Holes in Progressive Dongle could lead to car hacks
 A device that a popular car insurance company sends to customers to keep track of their driving and reduce their rate may be insecure and could be used to take control of a user’s vehicles.
A device that a popular car insurance company sends to customers to keep track of their driving and reduce their rate may be insecure and could be used to take control of a user’s vehicles.
The device, already in use in two million cars across the USA, is designed to capture users’ driving habits in order to get them a better rate on car insurance. Thuen took Progressive up on an offer the company runs where they can offer anyone who wants to try out the device a free trial. After reverse engineering the device and plugging it into his Toyota Tundra, Thuen discovered the dongle not only fails to authenticate to the cellular network but also fails to encrypt its traffic.
Read moreCTB-Locker is the newest crypto malware
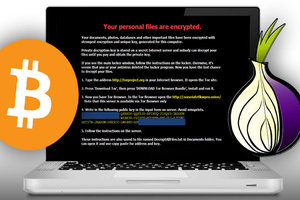 From late 2013 through the first half of 2014, CryptoLocker malware was a major concern for many businesses and individuals. The FBI was able to successfully disrupt CryptoLocker, along with Game Over Zeus, but according to the figures in their legal complaint against Evgeniy Bogachev, not before his malware had encrypted a lot of computers.
From late 2013 through the first half of 2014, CryptoLocker malware was a major concern for many businesses and individuals. The FBI was able to successfully disrupt CryptoLocker, along with Game Over Zeus, but according to the figures in their legal complaint against Evgeniy Bogachev, not before his malware had encrypted a lot of computers.
The second major Crypto Malware was CryptoWall. In Malcovery's 3rd Quarter malware report, there were documented 24 separate spam campaigns that resulted in CryptoWall infections. Today we may have seen the beginning of the Next Wave of Crypto Malware being delivered by spam.
Read moreDating app makes it easy to stalk
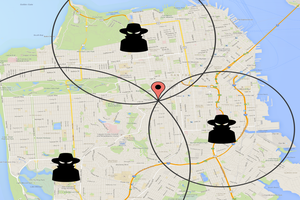 Location sharing allows user whearabouts to be tracked around the clock. Mobile dating apps have revolutionized the pursuit of love and sex by allowing people not only to find like-minded mates but to identify those who are literally right next door, or even in the same bar, at any given time.
Location sharing allows user whearabouts to be tracked around the clock. Mobile dating apps have revolutionized the pursuit of love and sex by allowing people not only to find like-minded mates but to identify those who are literally right next door, or even in the same bar, at any given time.
That convenience is a double-edge sword, warn researchers. To prove their point, they exploited weaknesses in Grindr, a dating app with more than five million monthly users, to identify users and construct detailed histories of their movements. The proof-of-concept attack worked because of weaknesses identified five months ago.
Read moreUnited Kingdom: We have to spy on innocent people in order to stop terrorism
 Former head of Secret Intelligence Service uses first speech since leaving to say there cannot be 'no-go areas' on internet as he warns of 'all but inevitable' attack on UK. The British security services will not be able to prevent terrorism unless they monitor the internet traffic of innocent people, the former head of MI6 has said.
Former head of Secret Intelligence Service uses first speech since leaving to say there cannot be 'no-go areas' on internet as he warns of 'all but inevitable' attack on UK. The British security services will not be able to prevent terrorism unless they monitor the internet traffic of innocent people, the former head of MI6 has said.
He said the revelations the former CIA contractor had captured the public's attention because they had not been properly informed about the security services' online surveillance capabilities. Snowden, who revealed top secret details about online monitoring, had "thrown a massive rock in the pool", but he admitted that the move had led to a public debate.
Read moreGoogle in talks to invest money in SpaceX
 Google could soon make an investment in SpaceX. The goal of the deal is to support the creation of a satellite-based Internet system that would bring Internet access to rural areas not yet online. Google's investment would value Elon Musk's company a lot of money.
