User data plundering by Android and iOS apps is as rampant as you suspected
 Apps in both Google Play and the Apple App Store frequently send users' highly personal information to third parties, often with little or no notice.
Apps in both Google Play and the Apple App Store frequently send users' highly personal information to third parties, often with little or no notice.
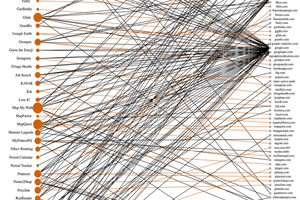
The researchers analyzed 55 of the most popular apps from each market and found that a significant percentage of them regularly provided Google, Apple, and other third parties with user e-mail addresses, names, and physical locations. Android apps sent potentially sensitive data to 3.1 third-party domains while the average iOS app sent it to 2.6 third-party domains. In some cases, health apps sent searches including words such as "herpes" and "interferon" to no fewer than five domains with no notification that it was happening.
Read moreXcodeGhost iOS malware strikes US enterprises
 A new variant of XcodeGhost has been discovered in the wild, leaving China behind to tackle US companies. In September this year, researchers discovered malware able to infect legitimate Apple iOS applications.
A new variant of XcodeGhost has been discovered in the wild, leaving China behind to tackle US companies. In September this year, researchers discovered malware able to infect legitimate Apple iOS applications.
The malicious code, known as XcodeGhost, lurked within at least 4000 legitimate iOS apps offered to the Chinese market, placing millions of users at risk. The malware was able to hijack apps through the developer toolkit Xcode, which is used to develop software for Apple's ecosystem. By adding the code to Xcode packages hosted on third-party websites rather than Apple domains, cybercriminals were able to bypass Apple's stringent security protocols.
Read moreResearchers find 256 iOS apps that collect users’ personal info
 Researchers said they've found more than 250 iOS apps that violate Apple's App Store privacy policy forbidding the gathering of e-mail addresses, installed apps, serial numbers, and other personally identifying information that can be used to track users.
Researchers said they've found more than 250 iOS apps that violate Apple's App Store privacy policy forbidding the gathering of e-mail addresses, installed apps, serial numbers, and other personally identifying information that can be used to track users.
The apps, which at most recent count totaled 256, are significant because they expose a lapse in Apple's vetting process for admitting titles into its highly curated App Store. They also represent an invasion of privacy to the one million people estimated to have downloaded the apps. The data gathering is so surreptitious that even the individual developers of the affected apps are unlikely to know about it.
Read moreApple's iOS App Store suffers major attack
 Apple Inc said it is cleaning up its iOS App Store to remove malicious iPhone and iPad programs identified in the first large-scale attack on the popular mobile software outlet.
Apple Inc said it is cleaning up its iOS App Store to remove malicious iPhone and iPad programs identified in the first large-scale attack on the popular mobile software outlet.
The company disclosed the effort after several cyber security firms reported finding a malicious program dubbed XcodeGhost that was embedded in hundreds of legitimate apps. It is the first reported case of large numbers of malicious software programs making their way past Apple's stringent app review process. Prior to this attack, a total of just five malicious apps had ever been found in the App Store, according to cyber security firm Palo Alto Networks Inc.
Read moreAirDrop bug in iOS and OSX allows hackers to install malware
 With the launch of iOS 9, Apple gave us an ultimate reason to upgrade our Apple devices to its new operating system. The latest iOS 9 includes a security update for a nasty bug that could be exploited to take full control of your iPhone or Macs, forcing most of the Apple users to download the latest update.
With the launch of iOS 9, Apple gave us an ultimate reason to upgrade our Apple devices to its new operating system. The latest iOS 9 includes a security update for a nasty bug that could be exploited to take full control of your iPhone or Macs, forcing most of the Apple users to download the latest update.
Australian security researcher Mark Dowd has disclosed a serious vulnerability in AirDrop, Apple's over-the-air file sharing service built into iOS and Mac OS X. The vulnerability allows anyone within the range of an AirDrop user to silently install a malicious app on a target Apple device by sending an AirDrop file which involves rebooting of the target device.
Read moreHow to remove KeyRaider malware that hacked iOS devices
 Jailbreaking your device may have got you the best of apps but after reading this you will know what a high price you could have to pay for the jailbreak. A malware named ‘KeyRaider’ has supposedly stolen user credentials of approximately 225K iPhone users.
Jailbreaking your device may have got you the best of apps but after reading this you will know what a high price you could have to pay for the jailbreak. A malware named ‘KeyRaider’ has supposedly stolen user credentials of approximately 225K iPhone users.
It has been given this name as it raids victims’ username and passwords, private keys and certificates. Figures say that KeyRaider malware has affected a large number of users in China and worldwide 17 more countries. Also, the origin of malware is suspected to be in China, as said in investigations conducted by Palo Alto Networks for reporting any suspicious tweaks on iPhones.
Read moreAuthentication flaw affects the PayPal mobile app
 Under specific conditions, PayPal can ask users to confirm their identity to prevent frauds. When users are asked to verify their identity, their account is not accessible and in order to unblock it PayPal request them to make a call or send an email to its service and complete the procedure.
Under specific conditions, PayPal can ask users to confirm their identity to prevent frauds. When users are asked to verify their identity, their account is not accessible and in order to unblock it PayPal request them to make a call or send an email to its service and complete the procedure.
Mejri explained that a vulnerability affecting the PayPal mobile app that can be exploited by attackers to access blocked accounts through repeated login attempts that leverage valid session cookies. The same trick could be used to bypass two-factor authentication process, once the attacker successfully accesses the account is it able to change its settings.
Read moreSmartwatch security fails to impress
 A research study conducted by Hewlett-Packard has found serious security issues in today's top smartwatch wearable devices. Smartwatches are part of the wearable device trend, which extends from medical devices and fitness trackers to acting as an extension of your smartphone.
A research study conducted by Hewlett-Packard has found serious security issues in today's top smartwatch wearable devices. Smartwatches are part of the wearable device trend, which extends from medical devices and fitness trackers to acting as an extension of your smartphone.
The Apple Watch and Android Wear are examples of popular wearable devices on the market which can pair with smartphones and allow you to view online notifications, send messages and control apps through either the small display or through voice control. Every one of the ten devices analyzed contained significant vulnerabilities.
Read moreBogus news app used to deliver spy tool
 Data stolen from Hacking Team continues to yield information about the company’s infiltration techniques. The latest find is a fake Android news app, which was used to install its flagship surveillance tool. The app is called “BeNews,” the same name as a long-shuttered news website.
Data stolen from Hacking Team continues to yield information about the company’s infiltration techniques. The latest find is a fake Android news app, which was used to install its flagship surveillance tool. The app is called “BeNews,” the same name as a long-shuttered news website.
Inside the app is a backdoor that appears to have been used to load the Android version of Hacking Team’s Remote Control System, also known as Galileo, a data-collecting tool the company sold to law enforcement and security agencies worldwide. That malicious component takes advantage of a local privilege escalation vulnerability.
Read moreHow tablets are changing education
 If you're writing poetry, write it. Don't type it in just because you can. The classroom is changing, as new technologies dramatically alter the learning for both teachers and students. And at the heart of this change is the tablet.
If you're writing poetry, write it. Don't type it in just because you can. The classroom is changing, as new technologies dramatically alter the learning for both teachers and students. And at the heart of this change is the tablet.
You might not think of the classroom as a key market for big companies such as Apple and Google. That's indicative of a vast worldwide market. Manufacturers understandably want their share – and it comes with some significant benefits to education too. What's been clear from looking at how the tablet is currently used in the classroom is that it's had a transformational effect.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















