Attackers exploit Apple DRM weakness to infect non-jailbroken iOS devices
 Palo Alto Networks revealed today the existence of a new iOS trojan called AceDeceiver that can infect both jailbroken and non-jailbroken devices, leveraging a design flaw in Apple's FairPlay DRM system.
Palo Alto Networks revealed today the existence of a new iOS trojan called AceDeceiver that can infect both jailbroken and non-jailbroken devices, leveraging a design flaw in Apple's FairPlay DRM system.
This design flaw is not new, it's called FairPlay Man-in-the-Middle, and was observed in the wild for the first time in February 2013, used for spreading pirated apps, and later presented in depth at the 23rd USENIX Security Symposium. AceDeceiver marks the first time a FairPlay MitM attack was used to spread malware. FairPlay MitM is a simple MitM attack in which the attacker plays an intermediary role between the App Store and a user's computer or iOS device.
Read more4 new ways to bypass passcode lock screen on iPhones
 There are multiple bypass vulnerabilities which could allow an attacker to get past the passcode lock screen on Apple devices running iOS 9. The details for four different attack scenarios were disclosed by Vulnerability Lab. It’s important to note that an attacker would need physical access to the device to pull this off.
There are multiple bypass vulnerabilities which could allow an attacker to get past the passcode lock screen on Apple devices running iOS 9. The details for four different attack scenarios were disclosed by Vulnerability Lab. It’s important to note that an attacker would need physical access to the device to pull this off.
Security researcher Benjamin Kunz Mejri, who disclosed a different method for disabling the passcode lock screen on iOS 8 and iOS 9 about a month ago, discovered the flaws. Vulnerability Lab posted a proof-of-concept video showing multiple new ways for a local attacker to bypass the passcode in iOS 9 and gain unauthorized access to the device.
Read moreTim Cook hits back at 'chilling' order for iPhone backdoor
 Apple CEO Tim Cook denounced a federal judge's order to crack open an iPhone used by a terrorist, calling the situation "chilling" and saying it would deal a major setback to online privacy for all.
Apple CEO Tim Cook denounced a federal judge's order to crack open an iPhone used by a terrorist, calling the situation "chilling" and saying it would deal a major setback to online privacy for all.
To hack the phone, the FBI wants Apple to build a new version of its iOS software that Cook claims bypasses the iPhone's security features and creates "the potential to unlock any iPhone in someone's physical possession." "The US government has asked us for something we simply do not have, and something we consider too dangerous to create," Cook wrote in an open letter posted on Apple's website. "They have asked us to build a backdoor to the iPhone."
Read morePopular hot patching technique puts iOS users at risk
 Do you know?… Any iOS app downloaded from Apple’s official App Store has an ability to update itself from any 3rd-party server automatically without your knowledge. Yes, it is possible, and you could end up downloading malware on your iPhone or iPad.
Do you know?… Any iOS app downloaded from Apple’s official App Store has an ability to update itself from any 3rd-party server automatically without your knowledge. Yes, it is possible, and you could end up downloading malware on your iPhone or iPad.
Unlike Google, Apple has made remarkable efforts to create and maintain a healthy and clean ecosystem of its official App Store. Although Apple's review process and standards for security and integrity are intended to protect iOS users, developers found the process time consuming and extremely frustrating while issuing a patch for a severe bug or security flaw impacting existing app users.
Read moreWarning! People are sharing a link that will crash and reboot your iPhone
 A new prank circulating on Twitter, Facebook and other social media platform could crash your iPhone or iPad completely. If you come across a link to crashsafari.com, you are advised not to open it on your iPhone, iPad or even Macs.
A new prank circulating on Twitter, Facebook and other social media platform could crash your iPhone or iPad completely. If you come across a link to crashsafari.com, you are advised not to open it on your iPhone, iPad or even Macs.
Doing so will cause Safari application to crash, potentially causing your Apple device to restart. In case, you want to try this out, just click here to visit the website and watch what happens. Currently, people are spreading the link to CrashSafari.com via Twitter using a URL shortener, and users are tricked into visiting the site without being knowing. How does this Prank Work?