Google could soon make an investment in SpaceX. The goal of the deal is to support the creation of a satellite-based Internet system that would bring Internet access to rural areas not yet online. Google's investment would value Elon Musk's company a lot of money.
The lower satellites would make for a speedier Internet service, with less distance for electromagnetic signals to travel. The lag in current satellite systems makes applications such as Skype, online gaming, and other cloud-based services tough to use. Musk’s service would, in theory, rival fiber optic cables on land while also making the Internet available to remote and poor regions that don’t have access.
Read moreDemand for cyber insurance skyrockets
 Demand for cybersecurity insurance is booming as a string of high-profile hacks and data breaches spurs explosive growth in what has suddenly become a $2 billion industry.
Demand for cybersecurity insurance is booming as a string of high-profile hacks and data breaches spurs explosive growth in what has suddenly become a $2 billion industry.
The recent cyberattack on Sony Pictures Entertainment, which brought losses and public embarrassment to the company, has only accelerated years of steady growth that is expected to expand into new sectors of the economy in 2015. Major data breaches, which collectively exposed the information of hundreds of millions of consumers and cost the companies millions of dollars, have heightened businesses’ concerns that they could be next.
Read moreCanadian new rules should cut malware
 All you wanted to do was download a game from the Internet, and the next thing you knew, your browser homepage had changed, an unwanted toolbar appeared, and you found yourself plagued by annoying pop-up ads that danced around your screen.
All you wanted to do was download a game from the Internet, and the next thing you knew, your browser homepage had changed, an unwanted toolbar appeared, and you found yourself plagued by annoying pop-up ads that danced around your screen.
Such experiences should be less of a problem for Canadians thanks to new rules from the Canadian Radio-television and Telecommunications Commission which came into effect last week. The new guidelines make it illegal to install programs on an individual’s computing device without the operator’s consent. The rules are designed to protect Canadians from damaging and deceptive forms of spam.
Read moreCan you be sure in a smart TV?
 With the continuous advancements made in technology, our online experiences are becoming more streamlined and seemingly user friendly.
With the continuous advancements made in technology, our online experiences are becoming more streamlined and seemingly user friendly.
We no longer require stationary desktop computers to access the Internet, but instead can reach the web through our laptops, smartphones, tablets and now, televisions. Smart TVs are one of the latest additions to the family of fun gadgets millions of people have their eyes on, but are they secure? In January 2014, there was a deeper dive into the safety of smart TVs by inspecting the televisions of major manufactures. Journalists were able to crack into the devices by messing with their SSL certificates.
Read moreFacebook hiring spree hints at ambitions in virtual reality and beyond
 Virtual reality goggles, drones and data centers are all driving a hiring spree at Facebook that is set to swell its ranks as much as 14 percent in the near term, according to a review of job listings on the company's website.
Virtual reality goggles, drones and data centers are all driving a hiring spree at Facebook that is set to swell its ranks as much as 14 percent in the near term, according to a review of job listings on the company's website.
The Internet social networking company aims to add new employees, the outgrowth of aggressive investments that executives have said will define the coming year. The market for virtual reality headsets is still nascent. But if virtual reality takes off for entertainment, gaming, communications or computing, Facebook could be at the center of the new platform with Oculus. Facebook’s ambitious effort to build its own satellites and drones capable of delivering Internet service.
Read moreFake Wi-Fi network fools top Swedish security experts
 A leading internet activist has tricked Swedish security and defense experts into joining an open Wi-Fi network he set up to challenge digital surveillance. He discovered some of them were using Skype and looking at eBay while working.
A leading internet activist has tricked Swedish security and defense experts into joining an open Wi-Fi network he set up to challenge digital surveillance. He discovered some of them were using Skype and looking at eBay while working.
The hacker created the Wi-Fi network at a conference earlier this week. Given the network was not encrypted, he managed to monitor the sites people visited, along with emails and text messages of up to 100 delegates, politicians, journalists and security experts among them. The security establishment was in Sälen pushing for more surveillance, but then leading figures go and log on to an unsecure Wi-Fi network.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















