The NSA worked to “track down” bitcoin users, Snowden documents reveal
 Internet paranoiacs drawn to bitcoin have long indulged fantasies of American spies subverting the booming, controversial digital currency.
Internet paranoiacs drawn to bitcoin have long indulged fantasies of American spies subverting the booming, controversial digital currency.
Increasingly popular among get-rich-quick speculators, bitcoin started out as a high-minded project to make financial transactions public and mathematically verifiable — while also offering discretion. Governments, with a vested interest in controlling how money moves, would, some of bitcoin’s fierce advocates believed, naturally try and thwart the coming techno-libertarian financial order. It turns out the conspiracy theorists were onto something.
Read moreThe US spy hub in the heart of Australia
 A short drive south of Alice Springs, the second largest population center in Australia’s Northern Territory, there is a high-security compound, code-named “RAINFALL.”
A short drive south of Alice Springs, the second largest population center in Australia’s Northern Territory, there is a high-security compound, code-named “RAINFALL.”
The remote base is one of the most important covert surveillance sites in the eastern hemisphere. Hundreds of Australian and American employees come and go every day from Joint Defence Facility Pine Gap, as the base is formally known. The official “cover story,” as outlined in a secret U.S. intelligence document, is to “support the national security of both the U.S. and Australia. The [facility] contributes to verifying arms control and disarmament agreements and monitoring military developments.”
Read moreAmerican and British spy agencies targeted in-flight mobile phone use
 In the trove of documents provided by former National Security Agency contractor Edward Snowden is a treasure. It begins with a riddle: “What do the President of Pakistan, a cigar smuggler, an arms dealer, a counterterrorism target, and a combatting proliferation target have in common? They all used their everyday GSM phone during a flight.”
In the trove of documents provided by former National Security Agency contractor Edward Snowden is a treasure. It begins with a riddle: “What do the President of Pakistan, a cigar smuggler, an arms dealer, a counterterrorism target, and a combatting proliferation target have in common? They all used their everyday GSM phone during a flight.”
This riddle appeared in 2010 in SIDtoday, the internal newsletter of the NSA’s Signals Intelligence Directorate, or SID, and it was classified “top secret.” It announced the emergence of a new field of espionage that had not yet been explored: the interception of data from phone calls made on board civil aircraft.
Read moreCongressional report slams NSA leaker Edward Snowden
 A House intelligence committee report condemned Edward Snowden, saying the National Security Agency leaker is not a whistleblower and that the vast majority of the documents he stole were defense secrets that had nothing to do with privacy.
A House intelligence committee report condemned Edward Snowden, saying the National Security Agency leaker is not a whistleblower and that the vast majority of the documents he stole were defense secrets that had nothing to do with privacy.
The Republican-led committee released a three-page unclassified summary of its two-year bipartisan examination of how Snowden was able to remove more than 1.5 million classified documents from secure NSA networks, what the documents contained and the damage their removal caused to US national security. Snowden was an NSA contract employee when he leaked the documents to journalists.
Read moreThe NSA leak is real, Snowden documents confirm
 A hacking group calling itself the “ShadowBrokers” announced an auction for what it claimed were “cyber weapons” made by the NSA.
A hacking group calling itself the “ShadowBrokers” announced an auction for what it claimed were “cyber weapons” made by the NSA.
Based on documents provided by Edward Snowden, The Intercept can confirm that the arsenal contains authentic NSA software, part of a powerful constellation of tools used to covertly infect computers worldwide. The provenance of the code has been a matter of heated debate this week among cybersecurity experts, and while it remains unclear how the software leaked, one thing is now beyond speculation: The malware is covered with the NSA’s virtual fingerprints and clearly originates from the agency.
Read moreThe Intercept is broadening access to the Snowden archive
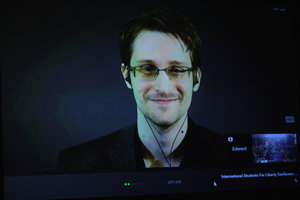 From the time we began reporting on the archive provided to us in Hong Kong by NSA whistleblower Edward Snowden, we sought to fulfil his two principal requests for how the materials should be handled.
From the time we began reporting on the archive provided to us in Hong Kong by NSA whistleblower Edward Snowden, we sought to fulfil his two principal requests for how the materials should be handled.
They should be released in conjunction with careful reporting that puts the documents in context and makes them digestible to the public, and that the welfare and reputations of innocent people should be safeguarded. As time has gone on, The Intercept has sought out new ways to get documents from the archive into the hands of the public, consistent with the public interest as originally conceived.
Read moreEU politicians want all criminal charges against Edward Snowden dropped
 Government-secret leaker Edward Snowden should be granted protection because his leaks were in defense of human rights, the European Parliament said.
Government-secret leaker Edward Snowden should be granted protection because his leaks were in defense of human rights, the European Parliament said.
The parliament passed a nonbinding resolution that called on European Union member states to protect Snowden from "extradition or rendition by third parties" because of "his status as whistle-blower and international human rights defender." The resolution also asks EU countries to drop any criminal charges against Snowden. The former contractor for the US National Security Agency sparked global debate about surveillance in the digital age when he leaked secret NSA documents to journalists in 2013.
Read moreEdward Snowden: Smartphones can be taken over
 Smartphone users can do "very little" to stop security services getting "total control" over their devices, Edward Snowden has said. The former intelligence contractor told that UK intelligence agency GCHQ had the power to hack into phones without their owners' knowledge.
Smartphone users can do "very little" to stop security services getting "total control" over their devices, Edward Snowden has said. The former intelligence contractor told that UK intelligence agency GCHQ had the power to hack into phones without their owners' knowledge.
GCHQ could gain access to a handset by sending it an encrypted text message and use it for such things as taking pictures and listening in. Mr Snowden did not suggest that either GCHQ or the NSA were interested in mass-monitoring of citizens' private communications but said both agencies had invested heavily in technology allowing them to hack smartphones.
Read moreThe Justice Department could strike deal with Edward Snowden
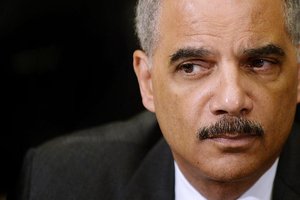 Former Attorney General Eric Holder said that a possibility exists for the Justice Department to cut a deal with former NSA contractor Edward Snowden that would allow him to return to the United States from Moscow.
Former Attorney General Eric Holder said that a possibility exists for the Justice Department to cut a deal with former NSA contractor Edward Snowden that would allow him to return to the United States from Moscow.
In an interview, Holder said we are in a different place as a result of the Snowden disclosures and that his actions spurred a necessary debate that prompted President Obama and Congress to change policies on the bulk collection of phone records of American citizens. Holder’s comments came as he began a new job as a private lawyer at Covington & Burling, where he worked before serving as the nation’s top law enforcement officer from February 2009 until last April.
Read moreNSA spied on non-American anti-virus companies
 British and American intelligence agencies have spied on anti-virus companies and probed their software for weaknesses, as the snoops sought to enhance their offensive surveillance techniques.
British and American intelligence agencies have spied on anti-virus companies and probed their software for weaknesses, as the snoops sought to enhance their offensive surveillance techniques.
This was predictable given previous revelations around the extensive hacking capabilities at GCHQ and the NSA, but for reasons not outlined in the leaks or by the agencies themselves, notable US and UK anti-virus providers were seemingly left untouched, despite being used across the world. Older versions of F-Secure also used the Kaspersky signature database, which contained lists of blacklisted malware.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















