Infected ATMs gave away millions of dollars
 What do you need in order to withdraw cash from an ATM? First, you need to have a debit or credit card, which acts as a key to your bank account. Second, you must know the PIN code associated with the card; otherwise, the bank wouldn’t approve the transaction.
What do you need in order to withdraw cash from an ATM? First, you need to have a debit or credit card, which acts as a key to your bank account. Second, you must know the PIN code associated with the card; otherwise, the bank wouldn’t approve the transaction.
Finally, you need to have some money in your account that you can withdraw. However, hackers do things differently: they don’t need cards, PIN codes or bank accounts to get money. In reality, all they need is an ATM with some cash in it and a special piece of software. Earlier this year, at the request of a financial institution, experts performed a forensic investigation into a cyber-criminal attack that targeted multiple ATMs in Eastern Europe.
Read moreTwitter sues the government of the USA
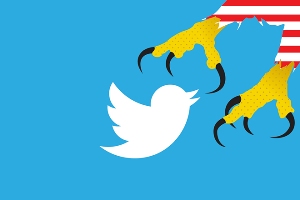 Twitter just sued the federal government over restrictions the government places on how much the company can disclose about surveillance requests it receives. For months, Twitter has tried to negotiate with the government to expand the kind of information that it and other companies are allowed to disclose. But it failed.
Twitter just sued the federal government over restrictions the government places on how much the company can disclose about surveillance requests it receives. For months, Twitter has tried to negotiate with the government to expand the kind of information that it and other companies are allowed to disclose. But it failed.
Twitter asserts in its suit that preventing the company from telling users how often the government submits national security requests for user data is a violation of the First Amendment. The move goes a step beyond a challenge filed by Google and other companies last year that also sought permission on First Amendment grounds to disclose how often it receives national security requests for data.
Read moreGermany handed law-protected private data
 Intelligence service BND failed to protect the private data of German citizens as it handed over internet data collected at a Frankfurt traffic hub to the US. During an ongoing parliamentary investigation into US National Security Service spying on German soil the secret documents were obtained from the federal government.
Intelligence service BND failed to protect the private data of German citizens as it handed over internet data collected at a Frankfurt traffic hub to the US. During an ongoing parliamentary investigation into US National Security Service spying on German soil the secret documents were obtained from the federal government.
So when last year in was revealed that the two intelligence services had been collaborating to collect communication data at the De-Cix internet exchange node in Frankfurt, the BND had to produce explanations. The German service said it had a filter running, which prevented data of German citizens from being collected and forwarded to the NSA.
Read moreCaution! Windows 10
 The reason why Microsoft has launched Windows Technical Preview is the collection of user feedback, in order to issue a new final Windows 10 version, which is planned to release in 2015.
The reason why Microsoft has launched Windows Technical Preview is the collection of user feedback, in order to issue a new final Windows 10 version, which is planned to release in 2015.
Windows 10 beta version asks to register in Windows Insider Program and then a user must send the reviews about the new system at a specific time. But as it turned out they are not interested in your mind only. If you read the rules of Windows Insider Program attentively, we can see that Microsoft is interested not only in your point of view. With the help of Windows Technical Preview, Microsoft collects information about...
Read moreYour mail is the key to everything
 Not all accounts are created equal. It’s only natural that you would care less about an ESPN Fantasy Football account than you would care about your online banking or PayPal account.
Not all accounts are created equal. It’s only natural that you would care less about an ESPN Fantasy Football account than you would care about your online banking or PayPal account.
Anyone who spends even a little time thinking about security is careful to use a strong password and proceed with caution when accessing a service related to personal finance. However, a lot of users are also relatively careless about their primary webmail account, which often serves as a master key to all other accounts. Think about it: whenever you set up nearly any online account, you’re prompted to enter a primary webmail account. There are a number of reasons for this.
Read moreDo not cover the pop-up windows!
 Web surfing is one of the most popular kinds of using the Internet. Every day we are surfing the web: view the news, listen to the music and check e-mail. However, this service puts at risk the information stored on your computer.
Web surfing is one of the most popular kinds of using the Internet. Every day we are surfing the web: view the news, listen to the music and check e-mail. However, this service puts at risk the information stored on your computer.
During web surfing everyone can get to the site from which you can upload virus or an attacker can trick to get personal information. A digital certificate may be threat signal. Let's look at what it is a digital certificate and how it provides safety when surfing the web. There are many digital certificates and each serves for their own purposes. The most common type of certificates is SSL certificates.
Read moreYou are tracked, even now
 The American company suggests service that can track subscriders all over the world, without users or operators knowledge. On the Internet, there are so many services that can monitor the location of the user, but this case is one of the first, when such services are offered quite officially and globally.
The American company suggests service that can track subscriders all over the world, without users or operators knowledge. On the Internet, there are so many services that can monitor the location of the user, but this case is one of the first, when such services are offered quite officially and globally.
How can it be? When it comes to mobile surveillance, it is believed that this requires technologies that are used by special services only. In reality, everything is easier. The telecommunication network contains many small systems of different technical level, and the level of the network security is often determined by the level of the weakest link.
Read moreIntelligence services against journalists. What will the law say?
 Australia’s lower house of parliament has passed the first in a series of counter-terrorism amendments toughening the country’s national security law. The new legislation could see journalists jailed for reporting on related matters.
Australia’s lower house of parliament has passed the first in a series of counter-terrorism amendments toughening the country’s national security law. The new legislation could see journalists jailed for reporting on related matters.
National Security Amendments Bill says a person who discloses information relating to a special intelligence operation may face from five to 10 years behind bars. Copying, transcribing or retaining records of the Australian Security Intelligence Organisation is also outlawed, which is seen as a measure taken in the wake of Edward Snowden’s leaks of documents on the US’s National Security Agency.
Read moreWristband gives shocks to break bad habits
 A startup called Pavlok has launched a crowdfunding campaign for a wristband that electroshocks its owner to encourage him or her to exercise, eat healthily, wake up on time and stop procrastinating.
A startup called Pavlok has launched a crowdfunding campaign for a wristband that electroshocks its owner to encourage him or her to exercise, eat healthily, wake up on time and stop procrastinating.
Pavlok can help with setting goals like going to the gym regularly or giving up social networks, with the wristband electrically shocking the owner, should he/she fail to stick to the task. Pavlok can shock the person via small metal terminals, and the wave might jolt, but supposedly isn’t hazardous. Amid the most notable Pavlok’s functions, is the alarm which goes off gently with noises and vibrations, waking the owner up, but if he or she continues to sleep, a shock wave will be sent.
Read moreWhat is the Bash vulnerability and why it affects everyone
 In what seems like the most impactful security vulnerability since the OpenSSL Heartbleed affair, a new Internet-wide bug emerged this week in the Bourne again shell (Bash).
In what seems like the most impactful security vulnerability since the OpenSSL Heartbleed affair, a new Internet-wide bug emerged this week in the Bourne again shell (Bash).
While its true severity remains unknown, the Bash vulnerability (also known as “shell shock”) is being talked about everywhere, and you may have even seen your local news anchors discussing the story in front of a green-screen covered in fast-scrolling computer code on last night’s evening news. Bash is present in a very large number of Web-servers and in-home appliances. What is Bash?
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















