Top secret designs could be stolen from 3D printers using an ordinary smartphone
 In the years to come, 3D printing is going to be used for everything from helping create rocket engines to printing new heart valves. With those kind of high-stakes — and often highly-valuable–applications, it’s no wonder experts are concerned about the security risk posed by hackers.
In the years to come, 3D printing is going to be used for everything from helping create rocket engines to printing new heart valves. With those kind of high-stakes — and often highly-valuable–applications, it’s no wonder experts are concerned about the security risk posed by hackers.
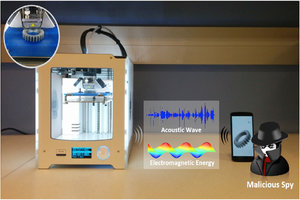
One possible threat is explored in a new study by researchers at the University at Buffalo in New York entitled “My Smartphone Knows What You Print: Exploring Smartphone-Based Side-Channel Attacks Against 3D Printers.” A team of computer scientists was able to use a regular smartphone’s built-in sensors to measure the electromagnetic energy and acoustic waves that emanate from a 3D printer.
Read morePrinters now the least-secure things on the internet
 The Internet of Things is exactly as bad a security nightmare as pessimists think it is, according to Bitdefender's Bogdan Botezatu.
The Internet of Things is exactly as bad a security nightmare as pessimists think it is, according to Bitdefender's Bogdan Botezatu.
The senior threat analyst at the Romanian security software company called by to chat to Vulture South while in Australia (we were, I suspect, meant to discuss the company's 2017 launches, but conversation digressed from the start, and there's plenty of time between now and the end of the year). Experts have long been following the persistent awfulness of “SOHOpeless” broadband routers, but Botezatu says they've already been overtaken by the awfulness of other things.
Read moreThe dangers of self-driving cars
 The very word automobile means self-moving. Through their history of more than a century, automobiles have evolved, increasingly taking over the driving process from humans. Many years ago, the car had to be started with a crank; such features as automatic transmission, cruise control, and automatic braking would come many years later.
The very word automobile means self-moving. Through their history of more than a century, automobiles have evolved, increasingly taking over the driving process from humans. Many years ago, the car had to be started with a crank; such features as automatic transmission, cruise control, and automatic braking would come many years later.
And now we are witnessing the emergence of fully driverless, automated cars. From the hardware point of view, there is nothing particularly complex about such vehicles. The wheels, engine, steering wheel, brakes, and various servos are just about the same as those in ordinary cars.
Read moreMirai Trojan is the next big threat to IoT devices and Linux servers
 A new trojan named Mirai has surfaced, and it's targeting Linux servers and IoT devices, mainly DVRs, running Linux-based firmware, for the purpose of enslaving these systems as part of a large botnet used to launch DDoS attacks. Mirai is an evolution of an older trojan, also used for DDoS attacks.
A new trojan named Mirai has surfaced, and it's targeting Linux servers and IoT devices, mainly DVRs, running Linux-based firmware, for the purpose of enslaving these systems as part of a large botnet used to launch DDoS attacks. Mirai is an evolution of an older trojan, also used for DDoS attacks.
Mirai's mode of operation is largely the same as Gafgyt, targeting IoT devices running Busybox, a slimmed-down version of select GNU tools and libraries, usually deployed on small embedded hardware. The trojan also targets only a specific set of platforms, on which IoT devices are usually built.
Read moreHackers make the first-ever ransomware for smart thermostats
 One day, your thermostat will get hacked by some cybercriminal hundreds of miles away who will lock it with malware and demand a ransom to get it back to normal, leaving you literally in the cold until you pay up a few hundred dollars.
One day, your thermostat will get hacked by some cybercriminal hundreds of miles away who will lock it with malware and demand a ransom to get it back to normal, leaving you literally in the cold until you pay up a few hundred dollars.
