Kmart, Dairy Queen see payment-card data stolen
 The retailer and the fast-food chain are the latest businesses to report that hackers accessed payment-card data by breaching their systems. Kmart and Dairy Queen customers should check their credit- and debit-card statements for shady activity.
The retailer and the fast-food chain are the latest businesses to report that hackers accessed payment-card data by breaching their systems. Kmart and Dairy Queen customers should check their credit- and debit-card statements for shady activity.
That's because the retailer and the fast-food chain have become the latest businesses to reveal that their payment systems were hacked. The breach has been plugged and the malware removed, James said. Dairy Queen similarly said there was no indication that any other personal information was affected and that the security hole had been addressed.
Read moreUK councils sell constituents’ personal data for junk mail
 Junk mail is a pain for all of us, but in Britain, what's really bugging people is that it's being so personally targeted into their homes. What's more, marketing firms are buying up names and addresses from a place most would assume holds their details safely under lock and key.
Junk mail is a pain for all of us, but in Britain, what's really bugging people is that it's being so personally targeted into their homes. What's more, marketing firms are buying up names and addresses from a place most would assume holds their details safely under lock and key.
Getting the post, delivered these days is less by letters from France or even bills it now a direct advertising offensive to your own front door. Each year, individuals and private firms receive 12 billion of advertising letters, that is, more than 400 for the average English family. So, who is selling your name and address?
Read moreYouTube has potentially infected over 100,000 users during the past 30 days
 YouTube has become a daily habit for millions all over the world, but it looks like there has been some malicious activity on the website -- which may have affected more than 100,000 users over a 30 day period.
YouTube has become a daily habit for millions all over the world, but it looks like there has been some malicious activity on the website -- which may have affected more than 100,000 users over a 30 day period.
According to Trend Micro, they have been monitoring the activity on YouTube over the past couple of months and have found that the attack comes in the form of ads that are present on the site. While the ads themselves have no malicious content, the issue seems to occur when the ad is clicked. Although these ads should be monitored and screened by YouTube, some have seemed to slip through the cracks, redirecting to malicious websites that could cause infections.
Read moreMalicious worm seeks vulnerable home data stores
 A malicious worm that can roam the net seeking data stored on insecure hardware has been created by a security researcher. The proof-of-concept worm was written to illustrate how vulnerable such data stores are to malicious attack.
A malicious worm that can roam the net seeking data stored on insecure hardware has been created by a security researcher. The proof-of-concept worm was written to illustrate how vulnerable such data stores are to malicious attack.
Many people connect these devices to a home router to give family members a place to put important files such as photos and films or to act as a back-up for other gadgets. Some home routers can also connect to hard drives to turn them into an NAS-type device. Many of these, if exploited, would give an attacker complete control over a device letting them plunder the data on it.
Read moreHurricane Panda hackers exploit Zero-day for 5 months
 A highly advanced adversary dubbed Hurricane Panda is targeting major infrastructure companies with a zero-day exploit—and it has been since last spring. The timestamp of the attack suggests that the vulnerability has been actively exploited in the wild for at least five months.
A highly advanced adversary dubbed Hurricane Panda is targeting major infrastructure companies with a zero-day exploit—and it has been since last spring. The timestamp of the attack suggests that the vulnerability has been actively exploited in the wild for at least five months.
CrowdStrike first detected suspicious activity on a 64-bit Windows Server 2008 R2 machine that was attributed to a compromise by the group. It uncovered that the attacks begin with compromising web servers and deploying Chopper webshells, and then escalating privileges using the newly discovered Local Privilege Escalation tool, which exploits a previously unknown vulnerability.
Read moreNSA Sentry Eagle placed spies in private companies
 The National Security Agency has sent spies into private companies in a bid to compromise networks from within, according to documents leaked by Edward Snowden.
The National Security Agency has sent spies into private companies in a bid to compromise networks from within, according to documents leaked by Edward Snowden.