Read moreCybercriminals will target Apple in 2016
 Cybercriminals are increasingly targeting Apple devices and 2016 will see a rise in attacks on its operating systems, security experts suggest. According to security firm Symantec, the amount of malware aimed at Apple's mobile operating system has more than doubled this year, while threats to Mac computers also rose.
Cybercriminals are increasingly targeting Apple devices and 2016 will see a rise in attacks on its operating systems, security experts suggest. According to security firm Symantec, the amount of malware aimed at Apple's mobile operating system has more than doubled this year, while threats to Mac computers also rose.
Security firm FireEye also expects 2016 to be a bumper year for Apple malware. Systems such as Apple Pay could be targeted, it predicts. Apple is an obvious target for cybercriminals because its products are so popular. While the total number of threats targeting Apple devices remains low compared with Windows and Android.
Read moreiOS apps more vulnerable than Android
 Applications written for iOS devices have more vulnerabilities than those written for Androids, and this has the potential for security problems in the future as attackers move to application-based threat vectors.
Applications written for iOS devices have more vulnerabilities than those written for Androids, and this has the potential for security problems in the future as attackers move to application-based threat vectors.
According to a new report from mobile application security vendors Checkmarx and AppSec Labs, the average mobile app has nine vulnerabilities. Of the iOS vulnerabilities, 40 percent were critical or high severity, compared to 36 percent of the Android vulnerabilities, said Amit Ashbel, product marketing manager at Checkmarx. Researchers tested hundreds of applications of all types, including banking, utilities, retail, gaming and security.
Read moreUser data plundering by Android and iOS apps is as rampant as you suspected
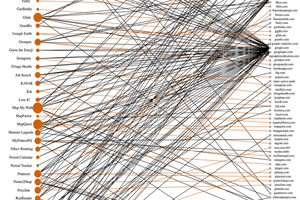 Apps in both Google Play and the Apple App Store frequently send users' highly personal information to third parties, often with little or no notice.
Apps in both Google Play and the Apple App Store frequently send users' highly personal information to third parties, often with little or no notice.
The researchers analyzed 55 of the most popular apps from each market and found that a significant percentage of them regularly provided Google, Apple, and other third parties with user e-mail addresses, names, and physical locations. Android apps sent potentially sensitive data to 3.1 third-party domains while the average iOS app sent it to 2.6 third-party domains. In some cases, health apps sent searches including words such as "herpes" and "interferon" to no fewer than five domains with no notification that it was happening.
Read moreXcodeGhost iOS malware strikes US enterprises
 A new variant of XcodeGhost has been discovered in the wild, leaving China behind to tackle US companies. In September this year, researchers discovered malware able to infect legitimate Apple iOS applications.
A new variant of XcodeGhost has been discovered in the wild, leaving China behind to tackle US companies. In September this year, researchers discovered malware able to infect legitimate Apple iOS applications.
The malicious code, known as XcodeGhost, lurked within at least 4000 legitimate iOS apps offered to the Chinese market, placing millions of users at risk. The malware was able to hijack apps through the developer toolkit Xcode, which is used to develop software for Apple's ecosystem. By adding the code to Xcode packages hosted on third-party websites rather than Apple domains, cybercriminals were able to bypass Apple's stringent security protocols.
Read moreResearchers find 256 iOS apps that collect users’ personal info
 Researchers said they've found more than 250 iOS apps that violate Apple's App Store privacy policy forbidding the gathering of e-mail addresses, installed apps, serial numbers, and other personally identifying information that can be used to track users.
Researchers said they've found more than 250 iOS apps that violate Apple's App Store privacy policy forbidding the gathering of e-mail addresses, installed apps, serial numbers, and other personally identifying information that can be used to track users.
The apps, which at most recent count totaled 256, are significant because they expose a lapse in Apple's vetting process for admitting titles into its highly curated App Store. They also represent an invasion of privacy to the one million people estimated to have downloaded the apps. The data gathering is so surreptitious that even the individual developers of the affected apps are unlikely to know about it.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