This has been a scenario that security experts have touted as one of the theoretical dangers of the rise of the Internet of Things, internet-connected devices that are often insecure. On Saturday, what sounds like a Mr. Robot plot line came one step closer to being reality, when two white hat hackers showed off the first-ever ransomware that works against a “smart” device, in this case a thermostat.
Read moreNSA looking to exploit Internet of Things, including biomedical devices
 The national security agency is researching opportunities to collect foreign intelligence — including the possibility of exploiting internet-connected biomedical devices like pacemakers, according to a senior official.
The national security agency is researching opportunities to collect foreign intelligence — including the possibility of exploiting internet-connected biomedical devices like pacemakers, according to a senior official.
“We’re looking at it sort of theoretically from a research point of view right now,” Richard Ledgett, the NSA’s deputy director, said at a conference on military technology at Washington’s Newseum. Biomedical devices could be a new source of information for the NSA’s data hoards — “maybe a niche kind of thing … a tool in the toolbox,” he said, though he added that there are easier ways to keep track of overseas terrorists and foreign intelligence agents.
Read moreIt's 2016 and now your internet-connected bathroom scales can be hacked
 Owners of Fitbit's Aria internet-connected smart scales are being advised to install a firmware patch following the discovery of critical security flaws. Tavis Ormandy of Google's Project Zero was credited with finding the vulnerabilities in the Wi-Fi cyber-scales.
Owners of Fitbit's Aria internet-connected smart scales are being advised to install a firmware patch following the discovery of critical security flaws. Tavis Ormandy of Google's Project Zero was credited with finding the vulnerabilities in the Wi-Fi cyber-scales.
While Fitbit isn't providing specific details on the nature of the flaws, it says that, in general, "critical" issues are those which "if exploited could allow attacker-supplied code to gain unrestricted access and potentially go undetected by the customer." Fitbit is right now pushing out the critical patch, and folks are advised to update their Aria scale firmware as soon as possible to prevent attacks.
Read moreNest is permanently disabling the Revolv smart home hub
 Nest is coming under fire following an announcement that Revolv, a smart home startup it acquired two years ago, would be permanently shutting off its product starting May 15th.
Nest is coming under fire following an announcement that Revolv, a smart home startup it acquired two years ago, would be permanently shutting off its product starting May 15th.
The decision, announced in a quiet note on Revolv's website in February, has gone largely unnoticed and is expected to impact a very small number of consumers. However, it does raise serious questions about the longevity of smart home gadgets. The devices are often costly pieces of hardware made by small startups that may drop support at any point after being scooped up by a larger technology company.
Read morePopular consumer IoT devices proved vulnerable
 During a two-month hackathon, security researchers from Bitdefender found vulnerabilities in four new IoT devices, of which only one has been partially fixed after the developer was notified.
During a two-month hackathon, security researchers from Bitdefender found vulnerabilities in four new IoT devices, of which only one has been partially fixed after the developer was notified.
Researchers found the first issue in the WeMo Switch, an Internet-accessible switch that lets users turn electronic devices in their home on and off. This device was using an insecure communications channel between the switch and the smartphone app that features no authentication. Everything is transmitted in cleartext, except for the device's password, which is encrypted with an easily breakable algorithm, using an encryption key derived from the device's ID and its MAC address.
Read moreSmart toys can be hacked to track children
 One of the most popular children's toys for Christmas contained vulnerabilities that, if exploited, would have given out personal details about a child. The security flaw in Fisher-Price's Smart Toy Bear meant access to a child's name, date of birth and gender could have been easily accessed.
One of the most popular children's toys for Christmas contained vulnerabilities that, if exploited, would have given out personal details about a child. The security flaw in Fisher-Price's Smart Toy Bear meant access to a child's name, date of birth and gender could have been easily accessed.
The researchers said the toy could also be hijacked to give a malicious actor control over account data and in-built functions. The bear, designed for three to eight-year-old children, was on Toys R Us' 2015 "Hot toy list." It is a teddy bear that can connect to the internet and offer personalised learning activities.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