Agents sent in by the NSA targeted global communications firms under a highly classified 'core secrets' program dubbed Sentry Eagle previously known only to a handful of officials. The documents indicate operatives in the core secrets program worked in concert with companies to weaken encryption and spent hundreds of millions of dollars to break security mechanisms. The document listed facts ranging from unclassified to top secret necessitating "extraordinary protection".
Read morePOODLE bites: exploiting the SSL 3.0 fallback
 There are details of a vulnerability in the design of SSL version 3.0. This vulnerability allows the plaintext of secure connections to be calculated by a network attacker.
There are details of a vulnerability in the design of SSL version 3.0. This vulnerability allows the plaintext of secure connections to be calculated by a network attacker.
SSL 3.0 is nearly 15 years old, but support for it remains widespread. Most importantly, nearly all browsers support it and, in order to work around bugs in HTTPS servers, browsers will retry failed connections with older protocol versions, including SSL 3.0. Because a network attacker can cause connection failures, they can trigger the use of SSL 3.0 and then exploit this issue. Disabling SSL 3.0 support, or CBC-mode ciphers with SSL 3.0, is sufficient to mitigate this issue, but presents significant compatibility problems, even today.
Read moreRussian Sandworm Hack Has Been Spying on Foreign Governments
 A cyberespionage campaign believed to be based in Russia has been targeting government leaders and institutions for nearly five years, according to researchers with iSight Partners who have examined code used in the attacks.
A cyberespionage campaign believed to be based in Russia has been targeting government leaders and institutions for nearly five years, according to researchers with iSight Partners who have examined code used in the attacks.
The campaign, dubbed “Sandworm” is believed to have been running since 2009, and used a wide-reaching zero-day exploit uncovered by the researchers that affects nearly every version of the Windows operating system released since Windows Vista. The attackers also targeted attendees of this year’s GlobSec conference, a high-level national security gathering that attracts foreign ministers and other top leaders.
Read moreNew mobile trojan as Tic-tac-toe game targets Android devices
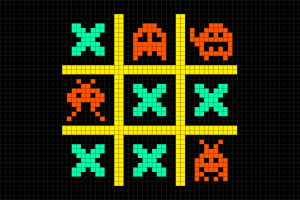 A Tic-tac-toe game is actually a new mobile trojan – detected as Trojan-Spy,AndroidOS.Gomal.a, or Gomal – targeting Android devices. Gomal is capable of recording audio from the microphone, stealing incoming SMS messages, stealing device information such as cell phone number.
A Tic-tac-toe game is actually a new mobile trojan – detected as Trojan-Spy,AndroidOS.Gomal.a, or Gomal – targeting Android devices. Gomal is capable of recording audio from the microphone, stealing incoming SMS messages, stealing device information such as cell phone number.
Obtaining root privileges, dumping memory regions of some processes in order to obtain sensitive data, and stealing data from the device log. Gomal uses many techniques initially incorporated into Windows trojans, the post indicates. Packaging trojans in mobile games is common – there are multiple cases of attackers doing so using the popular games.
Read moreAndroid's Cyanogenmod open to MitM attacks
 More than 10 million users of the popular Cyanogen build of Android are exposed to man-in-the-middle attacks thanks to reuse of vulnerable sample code. The zero day vulnerability makes it possible to target any browser used on the popular Android distribution.
More than 10 million users of the popular Cyanogen build of Android are exposed to man-in-the-middle attacks thanks to reuse of vulnerable sample code. The zero day vulnerability makes it possible to target any browser used on the popular Android distribution.
A security researcher who works for a top-tier vendor, but asked Vulture South not to use his name, said Cyanogenmod developers among many others had taken Oracle's sample code for Java 1.5 for parsing certificates to obtain hostnames - which is vulnerable to an older bug - and implemented it. Cyanogenmod developers have been contacted about the flaw.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















