A hacking operation has expanded its operations taking advantage of new tools - including the EternalBlue SMB exploit - to attack organisations across the Middle East for the purposes of surveillance and intelligence gathering.
Targets are mostly working in telecoms and transport and their surrounding supply chains - with IT software, payroll, aircraft services and engineering firms all targets during the last year. The operations of Chafer, an Iran-based targeted attack group have been detailed by researchers at security company Symantec, who note that since first being exposed in 2015, the group has expanded its surveillance and cyber attack operations.
Read moreCryptocurrency mining malware that uses an NSA exploit is on the rise
 A computer security exploit developed by the US National Security Agency and leaked by hackers last year is now being used to mine cryptocurrency, and according to cybersecurity experts the number of infections is rising.
A computer security exploit developed by the US National Security Agency and leaked by hackers last year is now being used to mine cryptocurrency, and according to cybersecurity experts the number of infections is rising.
Last April, a hacking group called the Shadow Brokers leaked EternalBlue, a Windows exploit that was developed by the NSA. Less than a month later, EternalBlue was used to unleash a devastating global ransomware attack called WannaCry that infected more than 230,000 computers in 150 countries. A month later, in June, the EternalBlue exploit was again used to cripple networks across the world in an even more sophisticated attack.
Read more"Zealot" campaign uses NSA exploits to mine Monero on Windows and Linux servers
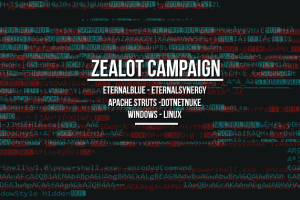 An aggressive and sophisticated malware campaign is currently underway, targeting Linux and Windows servers with an assortment of exploits with the goal of installing malware that mines the Monero cryptocurrency.
An aggressive and sophisticated malware campaign is currently underway, targeting Linux and Windows servers with an assortment of exploits with the goal of installing malware that mines the Monero cryptocurrency.
The campaign was detected by security researchers from F5 Networks, who named it Zealot, after zealot.zip, one of the files dropped on targeted servers. According to Maxim Zavodchik and Liron Segal, two security researchers for F5 Networks, the attackers are scanning the Internet for particular servers and using two exploits, one for Apache Struts and one for the DotNetNuke ASP.NET CMS, to get a foothold on unpatched machines.
Read moreNew NSA leak exposes Red Disk, the Army's failed intelligence system
 The contents of a highly sensitive hard drive belonging to a division of the National Security Agency have been left online.
The contents of a highly sensitive hard drive belonging to a division of the National Security Agency have been left online.
The virtual disk image contains over 100 gigabytes of data from an Army intelligence project, codenamed "Red Disk." The disk image belongs to the US Army's Intelligence and Security Command, known as INSCOM, a division of both the Army and the NSA. The disk image was left on an unlisted but public Amazon Web Services storage server, without a password, open for anyone to download. Unprotected storage buckets have become a recurring theme in recent data leaks and exposures.
Read moreInternal Kaspersky investigation says NSA worker’s computer was infested with malware
 The personal computer of an NSA worker who took government hacking tools and classified documents home with him was infected with a backdoor trojan, unrelated to these tools, that could have been used by criminal hackers to steal the US government files.
The personal computer of an NSA worker who took government hacking tools and classified documents home with him was infected with a backdoor trojan, unrelated to these tools, that could have been used by criminal hackers to steal the US government files.
The Moscow-based antivirus firm, which has been accused of using its security software to improperly grab NSA hacking tools and classified documents from the NSA worker's home computer and provide them to the Russian government, says the worker had at least 120 other malicious files on his home computer.
Read moreSecurity breach and spilled secrets have shaken the NSA to its core
 Jake Williams awoke last April in an Orlando, Fla., hotel where he was leading a training session. Checking Twitter, Mr. Williams, a cybersecurity expert, was dismayed to discover that he had been thrust into the middle of one of the worst security debacles ever to befall American intelligence.
Jake Williams awoke last April in an Orlando, Fla., hotel where he was leading a training session. Checking Twitter, Mr. Williams, a cybersecurity expert, was dismayed to discover that he had been thrust into the middle of one of the worst security debacles ever to befall American intelligence.
Mr. Williams had written on his company blog about the Shadow Brokers, a mysterious group that had somehow obtained many of the hacking tools the United States used to spy on other countries. Now the group had replied in an angry screed on Twitter. It identified him — correctly — as a former member of the National Security Agency’s hacking group, Tailored Access Operations, or T.A.O., a job he had not publicly disclosed.
Read moreYou can spy like the NSA for a few thousand bucks
 Gaining access to the global network used by spies to track phone calls and intercept communications is relatively cheap and easy for hackers, criminals, or even anyone, an investigation has found.
Gaining access to the global network used by spies to track phone calls and intercept communications is relatively cheap and easy for hackers, criminals, or even anyone, an investigation has found.
The network, known as SS7, has faced renewed attention in the past few years, especially after researchers exploited it to eavesdrop on a congressman’s calls in real-time from the other side of the world. But a major concern is that more sinister hackers could conduct this sort of surveillance. To test just how possible opening the door to SS7 really is, experts posed as a small potential customer to a telecom in Europe, and was offered SS7 access for just a few thousand dollars.
Read moreKaspersky says it obtained suspected NSA hacking code from U.S. computer
 Moscow-based antivirus software maker Kaspersky Lab said on Wednesday that its security software had taken source code for a secret American hacking tool from a personal computer in the United States.
Moscow-based antivirus software maker Kaspersky Lab said on Wednesday that its security software had taken source code for a secret American hacking tool from a personal computer in the United States.
In September, U.S. officials ordered Kaspersky’s products removed from government computers, saying the firm was vulnerable to Kremlin influence and that using the software could jeopardize national security. After that announcement, the Wall Street Journal reported on Oct. 5 that hackers working for the Russian government appeared to have targeted a National Security Agency (NSA) worker by using Kaspersky software to identify classified files in 2015.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















