A new spam targets corporations
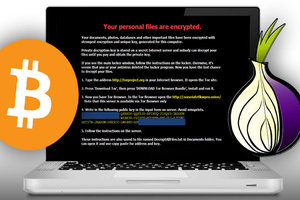
 A new spam wave has hit hundreds of mailboxes with malicious .chm attachments to spread the infamous Cryptowall ransomware.
A new spam wave has hit hundreds of mailboxes with malicious .chm attachments to spread the infamous Cryptowall ransomware.
Cryptowall is an advanced version of Cryptolocker, a file-encrypting ransomware known for disguising its viral payload as a non-threatening application or file. Its payload encrypts the files of infected computers in an effort to extract money for the decryption key. Malware researchers found that the email blast, which took place in February, targeted users from around the world, including the UK, the US, the Netherlands, Denmark, Sweden, Slovakia and Australia.
Read moreCTB-Locker is the newest crypto malware
 From late 2013 through the first half of 2014, CryptoLocker malware was a major concern for many businesses and individuals. The FBI was able to successfully disrupt CryptoLocker, along with Game Over Zeus, but according to the figures in their legal complaint against Evgeniy Bogachev, not before his malware had encrypted a lot of computers.
From late 2013 through the first half of 2014, CryptoLocker malware was a major concern for many businesses and individuals. The FBI was able to successfully disrupt CryptoLocker, along with Game Over Zeus, but according to the figures in their legal complaint against Evgeniy Bogachev, not before his malware had encrypted a lot of computers.
The second major Crypto Malware was CryptoWall. In Malcovery's 3rd Quarter malware report, there were documented 24 separate spam campaigns that resulted in CryptoWall infections. Today we may have seen the beginning of the Next Wave of Crypto Malware being delivered by spam.
Read moreCryptoWall ransomware infects millions
 A sophisticated cyber-crime campaign is leaving millions of people vulnerable to having malware installed on their computers simply by visiting high profile websites.
A sophisticated cyber-crime campaign is leaving millions of people vulnerable to having malware installed on their computers simply by visiting high profile websites.
The campaign is using the fast-growing method of 'malvertising' to spread a pernicious form of malware called ransomware, which encrypts all the files on the hard drive of a victim's computer, and if the victim doesn't pay a ransom by deadline, those files are lost forever. The researchers were even able to estimate how much money the criminals were earning on a daily basis as the ransoms are charged in bitcoin, meaning all payments are traceable via the public blockchain.
Read moreFBI against cellphone encryption
 FBI Director warned in stark terms Thursday against the push by technology companies to encrypt smartphone data and operating systems, arguing that murder cases could be stalled, suspects could walk free and justice could be thwarted by a locked phone or an encrypted hard drive.
FBI Director warned in stark terms Thursday against the push by technology companies to encrypt smartphone data and operating systems, arguing that murder cases could be stalled, suspects could walk free and justice could be thwarted by a locked phone or an encrypted hard drive.
Privacy advocates and technology experts called the concerns exaggerated and little more than recycled arguments the government has raised against encryption since the early 1990s. Likening encrypted data to a safe that cannot be cracked or a closet door that won't open, the move by tech companies to protect user communications in the name of privacy is certain to impede a wide range of criminal investigations.
Read moreCryptoWall ransomware scam rakes in $1 MEEELLION
 Victims of the CryptoWall ransomware have been extorted out of at least $1m. Despite a takedown operation in June, CryptoWall continues to be the largest and most destructive ransomware threat on the internet, according to the latest analysis of the threat by security researchers from Dell SecureWorks Counter Threat Unit.
Victims of the CryptoWall ransomware have been extorted out of at least $1m. Despite a takedown operation in June, CryptoWall continues to be the largest and most destructive ransomware threat on the internet, according to the latest analysis of the threat by security researchers from Dell SecureWorks Counter Threat Unit.
Cryptowall is a strain of file-encrypting ransomware that encrypts files on infected Windows PCs and attached storage devices with RSA-2048 encryption before demanding a ransom for the private key that recovers the documents. Dell SecureWorks CTU researchers registered a domain used by the CryptoWall malware as a backup command and control (C2) server in February.
Read moreTrueCrypt: an unexplained disappearance
 Something very weird is going on with the popular free whole-disk encryption suite TrueCrypt. The story is still developing, but it does look like the suite ceases to exist right now. The only explanation its creators have provided so far is that using TrueCrypt “is not secure as it may contain unfixed security issues”.
Something very weird is going on with the popular free whole-disk encryption suite TrueCrypt. The story is still developing, but it does look like the suite ceases to exist right now. The only explanation its creators have provided so far is that using TrueCrypt “is not secure as it may contain unfixed security issues”.
What kind of issues? – This is something people behind TrueCrypt have not disclosed so far. There are some speculations about the possibility of a backdoor in the software code, but it’s guesswork at best. There was also speculation of a possible deface: TrueCrypt’s official site started redirecting people to the suite’s Sourceforge page all of sudden.
Read moreTrueCrypt shuts down and may be compromised
.jpg) Independent encryption software TrueCrypt is apparently not as secure as many thought. The TrueCrypt homepage was suddenly replaced with a notification that read "WARNING: Using TrueCrypt is not secure as it may contain unfixed security issues."
Independent encryption software TrueCrypt is apparently not as secure as many thought. The TrueCrypt homepage was suddenly replaced with a notification that read "WARNING: Using TrueCrypt is not secure as it may contain unfixed security issues."
Moreover, it is reported that since May, 2014 TrueCrypt development is stopped. Significantly, the current version listed on the SourceForge page, version 7.2, was signed with the official TrueCrypt private signing key, the same key used by the TrueCrypt Foundation for as long as two years. This means the warning on the official homepage of TrueCrypt isn't a hoax posted by some hacker or cyber criminal.
Read moreTrueCrypt for Windows: No major flaws found in first phase of security audit
 The first round of results are in, and so far TrueCrypt, the popular open-source encryption program, has a relatively clean bill of health. Security firm iSec Partners recently carried out the first phase of the TrueCrypt audit on behalf of the Open Crypto Audit Project (OCAP).
The first round of results are in, and so far TrueCrypt, the popular open-source encryption program, has a relatively clean bill of health. Security firm iSec Partners recently carried out the first phase of the TrueCrypt audit on behalf of the Open Crypto Audit Project (OCAP).
OCAP is the official name for the group behind istruecryptauditedyet.com, a project inspired by the revelations about the National Security Agency’s surveillance activities. OCAP was created by Matthew Green, a cryptographer and research professor at Johns Hopkins University, and Kenneth White, Principal Scientist at Social & Scientific Systems. For its report, which was released on Monday, iSec took a look at TrueCrypt’s latest Windows edition (version 7.1a).
Read moreStarbucks admits its iPhone app stores unencrypted user passwords
 When you type a password into a mobile payment app, you'd probably expect it to protect that password somehow. But it seems that the Starbucks app for iOS doesn't actually lock its usernames and passwords down. According to a Computerworld report, company executives admitted today that the mobile app stores passwords in clear text, with no encryption of any sort. By connecting your phone to a computer, the report claims, someone could easily retrieve your password from a crash log.
When you type a password into a mobile payment app, you'd probably expect it to protect that password somehow. But it seems that the Starbucks app for iOS doesn't actually lock its usernames and passwords down. According to a Computerworld report, company executives admitted today that the mobile app stores passwords in clear text, with no encryption of any sort. By connecting your phone to a computer, the report claims, someone could easily retrieve your password from a crash log.
What's more, it appears that Starbucks may not intend to actually fix the problem. While the company told both Computerworld and The Seattle Times that the company had "taken steps to safeguard customers' information," it's unclear what steps it could have taken.
Read more New secured zone of Google Play: secure messenger SafeUM for Android. Download, Install, Communicate
New secured zone of Google Play: secure messenger SafeUM for Android. Download, Install, Communicate
Axarhöfði 14,
110 Reykjavik, Iceland














